23andMe Suffers Data Breach
October 20, 2023
Introduction
One of the latest companies to be victim of a data breach, 23andMe, has had their data shared on various dark web marketplaces as well as Telegram. Interestingly, the data from this breach has partly been shared in response to the conflict in Israel and Gaza with one of the sharers of the data citing this as a reason for sharing some of this information.
23andMe is a genealogy company which as well as providing ancestry services uses DNA to identify where individuals’ ancestors are likely to have come from. They also provide details of individuals’ health and genetic predispositions. The leak purports to contain full names, year of birth, location, as well as DNA markers and locations they may have links to.
23andMe has indicated that the data was obtained as part of a credential stuffing attack, and that there has been no evidence of a security breach on their IT systems.

The First Leak is Shared
The first identified mention of a leak of 23andMe data was on the marketplace Hydra Market on August 11, 2023. The post was made by a user using the alias Dazhbog. In the post he claimed to have access to 10M DNA data that he was providing for sale. He claimed that the file size was over 300TB and that the data would only be sold once, the asking price for the data was $50 million.
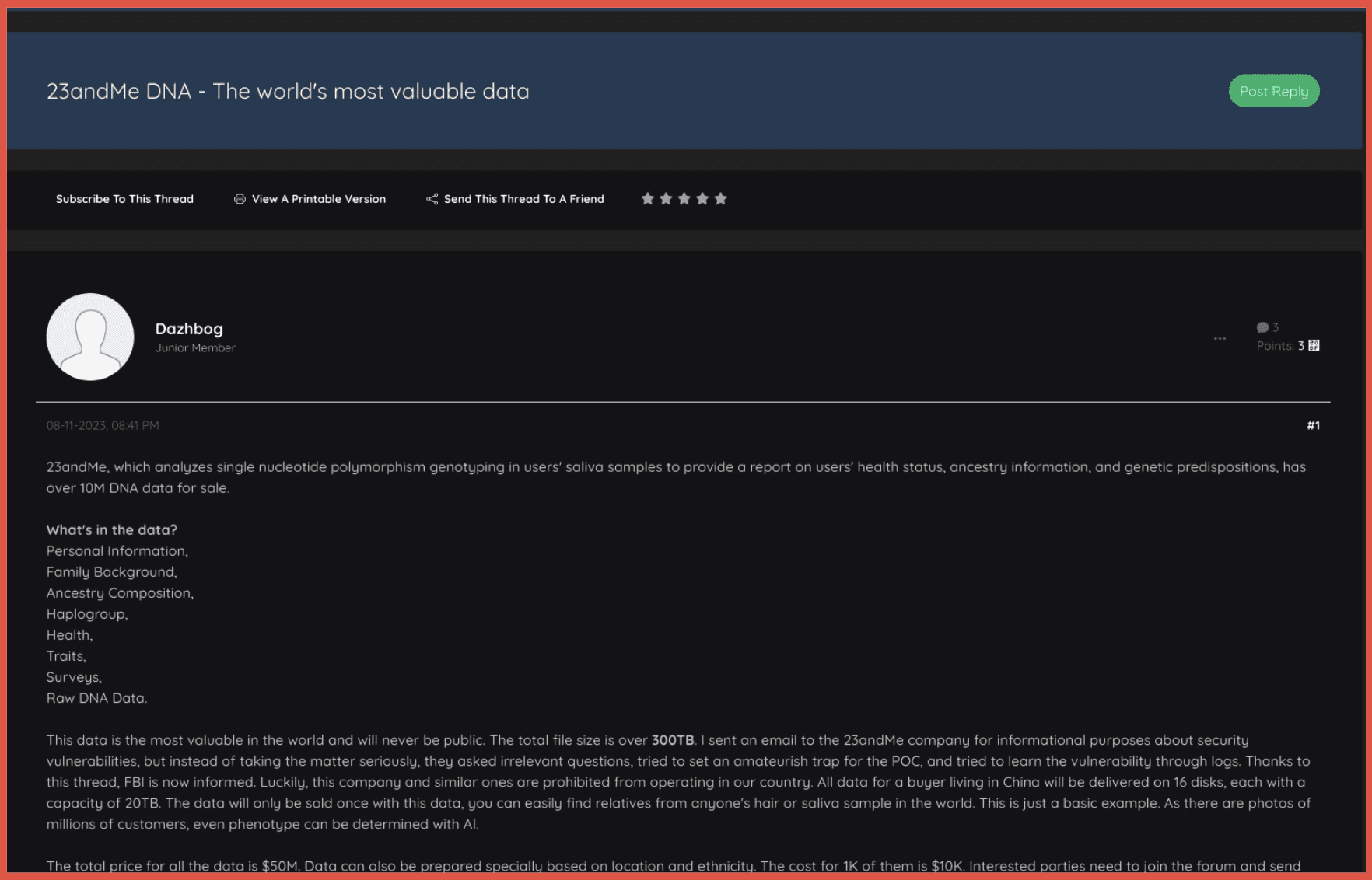
The seller also indicated that they would be open to selling the data in parts, based on location and ethnicity. This was priced at $10k per 1k of data.
Although it is unclear who is behind the username Dazhbog, they did indicate that 23andMe was not allowed to operate in their country. They also gave specific instructions for how buyers in China would be able to receive the data – in hard copy. The user first registered on Hydra Market on August 10, one day before the original post was made.
The poster provides details of how the information was obtained – claiming it was obtained through an API service used by pharmaceutical companies.
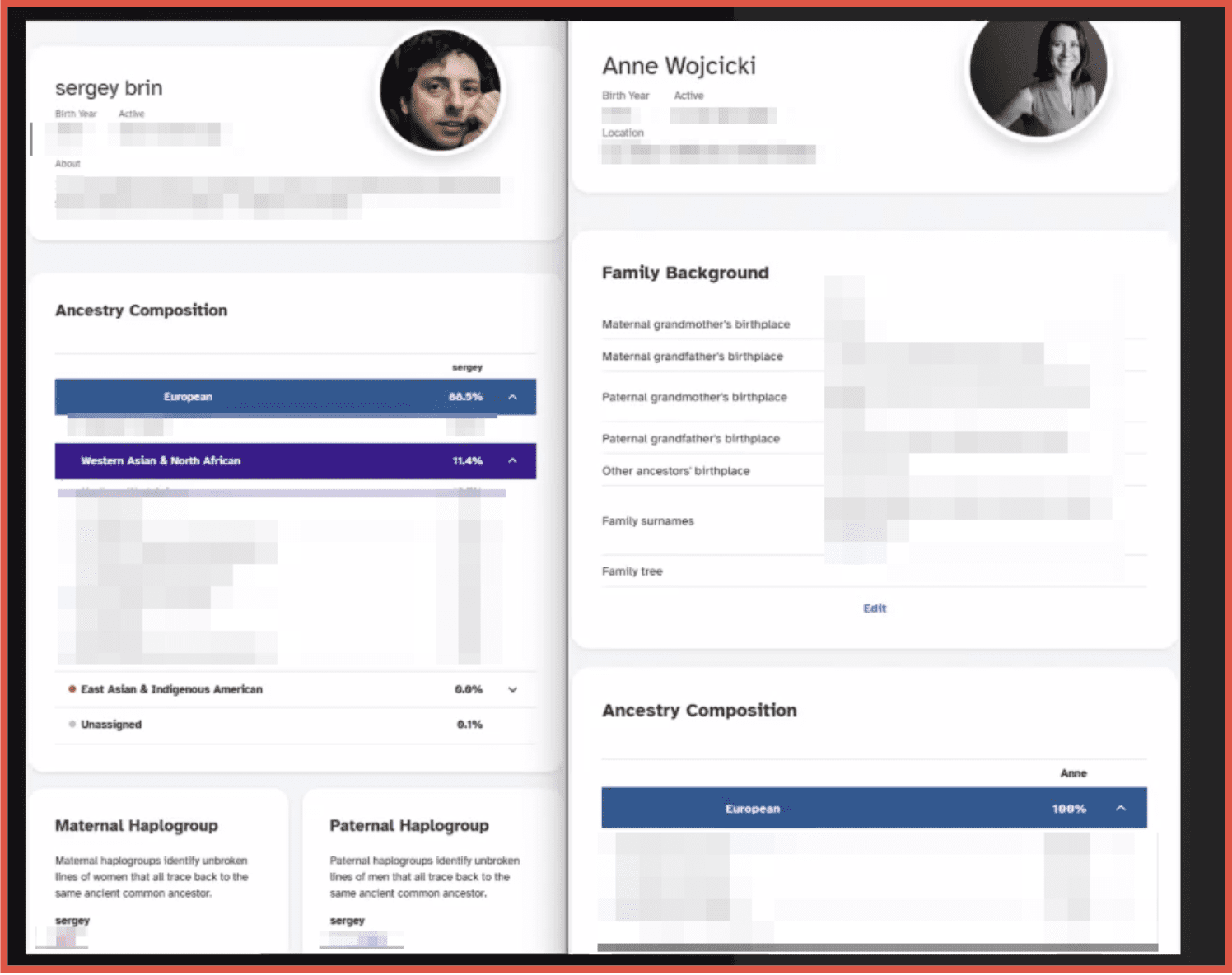
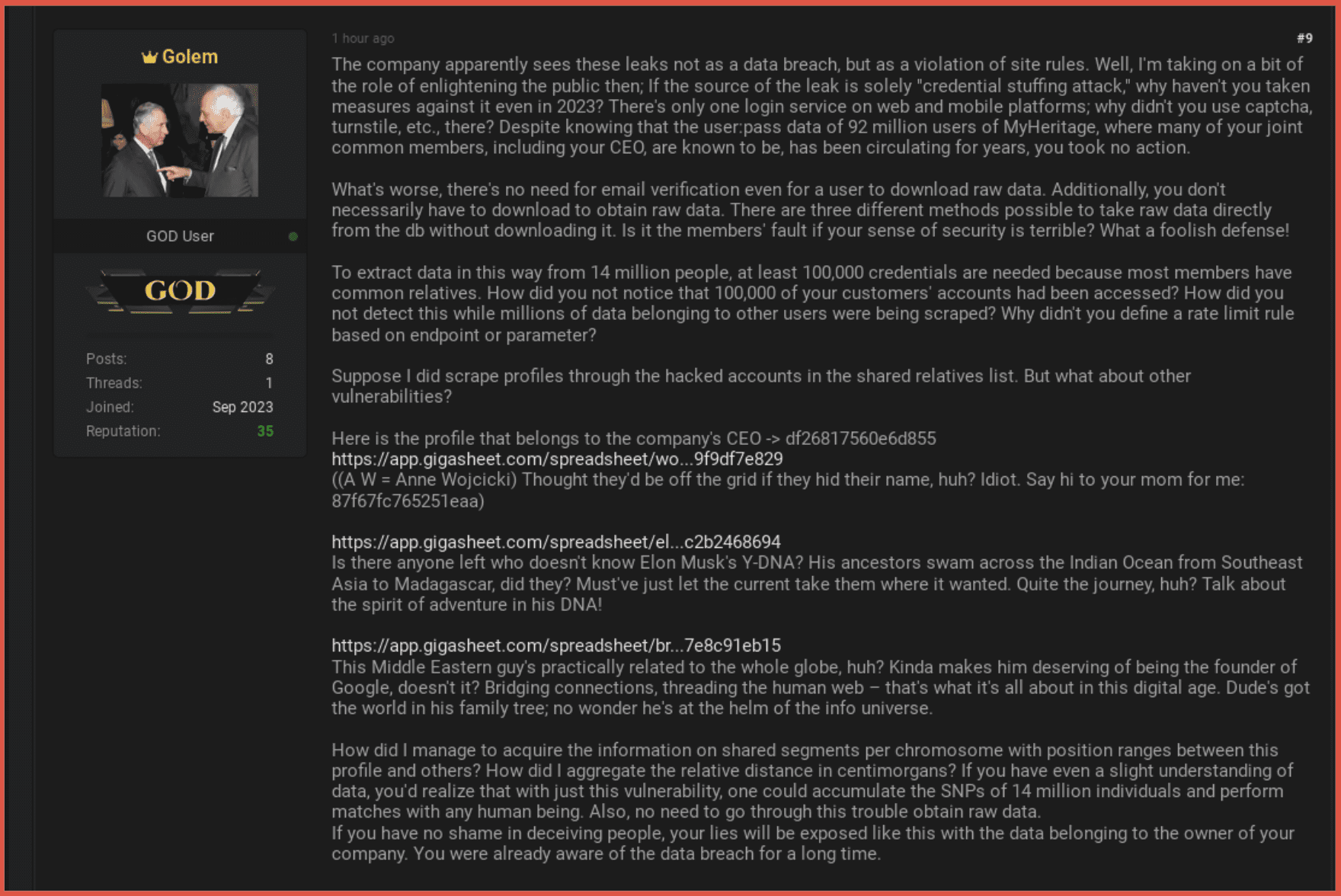
As proof of the data obtained, links we provided for Sergey Brin – Co-founder of Google and Anne Wojcicki – CEO of 23andMe. Images were also shown.
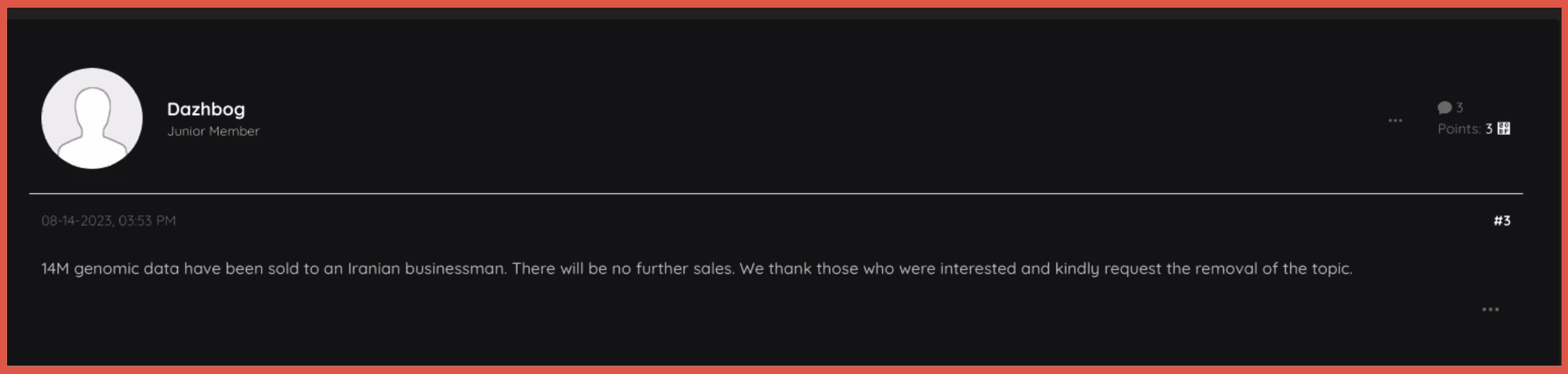
A post was made by the original poster on August 14 claiming that the full data had been sold to an Iranian individual and requested that the original post be removed. The post is still active, but the original poster has made no new posts since this time. Their profile also indicates that they have not been active since this time. This would suggest that this account was created specifically to share this leak.
Parts of the Leak Emerge
Once the original leak had been shared, several other leaks emerged on the forum Breached Forum which is known for providing leaked data.
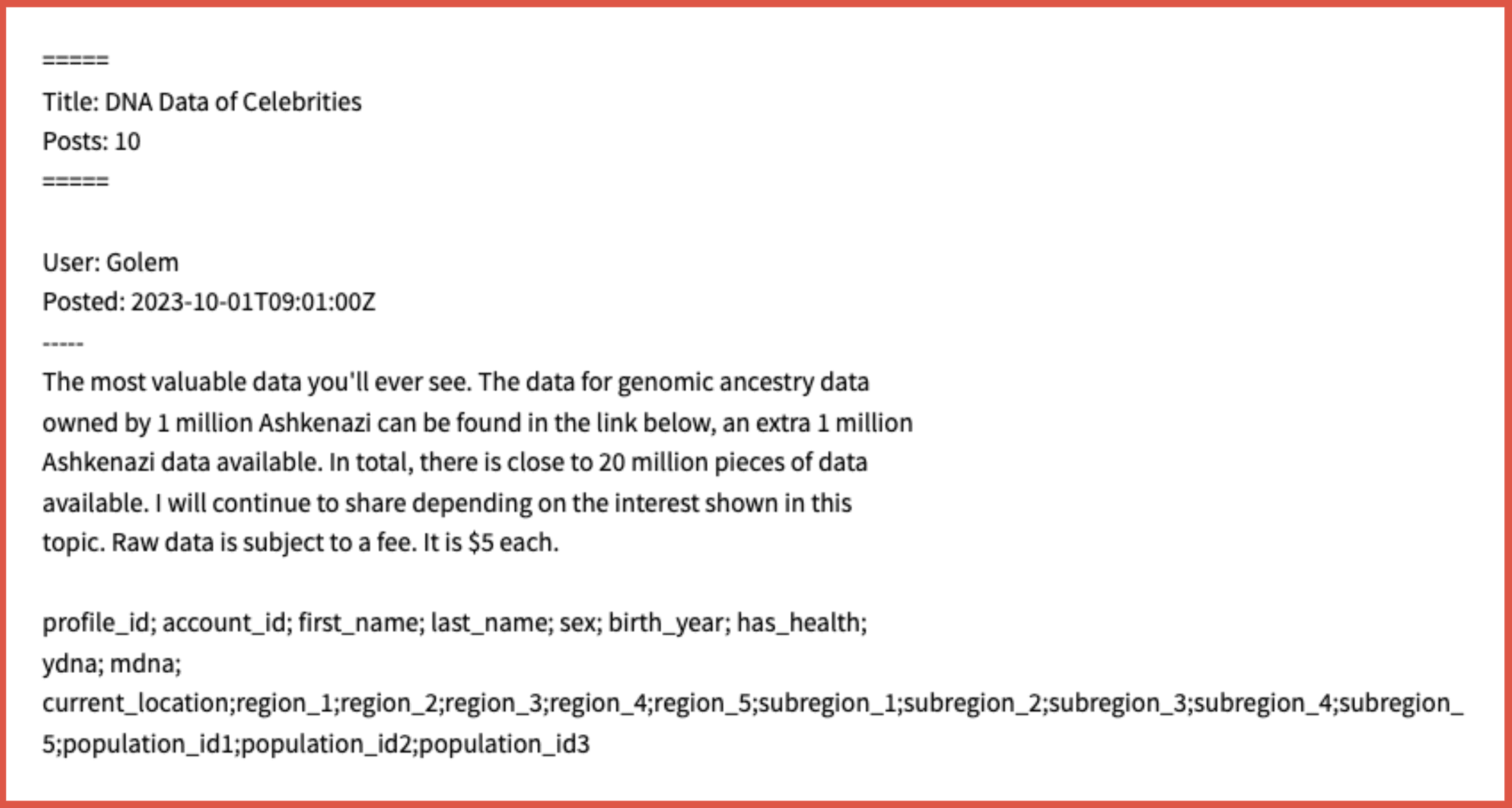
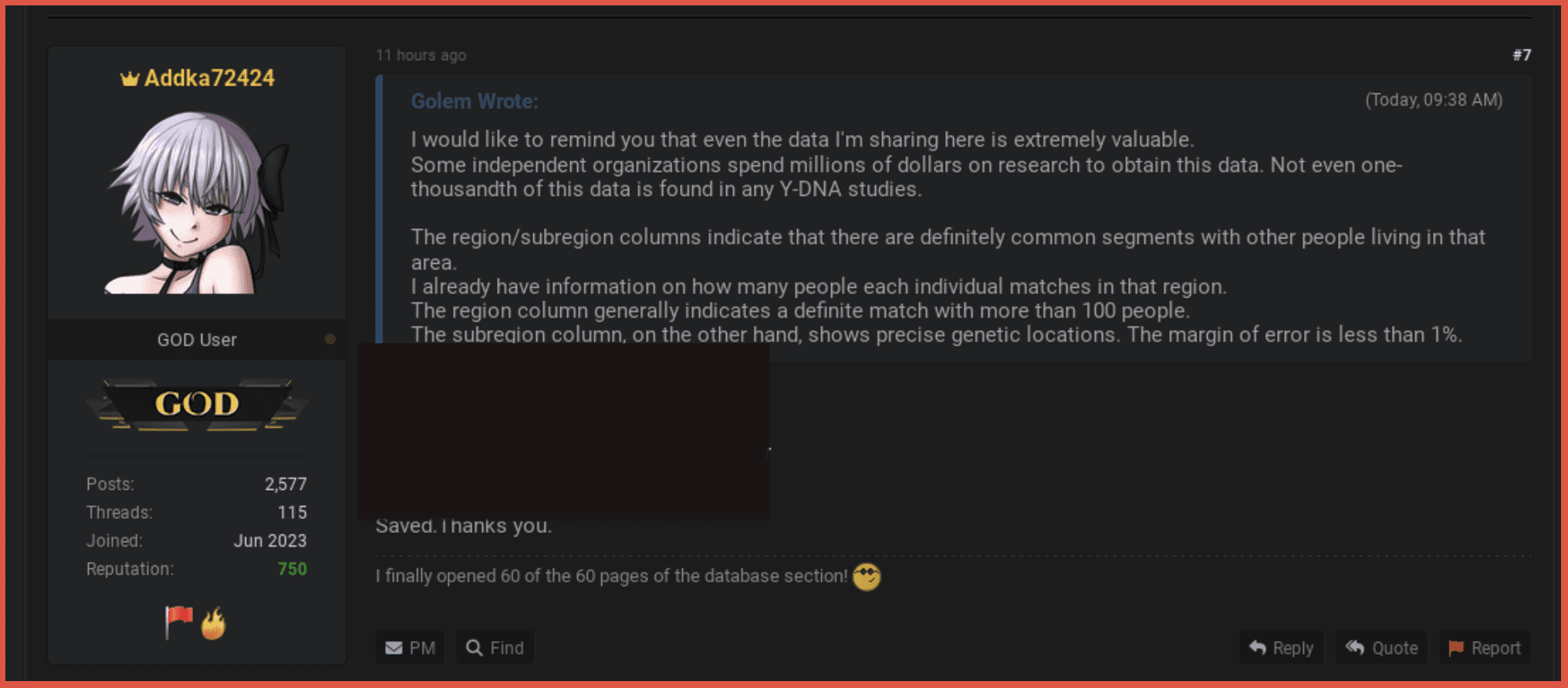
The user Golem posted on October 1, 2023, a link to data which they claimed was DNA of Celebrities. The description of the leak indicates that it will provide details of 1 million Ashkenazi Jews. The poster claims there is more data to come, and that raw data can be provided for a fee.
Although this post was not available for long, other users began to share the information – providing multiple leaks. A Telegram account was also created with the sole purpose of sharing this leak shortly after the attack on Israel on 7 October.
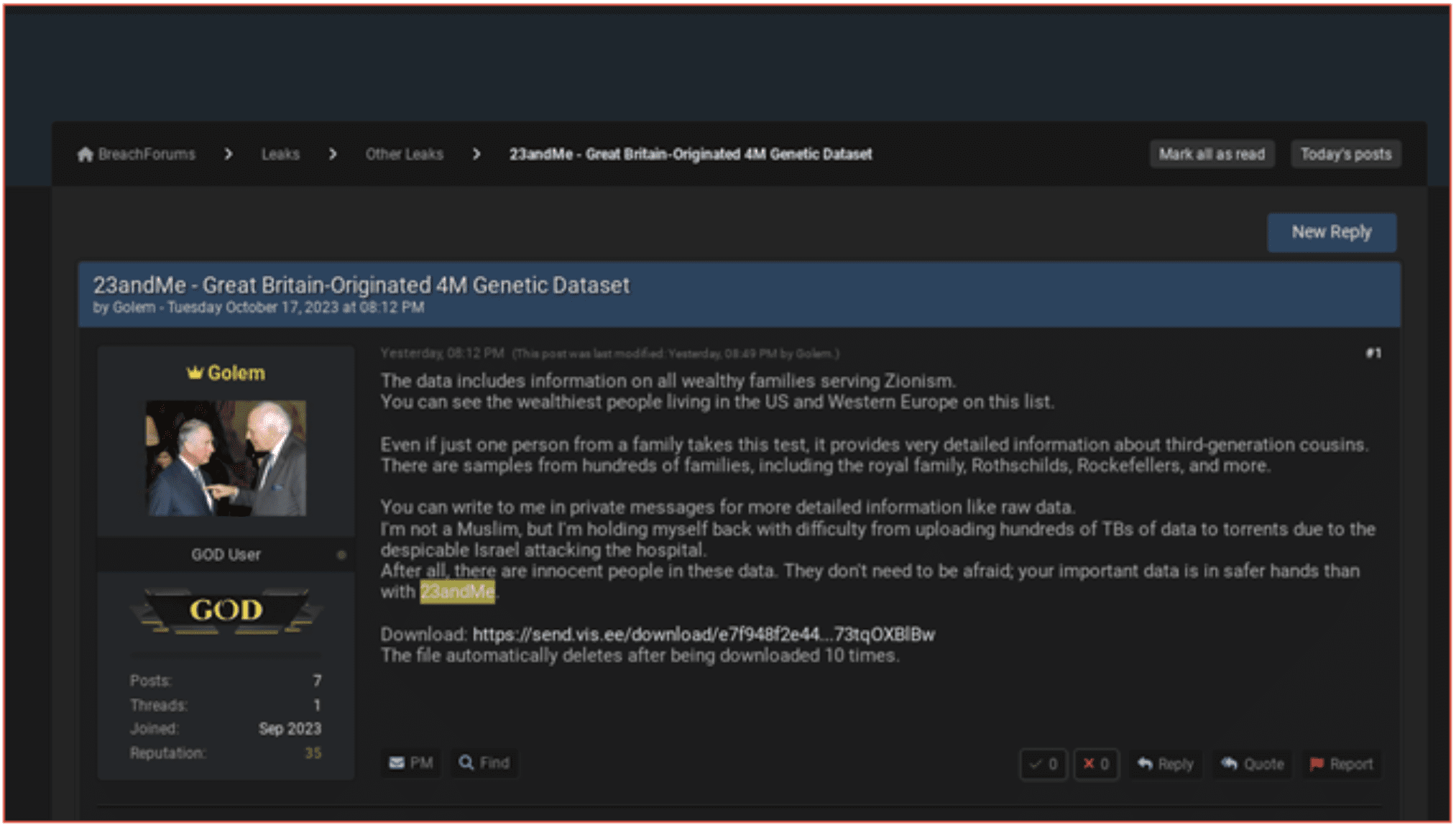
A further post was made on October 17 providing a leak claiming to provide details of individuals from the UK or with links to the UK. The poster, Golem stated that this information was being released in response to what they claimed was “the bombing of a hospital by the Israelis.”
Again, the leaks were not available for long, but the information was posted by other users. This also included links to German and Chinese data.
Golem also made a post, in response to 23 and Me claiming this was not a data leak, providing details of how the information was accessed. They also give examples which were provided in the original post. It is unclear if Golem has any links to Dazhbog or how they obtained this information.
Conclusion
The leak of this data provides threat actors with information relating to individuals’ personal ancestry and their DNA and could pose threats to those individuals, particularly those in the public eye. Some of the releases of this leak highlights how data leaks are being used as part of the conflict in Israel and Gaza with data being weaponized as part of the conflict. It also underlines the way that leaks are shared on the dark web, often first being made available for sale and then being shared for free. DarkOwl never pays for data from the dark web.
It is currently unclear if all the data obtained as part of this attack will be made available. DarkOwl analysts will continue to monitor for any further posts. All data that has been made freely available thus far is available via DarkOwl Vision.
Stay up to date with the latest research from the DarkOwl analyst team and subscribe to our email newsletter.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















