BULLETIN: Latest REvil Victims Suggest Ransomware Targeting is Less Indiscriminate Than Previously Thought
Late last week, DarkOwl analysts observed the REvil ransomware as a service (Raas) cyber-criminal organization publicly announce its latest victims of their ransomware operations on their darknet onion service, some of which have direct associations to western militaries and governments.
Previous assessments have suggested the targets selected by REvil and similar RaaS groups were completely random and indiscriminate. Without directly naming or shaming the companies who fell victim to REvil’s ransomware attack, DarkOwl endeavors to merely highlight the suspicious timing of these specific announcements – along with threatening language included in the release – and the lack of any mention, nor claim of responsibility attacks against global meat distributor, JBS SA attack during Memorial Day weekend; an attack that temporarily impacted meat supplies around the world and caught the attention of the U.S. White House and international authorities.
These latest victims highlight the increasingly vulnerability of supply-chain attacks against critical service providers and the potential impacts to national security in the U.S. and abroad.
REvil Threatens to Share Sensitive Victim Data to Foreign Military Agencies
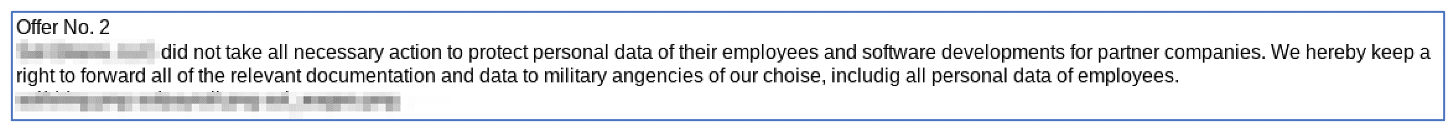
REvil representatives continually maintain their financially-motivated and opportunistic stance with numerous darknet forum posts stating that they want no part in geopolitical affairs nor act on behalf of any government. In these latest victim announcements, REvil included sensitive military contract information and critical personally identifiable information (PII) of the victim’s employees, such as copies of employee passports, payroll statements, and national identification numbers, as “proof” of the legitimacy of the attack.
More sinisterly, they also acknowledge the sensitivity of the data they’ve stolen and stated they would not hesitate to share this information with other foreign military agencies of their choice, directly contradicting earlier positions of agnosticism in international government affairs or military operations.
Many sources have already confirmed the likelihood that REvil is a Russian-based cyber-criminal organization. The recent string of ransomware attacks by REvil, their affiliates and similar groups, suggest that these organizations are indeed directly targeting critical supply-chain targets with unique technological and critical infrastructure focus, instead of indiscriminately targeting victims for monetary gain.
It is also noteworthy to point out that there is no current consensus on how long RaaS operators like REvil can maintain unauthorized access to victim networks, during which time they would be able to extract data and conduct potentially cyber-espionage-like activity before making themselves known. In other words, the target’s networks are freely accessible to these criminals for an unknown period of time before they finally pull the plug on the operation by deploying a ransomware variant, which then locks down the network, notifies the victim, and begins the phase of extorting target by demanding a ransom.
One security researcher recently shared their analysis of the latest version of REvil’s source code, version 2.05, stating that persistence of the malware was maintained through creating a registry key under SOFTWARE\Microsoft\Windows\CurrentVersion\Run (on Windows machines), which allows the malware to run every time the user reboots their machine. Other ransomware analysis of victims of the Pysa/Mespinoza strain, detailed an 8 hour campaign, launched via a compromised RDP account, where threat actors moved laterally throughout the entire domain harvesting additional credentials and data wherever possible (Source). This, however, is unsurprising as it is well-known that REvil and other popular RaaS operators leverage stolen VPN, RDP, and user credentials where available – often actively sold and traded on the darknet – and readily prey on unpatched server-side software and remote working products like Citrix ADC.
What other kinds of companies are REvil and their affiliates considering as potential targets?
In an interview conducted earlier this year, REvil representative known simply as “Unknown/UNKN”, stated many of their affiliates had unprecedented access to national security assets (directly or indirectly) including, “a ballistic missile launch system, one to a U.S. Navy cruiser, a third to a nuclear power plant, and a fourth to a weapons factory.” The veracity of this extremely serious claim has not been verified by DarkOwl nor the interviewer who spoke directly with Unknown. Others skeptical of interviews with such unreliable threat actors note that this particular “Unknown” could have been an imposter, as alias hijacking is common in across darknet communities.
However, supporting the ransomware group’s claims of their alarming access to such national entities are recent reports confirming that another ransomware victim is a company that manages the US fleet of military vehicles. While not presently determined to be directly attributed REvil, this incident is indicative that ransomware groups as a whole are indeed successfully compromising vendors supporting US and allied military efforts.
An Ever-Expanding and Continuous Operation
REvil fingerprints have also been recently detected in a new strain of ransomware known as Episilon Red, which information security researchers directly associate with a concerted attack on Microsoft Exchange mail servers. In late May, another new ransomware variant known as Prometheus setup a new Tor onion service claiming they were a “Group of REvil” in their ransom note and branding. Security researchers indicate that Prometheus, operating now for over a month, pens their ransom notes very similar to MountLocker and Medusalocker ransomware variants.
Despite the media attention the JBS SA attack garnered, REvil shows no sign of slowing down or scaling back their operations. In an interview conducted with Russian OSINT YouTube channel last week, they suggested they had previously limited themselves from conducting attacks against U.S. targets, although DarkOwl notes several of their victims over the past year included retail, health, legal, and agricultural companies with operations headquartered in the U.S.
The group’s spokesperson also showed no concern for being considered “terrorists” by the U.S. government or intelligence community, boasting their confidence in prosecution immunity, being sheltered by Moscow, who undoubtedly allows them to operate freely without legal consequence. They concluded their interview with the statement “We are not going anywhere, we are not going anywhere. We will work harder, harder, and harder.” (Source)
DarkOwl will continue to monitor this ongoing story and update as our analysts uncover information.
Breached data from ransomware attacks often wind up on the darknet. Contact us to see if your organization has been the victim of a cyber attack to gain insight into the full extent of your company’s darknet exposure.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















