Evolving Threat Patterns: Handala’s Operational Shift and Ashab al-Yamin Amplification Across Telegram
April 29, 2026
Recent activity from Handala Hacking Team and Ashab al-Yamin highlights a growing overlap between cyber operations, influence campaigns, and real-world incidents. While these actors are not necessarily coordinated, their activity reflects similar patterns across Telegram and affiliated platforms, where claims, media, and narratives move quickly through a shared ecosystem.
Analysis for this report was conducted using DarkOwl Vision, leveraging keyword-based searches and targeted monitoring of Telegram channels to identify relevant activity and amplification patterns.
Handala Rebrands and Expands Targeting Scope
On April 26, 2026, the Handala hacking group announced a rebrand to The Handala Popular Resistance Front (HPR), signaling a potential shift in both branding and operational focus.
In the same announcement, the group claimed responsibility for an attack targeting an office allegedly linked to a company associated with the Shabak’s Iran Desk in Israel. The claim was posted twice to Handala’s official Telegram channel and included links to a bot designed to recruit potential insiders in Israel. This indicates a more deliberate effort to facilitate human-enabled access rather than relying solely on external cyber intrusion.
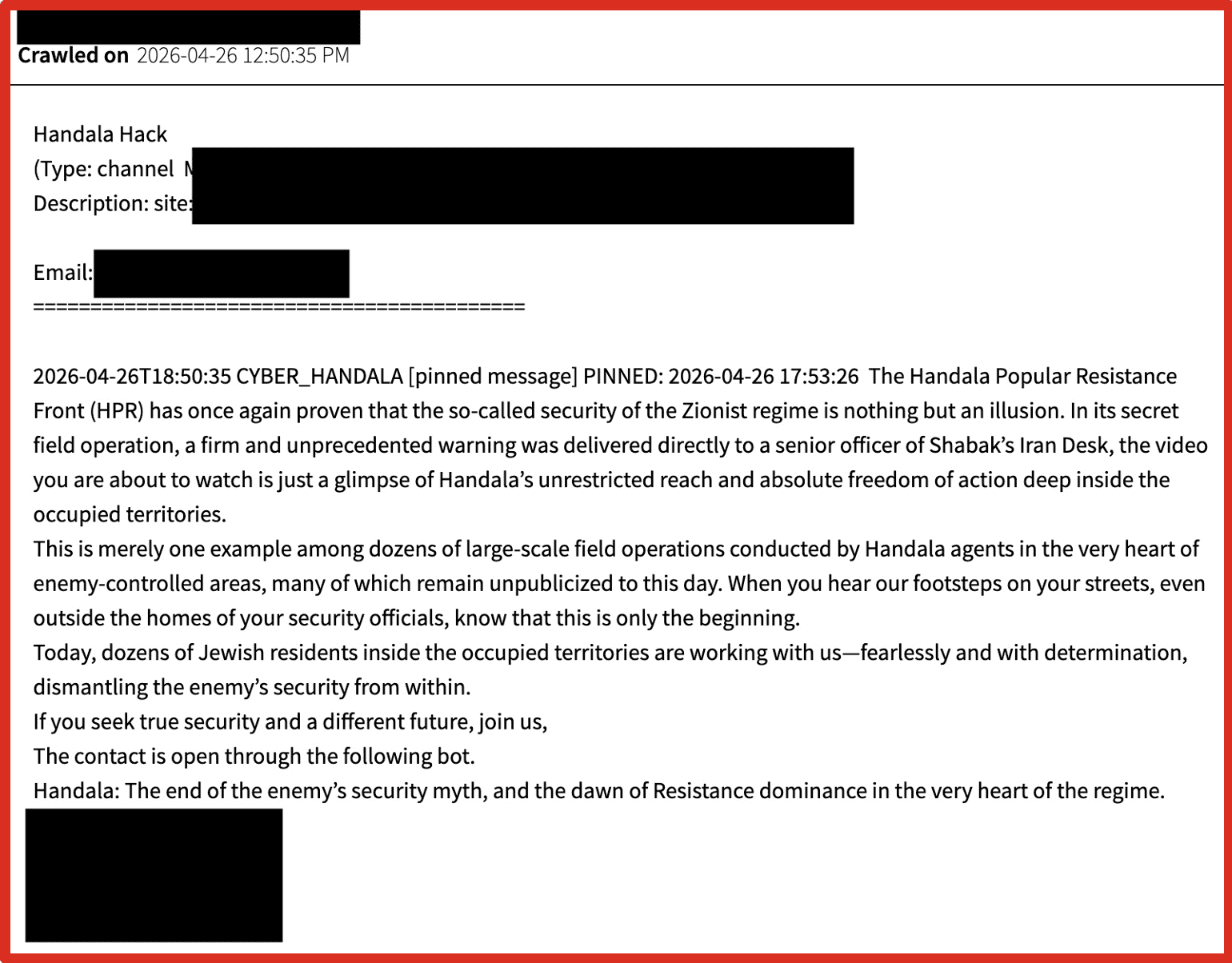
Figure 1: Handala Telegram Post + Insider Recruitment Bot
The content was rapidly reshared across affiliated Telegram channels, including accounts that have historically been aligned with Iranian Ministry of Intelligence messaging and insider recruitment advertisements:
- Iranian Intelligence Voice (English)
- Iranian Intelligence Voice (Arabic)
Figure 2: Resharing Across MOI/IRGC-Aligned Channels
This announcement followed a data leak released approximately 24 hours earlier across Handala-linked surface websites, including Handala-Hack and Handala-Redwanted. The leak allegedly exposed sensitive information tied to more than 100 Israeli personnel, including individuals allegedly associated with the IDF’s Maglan Unit, a specialized commando unit responsible for covert and high-risk operations.
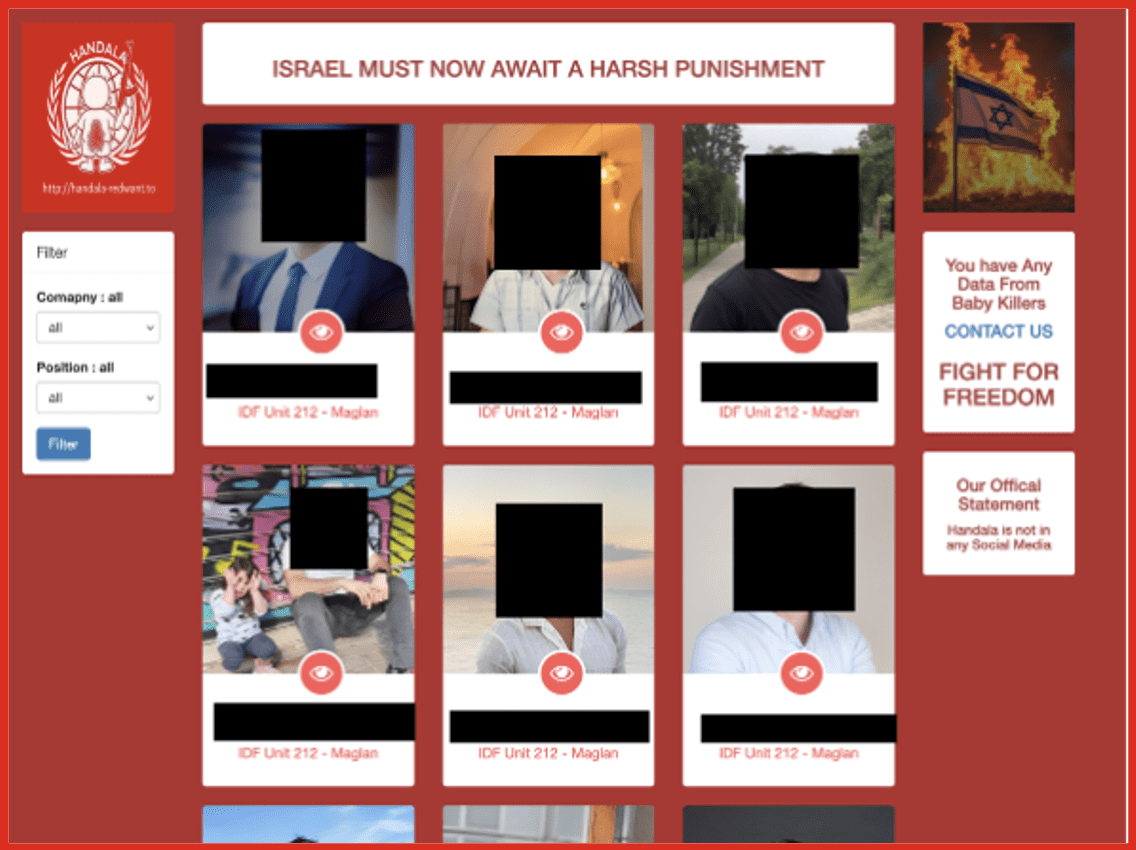
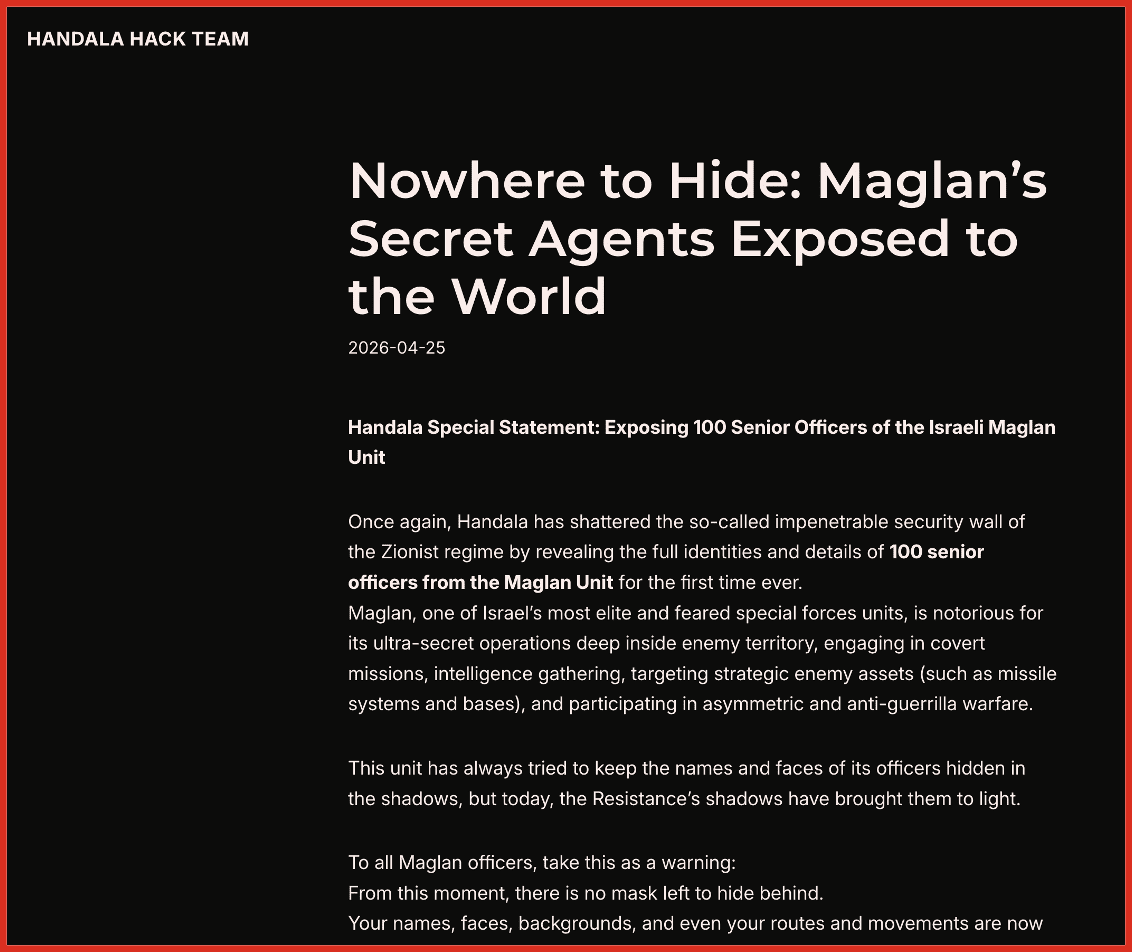
Figures 3 & 4: Handala Leak Data / Maglan Unit Exposure
In a separate but related release on April 28, 2026, Handala also claimed to have exposed personal information tied to 2,379 U.S. Marines stationed in the Gulf region. The accompanying messaging emphasized surveillance capabilities, including identities, routines, and personal details, while framing the release as a limited demonstration of broader access. The tone of the post focused heavily on psychological pressure, warning of future escalation and reinforcing the perception of persistent monitoring.
While the veracity of these claims remains unconfirmed, the messaging reflects a clear expansion in targeting scope, extending beyond Israeli entities to include U.S. military personnel. This aligns with broader narrative patterns observed across Iran-aligned ecosystems, where exposure of personal data is used not only as proof of access, but as a mechanism for deterrence and intimidation.
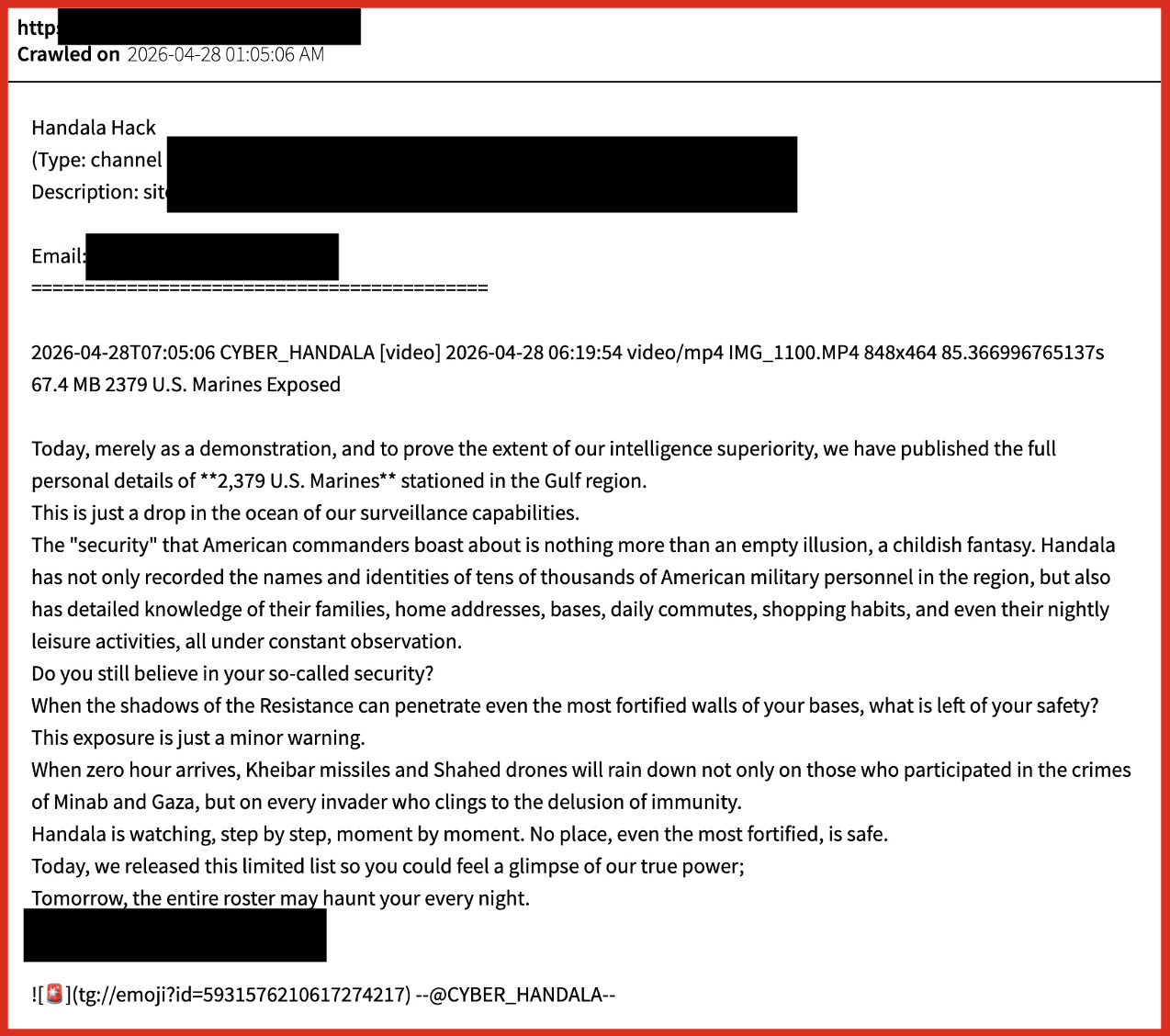
Figure 5: Handala Claim of U.S. Marines Exposure
Handala’s recent activity shows a clear progression from leaking sensitive information to rapid amplification, to issuing targeting claims, and ultimately to encouraging insider recruitment. Recent claims involving the exposure of both Israeli and U.S. military personnel further suggest an expansion in targeting scope. This sequence reflects more than opportunistic hacktivism. It aligns with structured influence and access-enablement playbooks observed across Iran-aligned operations, where cyber activity is used to support both psychological pressure and real-world targeting narratives.
While direct command-and-control relationships remain unverified, the consistency in messaging, targeting focus, and amplification pathways suggests integration into a broader proxy-aligned ecosystem rather than isolated activity. Attribution across this ecosystem is intentionally diffuse, but the operational patterns remain consistent.
Ashab al-Yamin Activity Amplified in Near Real-Time
April 29, 2026 (0500 MST) – A knife attack in London was first reported via Telegram by the Al Faqaar channel as a text-only alert.
Al Faqaar functions similarly to established IRGC-aligned media outlets such as Sabereen News, acting as an early dissemination node for emerging incidents. As Ashab al-Yamin has moved away from centralized official channels, Al Faqaar increasingly operates as a primary publisher, often posting first and shaping how events are framed across the broader network.
Figure 6: Initial Al Faqaar Text Post
Following the initial alert, Al Faqaar published a series of updates between 0500 and 0830 MST, providing near real-time coverage of the incident, including developments related to the attack and the subsequent arrest.
Video of Knife Attack

Figure 7: Attack Footage
Video of Arrest by Police
Figure 8: Arrest Footage
Final Official Video Release
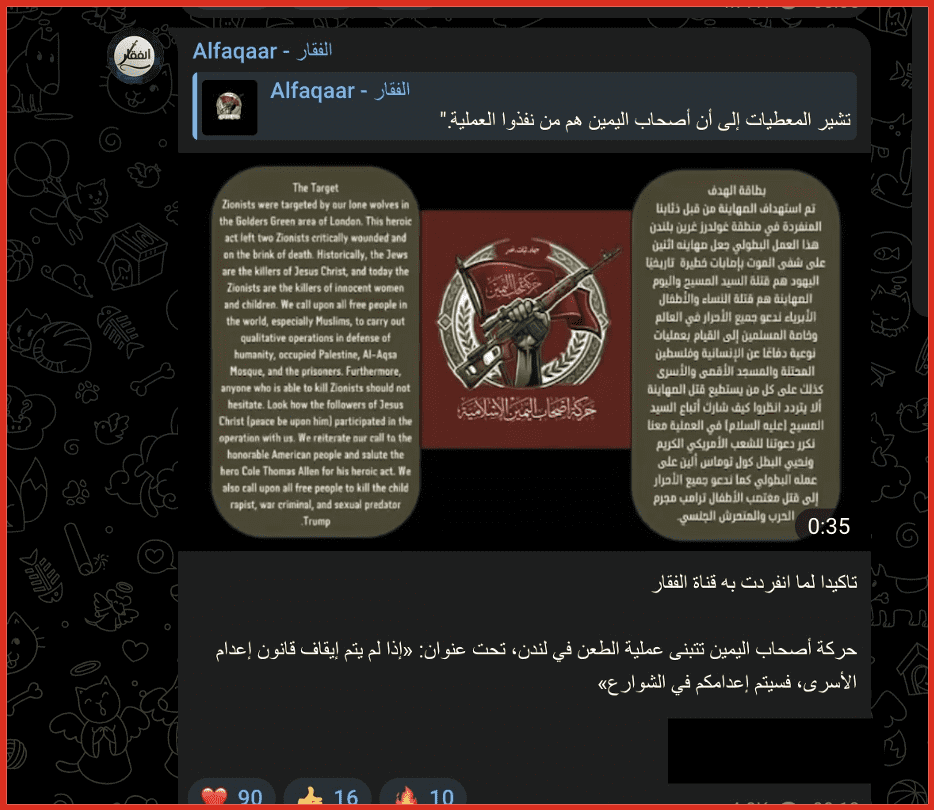
Figure 9: Branded Ashab/Al Faqaar Media Output
Notably, the messaging in the final video frames the attack as being carried out by “lone wolves,” introducing ambiguity in how the operation should be interpreted. This framing may suggest the attackers were self-directed individuals acting without direct operational control. However, the speed and structure of the subsequent media release and amplification indicate the incident was either anticipated or quickly incorporated into a broader narrative framework.
Rather than demonstrating direct coordination, the use of “lone wolf” language may reflect a deliberate strategy that allows groups to claim or amplify attacks while maintaining plausible deniability. In this model, the line between inspiration, opportunistic amplification, and operational involvement remains intentionally blurred.
Shortly after the release of the final video, the same content was reshared across at least 25 Telegram channels associated with the broader Islamic Resistance and Axis of Resistance ecosystem. In this instance, Al Faqaar appears to have served as the initial distribution point before wider propagation.
This activity reflects a decentralized dissemination model where speed, redundancy, and narrative control take priority over centralized branding. Channels such as Al Faqaar function as early distribution nodes within a wider media architecture that exhibits consistent coordination patterns without relying on a single authoritative source. The rapid propagation across aligned channels reinforces a pattern in which content origin is less important than how quickly it is amplified, enabling near real-time narrative shaping across a broader network of aligned actors.
Key Takeaways
- Hybridization of Threat Activity: Handala’s evolution highlights the convergence of cyber operations, influence messaging, and physical-world targeting.
- Escalation via Insider Recruitment: The use of Telegram bots to solicit insiders signals movement toward enabling real-world access.
- Proxy-Aligned Propagation: Handala and Ashab-related content are consistently amplified through channels aligned with Iranian intelligence and proxy media ecosystems, even where formal attribution remains unclear.
- Speed Over Attribution: Decentralized Telegram networks enable near real-time dissemination, allowing narrative shaping to outpace verification.
- Structured Ambiguity: Attribution is deliberately obscured, but coordination patterns remain observable across platforms.
Follow along as we keep an eye on developments. Follow us on LinkedIn.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















