Prepping The Battlefield – The New Cyber Warfare Playbook
February 10, 2026
Warfare has always gone hand and hand with technological innovation. Nuclear energy followed the nuclear bomb nearly a decade after the first atomic weapon was detonated. Before the World Wide Web, there was ARPANET, launched in 1969 by the U.S. Department of Defense to connect military and research installations through distributed computer networks, more than 20 years before the internet became public. Before commercial GPS, there was NAVSTAR, a U.S. military satellite program developed in the 1970s, originally designed for missile guidance, troop movements, and precision targeting—years before civilian GPS became available. Military jet engines preceded commercial aviation, military radar predated modern weather forecasting, military encryption existed long before public cryptography and e-commerce, and drones, satellites, and even mass-produced antibiotics were first developed to meet battlefield demands.
Once again, militaries are leveraging technology to redefine tactics and battlefield strategies. Nation-states are increasingly developing offensive cyber capabilities not merely as tools, but as a means to prepare and shape the battlespace before military action occurs. Power grids, communications infrastructure, air defenses, satellites, psychological, and command-and-control systems are now targeted before the first kinetic shots in anger.
In this blog, we’ll review some of the most impactful nation-state offensive cyber operations in the modern era and how they illustrate this escalating trend of warfare.
Operation Orchard – September 6, 2007
Eleven years after Operation Orchard, Isreal admitted it was responsible for an airstrike in Syria that targeted a suspected nuclear reactor which may have been capable of enriching nuclear weapons material. No jets were shot down during the operation and no surface to air defense missiles were deployed from the Syrian military. In other words, Israel entered Syrian airspace without resistance.
According to multiple sources, the failure of Syrian air defenses during the 2007 strike has been attributed to a proactive Israeli cyber and electronic warfare operation that temporarily disabled radar and surface-to-air missile systems. Although specific methods were never publicly disclosed, analysts have speculated that the operation may have involved advanced electronic jamming and a software capability known as Suter.
Suter, reportedly deployed aboard specialized aircraft, is believed to exploit radar and air-defense systems by detecting their emissions and injecting malicious signals back into the emitters. This can result in disrupted sensor feeds, conflicting or false target data, and, in some cases, complete loss of radar functionality, effectively rendering the air-defense network inoperable during the operation.
Russian Invasion of Georgia – August 8, 2008
One day before Russian military units entered Georgia in 2008, there were widespread cyberattacks targeting local media as well as governments websites. These attacks were primarily distributed denial of service (DDOS) and website defacements. Although less sophisticated than other types of nation state cyber operations, these attacks aimed to isolate and silence both Georgian officials, and the civilian population.
With government services offline, it became difficult for state officials to communicate and respond to the events that would take place the following day. And when local media was unable to broadcast, they too could not communicate to the public the impact of Russians invasion into their homeland. This strategic DDOS attack caused confusion and made disinformation more potent as Russia continue to take control of Georgian territory.
The next phase of the cyber operation broadened the scope and targeted financial services, institutions, and even launched anti-Georgian hacktivist websites to stir discontent and make civilian resistance to the Russian operation less attractive.
Russia – Ukraine – 2014
There is ongoing debate among experts regarding the strategic significance of cyber operations during Russia’s 2014 annexation of Crimea. While offensive cyber activity was present during and intensified after the invasion, it is difficult to argue that these operations played a decisive role in enabling Russia’s territorial gains or directly shaping battlefield outcomes for Russian forces on the ground.
More impactful cyber operations emerged after the annexation. The Sandworm campaign stands out as one of the most consequential post-Crimea cyber efforts, causing extensive disruption to Ukrainian networks and, in later operations, contributing to widespread power outages. Other destructive campaigns, including wiper-style malware such as NotPetya, similarly targeted Ukrainian institutions and critical infrastructure in the years following 2014, reinforcing cyber operations as a persistent element of Russia’s broader pressure campaign rather than a decisive pre-invasion enabler.
Russia invasion of Ukraine – 2022
By February 2022, it had become clear that Russian military strategists believed their prior cyber operations were worth leveraging again in the lead-up to a full-scale invasion of Ukraine. Many of the same cyber tactics observed in previous years were redeployed days—or even hours—before Russian troops crossed the Ukrainian border.
In the days preceding the invasion, WhisperGate targeted Ukrainian government websites and servers. Disguised as traditional ransomware, WhisperGate was in fact wiper malware designed to destroy data and render systems inoperable. Shortly thereafter, coordinated DDoS attacks disrupted Ukrainian banks and temporarily took multiple government websites offline.
Just hours before the ground invasion commenced, a synchronized campaign deploying HermeticWiper and IsaacWiper further targeted Ukrainian government networks with wiper malware. These attacks appeared aimed at degrading communications, slowing coordination, and complicating defensive responses.
As wiper malware was overwriting disks across Ukraine, a separate cyberattack targeted satellite communications infrastructure. Ukraine’s ViaSatKA-SAT system was taken down, disrupting satellite connectivity used by civilian networks as well as certain Ukrainian military assets. This attack demonstrated a deliberate effort to impair command, control, and situational awareness at the critical opening phase of the invasion.
United States – Venezuela – 2025
The recent operation in Caracas demonstrates the capabilities that emerge when cyber warfare is integrated with real-world troops in combat. Although few details, means, or methods have been made public, there is still a significant amount of evidence highlighting the impact the United States Cyber Command made during Operation Absolute Resolve.
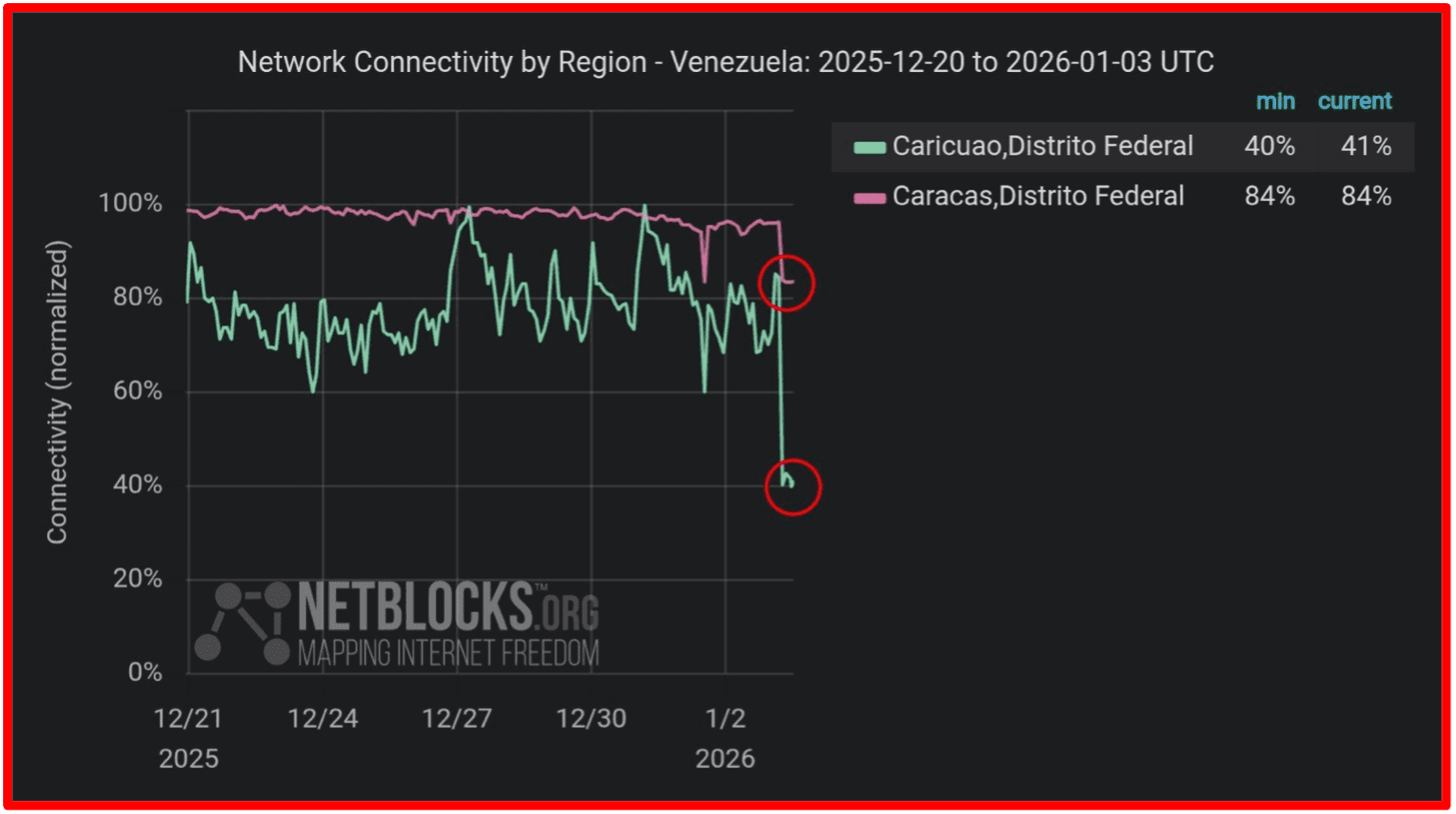
According to American officials, cyberweapons were used in Venezuela to disable power in regions near military bases in Caracas, as well as to shut down radar defense systems and even handheld radios used by the Venezuelan military (see image below). Unverified reports from soldiers and security personnel in Caracas claim to have experienced “intense sound waves, severe physical distress, and bleeding during the operation”. United States President Trump spoke to NewsNation after the operation and stated that a “sonic weapon” had been used during the raid.
Final Summary – The Cyber Battlespace Comes First
Modern warfare is no longer defined solely by armies, aircraft, and armor. As history has repeatedly shown, military necessity drives technological innovation, often before those capabilities reach the civilian world. Today, offensive cyber operations represent the latest evolution of this pattern—an invisible means of shaping conflict before the first kinetic action occurs.
The cases examined in this blog demonstrate a clear trend: nation-states now treat cyberspace as a domain of warfare. From Israel’s alleged disabling of Syrian air defenses during Operation Orchard, to Russia’s coordinated cyber disruptions preceding invasions of Georgia and Ukraine, cyber operations are used to blind sensors, sever communications, disrupt civilian infrastructure, and undermine public trust. These actions are not isolated technical events; they are strategically timed efforts designed to degrade an adversary’s ability to detect, decide, and respond under pressure.
Keep up with us. Follow DarkOwl on LinkedIn.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















