Q1 2026 Product Updates and Highlights
April 21, 2026
The team is excited to share the new capabilities, platform improvements, and notable darknet intelligence collected across January, February, and March.
Q1 was a big quarter for the DarkOwl platform. We’ve been laser-focused on one goal: helping analysts work faster and smarter — surfacing the right intelligence at the right moment, without ever breaking their flow. Here’s a look at what’s new.
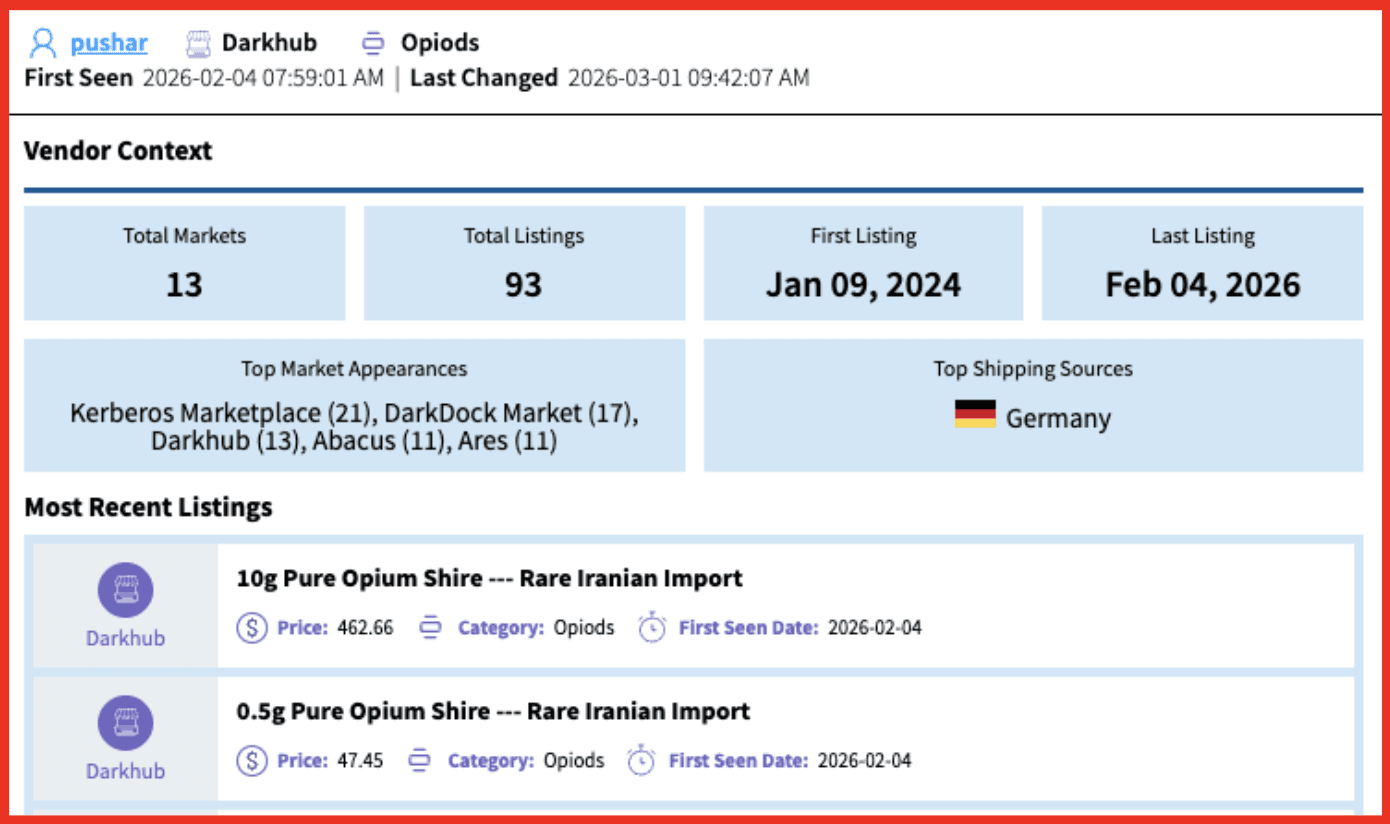
Introducing Vendor Context in Market Research
It’s never been faster to assess vendor scale, longevity, and risk — all without leaving the market listing result you’re already looking at. Vendor Context delivers an instant, comprehensive snapshot of any known vendor — directly within a Market Research listing. With a single click, analysts can see:
- Total markets and listings the vendor has appeared in
- First and last observed activity dates
- Top markets where the vendor is most active
- Primary shipping sources
- The vendor’s five most recent listings across all markets
Vendor Context expands on DarkOwl’s market dataset and features, providing a purpose-built, structured investigative capability specifically designed for darknet marketplace analysis. Markets are among the most operationally significant environments on the dark web—serving as hubs for the sale of drugs, weapons, stolen data, counterfeit goods, and as nexus points for the criminal networks. DarkOwl’s enhanced market holdings now include more than 431,000 listings which extract vendor identity, product description, category, price, accepted payment methods, shipment origin/destination, reviews, and more.
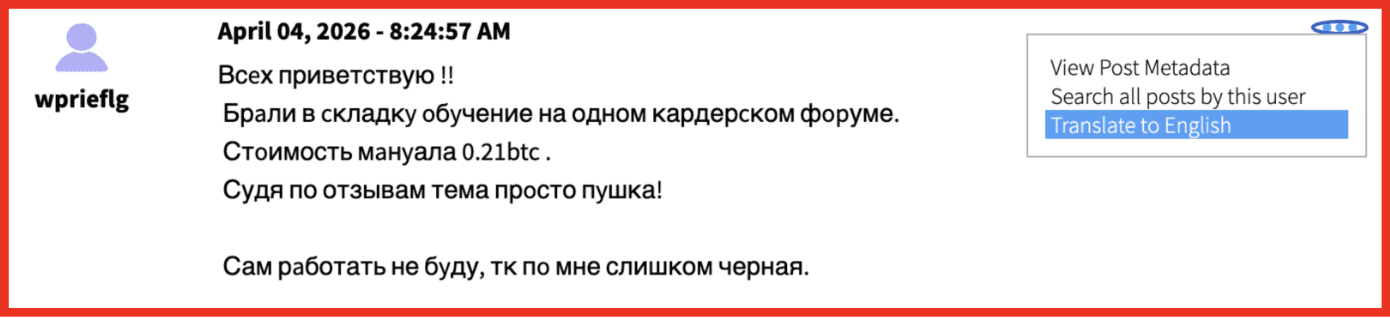
Breaking the Language Barrier
A substantial portion of threat actor activity, forum discussions, marketplace listings, and leaked data originates from Russian, Chinese, Arabic, Farsi, and other non-English-speaking communities. Global threat intelligence means working across dozens of languages. We’ve made that dramatically easier with Translation for search results. Instantly translate any text from search or alert results inline, now covering all 52 languages supported by Vision UI. No external tools, no copy-pasting — just highlight, click, and read. And because we know it matters for sensitive environments: translation runs entirely within the DarkOwl platform, with no data leaving our closed environment.
Deeper Intelligence and Streamlined Analyst Workflows
- Expanded Site Lexicon and Context — Data Sharing and File Repository are now recognized site categories, with full Site Context enabled across results — making it easier to identify and investigate these areas of the darknet. Key press releases, law enforcement actions, and major news coverage are now linked directly within a new media reporting field in Site Context.
- Export by Date Range — Generate time-based reports from Case Findings to share only the most relevant data or align exports with reporting or investigative timeframes.
- Save as Finding Snippet — Highlight any text in a result, click “Save as Finding Snippet,” and the Add Finding panel opens automatically. Analysts can save both the original and translated text as separate snippets within the same Finding — ideal for reporting, collaboration, and evidence tracking.
- Additional UX improvements — A Case Overview redesign to ensure critical alerts are now front and center; easier navigation in Actor Explore; additional fields on results from Paste sites.
Vision API Updates
For teams building on the DarkOwl API, Q1 brought expanded data access and improved developer experience:
- Paste-specific fields now available in Search API: author, postDate, expires, and key
- Media Reporting in Context API for sites
- Updated API documentation for a smoother integration experience
Collection Stats
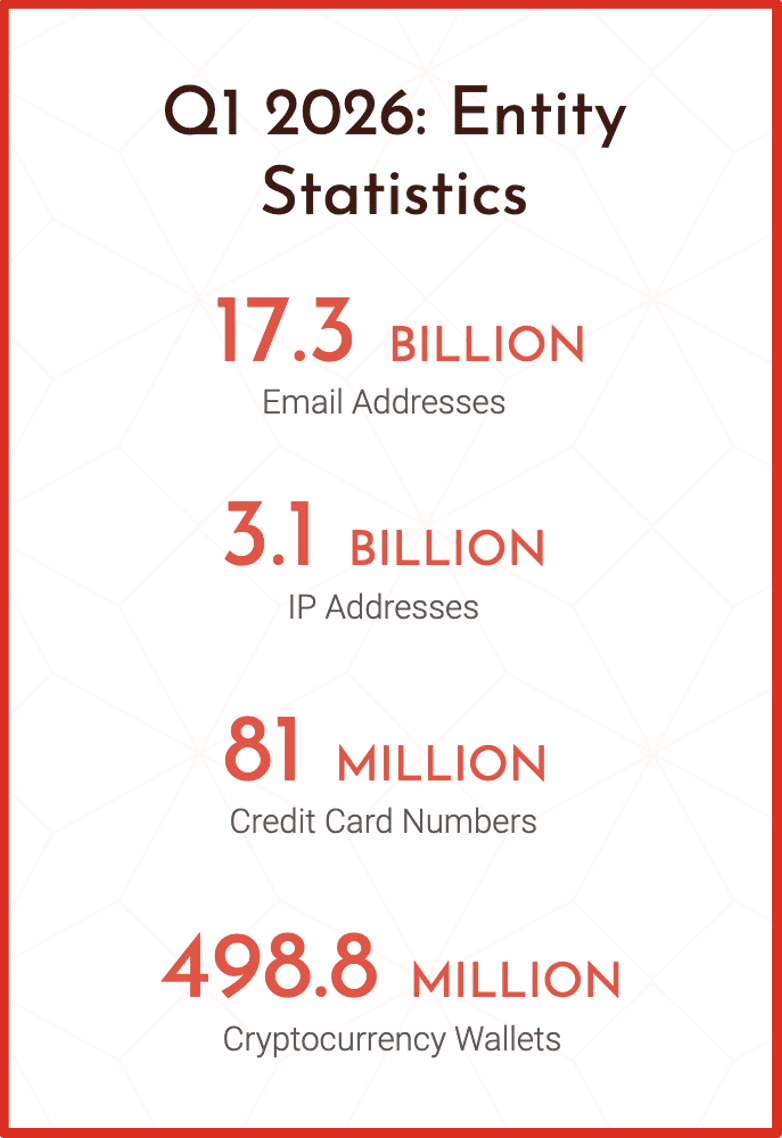
Our data collection team continues to astonish us with the quantity of data made available across all DarkOwl products. Let’s highlight just some of that growth year over year:
- 21% increase in credit card numbers
- 20.5% increase in email addresses
- 9% increase in IPs
Notable Content Collected
Our collection and research teams had a busy quarter. Here’s a snapshot of some of the most significant data leaks and original research that happened in Q1.
Original Research
Dark Web Reactions to the Israel–Iran Conflict
In March 2026, our team published an in-depth analysis of how dark web and adjacent communities responded to the escalating conflict between Iran, Israel, and the United States. Hacktivist groups launched over 149 DDoS attacks against 110 organizations—107 of them in the Middle East—within days of the strikes. Jihadist communities on Telegram and Rocket.Chat used the conflict to amplify recruitment narratives, including a call for “global cyber jihad” from a group claiming al-Qaeda ties. Iranian-aligned militia channels circulated target lists and operational claims, while a notable crossover emerged between extremist ideological communities as groups linked to Nihilistic Violent Extremism blurred traditional political lines. DarkOwl continues to monitor these ecosystems as the conflict evolves.
Leaks of Interest
BreachForums 2026
Posted on January 9, 2026, this leak exposed personal data for approximately 324,000 BreachForums users. The exposed data includes usernames, email addresses, and IP addresses for a large population of actors who may participate in buying and selling stolen data. The data came from a database backup dated August 11, 2025, inadvertently left in a publicly accessible directory during a site restoration. A 4,400-word manifesto attributed to a threat actor using the pseudonym “James” accompanied the data, framing the leak as deliberate retaliation against the forum’s users following attacks on French infrastructure.
Harvard University
Posted on ShinyHunters on February 4, 2026, this dataset purports to contain 1 million records from Harvard’s Alumni Affairs and Development systems. The breach originated from a vishing campaign in November 2025 where attackers impersonated support staff and bypassed Multi-Factor Authentication in real time. Researchers describe the exposed data as a “map of influence”—including private home addresses and mobile numbers for prominent individuals alongside sensitive donor contracts and internal strategy documents. The combination of donor financial data, direct contact information, and internal strategy documents creates a rich target for spear-phishing, fraud, and reputational exploitation across a high-profile institution’s network. For security teams evaluating their own exposure, this is immediately relevant to how they think about vishing defenses and privileged access to constituent or membership systems.
LexisNexis
Posted to DarkForums on March 3, 2026 by threat actor FulcrumSec, this breach exploited an unpatched React application on LexisNexis AWS infrastructure via a React2Shell vulnerability combined with a weak RDS master password. The actor claims to have exfiltrated over 2GB of data including plaintext credentials and contact details for 118 U.S. government employees—including federal judges and DOJ attorneys. LexisNexis characterizes the data as largely pre-2020 legacy records. FulcrumSec frames the attack as separate from a 2024 breach that prompted a class-action lawsuit and states it was not geopolitically motivated, but intended to highlight a “sustained pattern of negligence.” For organizations that rely on LexisNexis—law firms, financial institutions, government agencies—exposure of the underlying records is a direct concern. The inclusion of federal judiciary and DOJ contact information in a publicly accessible darknet post significantly elevates risk.
Curious how these features and data can make your job easier? Get in touch!
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















