Ransomware Affiliate Programs: Anatomy of a Criminal SaaS
March 5, 2026
Ransomware isn’t just malware, it is an operating model. Increasingly, ransomware groups as well as extorting victims themselves, have also operated “affiliate programs,” often called Ransomware-as-a-Service (RaaS). In this arrangement, a core team provides the tooling and brand, while affiliates conduct intrusions and share the proceeds with the owners of the malware.
This blog breaks down how the affiliate model works, why it persists, and which ransomware “brands” researchers most often associated with affiliate-driven operations in 2025.
What is a ransomware affiliate program?
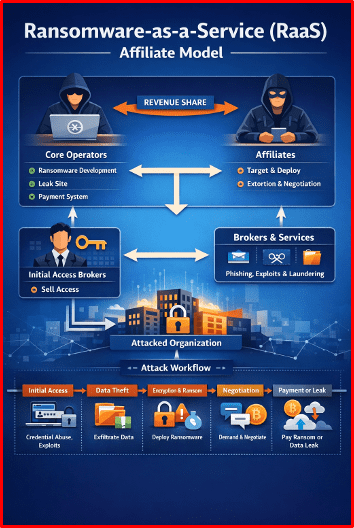
A ransomware affiliate program is a partnership structure between a core operator group – usually developers and infrastructure maintainers – and affiliates which usually consist of intrusion teams who deploy ransomware and run extortion negotiations with the victim, with revenue typically split between them. Think of it as a criminal version of a platform business: the “platform” team builds and maintains the product (ransomware + infrastructure), while “partners” scale distribution (intrusions) in exchange for a share of profits.
The RaaS division of labor – who does what?
The core group are usually responsible for maintaining the ransomware codebase and continually updating it to evade defenses; they will also host negotiation portals, victim dashboards, and leak sites where victim data is shared on the dark web.
They will also provide “support” to affiliates by providing troubleshooting services, process guidance and other things to ensure that the affiliates are successful.
Affiliate programs usually have a strict set of rules on how the ransomware can be used. The core group sets these rules and enforces program rules; these usually cover who can target what, what tactics are allowed, and dispute handling.
The Affiliate groups are usually responsible for choosing targets and executing intrusions using the malware they are supplied by the core groups. They will also perform data theft and later-stage deployment steps, run negotiations, which can sometimes have operator oversight or supplied templates. They will also coordinate payment verification and handoff of decryption. However, this can vary by program with different groups having different practices and different revenue shares.
Although the core group and the affiliates are the main practitioners, other threat actors can also be involved in this ecosystem such as Initial Access Brokers (IABs) who sell access to compromised environments which the ransomware group or affiliates will then use to target victims. There can also be specialist roles for credential theft, phishing, negotiation, laundering, etc.
This separation makes attribution harder for researchers and explains why the same intrusion patterns can “carry over” even when a ransomware “brand” changes.
What affiliates “get” from the program
Most established RaaS operations provide a bundle that looks like a grim SaaS product, this can include Affiliate panels / dashboards to manage victims, builds, and negotiations, a standardized extortion workflow which can include victim instructions, negotiation playbooks, as well as product support. They will also be provided with access to leak site infrastructure, hosted on the dark web, to publish victim data and increase pressure. As well as being provided with all the tools, being an affiliate is an attractive prospect as it also provides brand credibility. A known “name” can increase perceived threat and victim payment rates. Not all ransomware groups are the same, and some have the reputation for being successful and or being able to target high profile victims.
The typical lifecycle
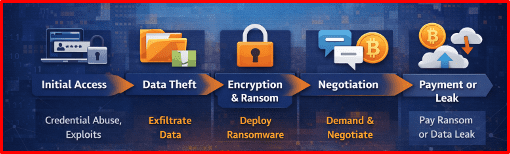
While the entry method differs by actor, many affiliate-run incidents follow a familiar lifecycle:
- Initial Access: The threat actor will obtain access to the victim’s infrastructure commonly via stolen credentials, exposed services, or purchased access, from an initial access broker. Increasingly data leaked after a ransomware attack can be used to target a supply chain.
- Data Theft: While traditionally ransomware encrypted data so the victim could not access it, that is not usually the case anymore with most actors simply exfiltrating as much data as they can from the victim. This data will then be used to extort the victim in the hope that the “ransom” will be paid to avoid the financial and reputational damage of having data shared on the dark web.
- Encryption & Ransom: Some actors do still use an encryption method as part of their tactics, and in all cases will issue a ransom note which will provide details of their demands – usually payment in cryptocurrency. Many groups position themselves in these notes as researchers who are helping the victim avoid damage. Whether encryption occurs is sometimes secondary, the “business” is often extortion, not encryption.
- Negotiation: Usually through the ransom note the victim is provided with a timeline in which to pay the ransom to avoid having their data released; this can also appear as a countdown on the darkweb leak site. The actors will often provide a portal for the victim to contact the threat actor, often on the dark web where negotiation can happen. As most victims do not disclose if they have paid the ransom or not, we do not have a clear picture of how these negotiations play out.
- Payment or Leak: If the victim chooses to pay the ransom, they will be provided with a cryptocurrency address in which to make the payment to. They will be provided with a decryptor, if the data was actually encrypted and the victim’s name will be removed from the leak site. However, the fact that the victim appeared on the page and then removed can suggest payment was made and can still cause reputational damage.
Many 2025 “top group” lists rely on data-leak site postings as a proxy for activity, but it undercounts failed extortions, private settlements, and unposted victims. Furthermore, as the data has been exfiltrated, there is no guarantee that making the payment means the data will not be released at some point. If the payment is not made, the data will be made available for download on the leak site.
How the money works: revenue share + trust problems
Affiliate programs need incentives and mechanisms to manage distrust and also to attract “good” actors to run operations. The programs usually work on the basis of revenue splits, where the affiliate keeps the larger portion, and operators take a platform fee.
Affiliates will often choose a ransomware brand that has not only had public success but also that are perceived as reliable payers. They may work with multiple groups. RaaS operators compete for affiliates with better splits, better support, more stable infrastructure, and broader “brand” recognition.
However, the core group can also be picky about who they work with, some groups are reported to only work with affiliates from certain countries and will set up their systems in a way to avoid exit scams, where operators steal all of the proceeds and do not pay the platform fee.
Takedowns, leaks, and internal conflicts lead can lead to splits, rebrands, and “new” groups that may be continuity operations rather than truly new actors. When a brand is disrupted, affiliates don’t disappear; they migrate, bringing tradecraft and victim targeting patterns with them.
Main ransomware brands commonly linked to affiliate-driven activity
Below are ransomware “brands” reported to be operating in an affiliate-friendly or RaaS-like manner. This is not exhaustive, and “brand” ≠ a single consistent team.
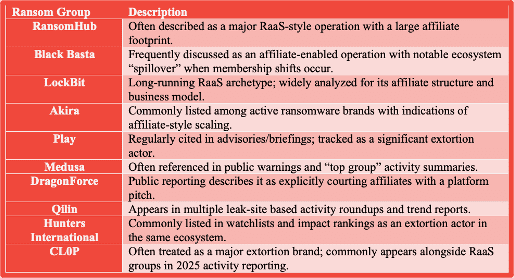
All of these groups are tracked by DarkOwl, with their leak sites being closely monitored for new victims.
Conclusion
Ransomware affiliate programs persist because they’re efficient; they turn a complex criminal operation into a repeatable platform. In 2025, the most important researcher takeaway isn’t just which brand is “on top,” but how affiliates move, how brands compete for them, and how extortion infrastructure evolves across disruptions.
Learn how DarkOwl tracks these groups and more. Contact us.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















