Tricks, Not Treats: Phishing, Social Engineering & the Dark Web
October 31, 2025
This Halloween, the scariest thing might be what’s tucked inside the candy bar, a lure that looks harmless but hands an attacker the keys to your digital life.
Phishing and social-engineering attacks are the “tricks” that become catastrophic when the dark web supplies ready-made toolkits and AI-generated messages to amplify them. The result: low-effort, high-impact scams that can ruin reputations and drain bank accounts.
This Halloween we explore the “scary tricks” cyber criminals are using to successfully trick you into clicking on phishing emails and other attack types, and what you can do to avoid this activity.
Phishing & Social Engineering: Why They’re Halloween-Worthy
Phishing and the wider family of social-engineering attacks (spear-phishing, smishing, vishing, “quishing” via QR codes, and voicemail impersonation) remain one of the simplest ways to get real access to real systems. For that reason, they remain one of the top cyber-attack vectors in 2025. Phishing and social engineering attacks have been responsible for some of the largest breaches so far this year, such as Salesforce and Allianz.
Researchers have highlighted that the large majority of successful cyber-attacks usually include a human element and are not purely technological vulnerabilities.
But two trends are supercharging phishing today:
- Automation and commoditization — phishing kits and “phishing-as-a-service” lower the technical bar for attackers. These are readily available software people can purchase to conduct attacks meaning they do not need to have the technical skills to conduct the attack.
- AI-augmented social engineering — generative models craft extremely convincing lures at scale. That combination turns the old “spray-and-pray” email into a professional, targeted, and scalable crime machine. Not to mention the creation of believable videos, images and voices which can be used to conduct vishing and other attacks.
The Dark Web Connection: Toolkits and Kits for Sale
The dark web and underground communities are where the tools, templates and services live, both marketplaces and forums offer software for sale as well as how to tutorials on how to conduct these attacks. Telegram also shared this information via marketplace channels. Below are some of the things being sold.
Security researchers have indicated that the availability of ready-to-use phishing kits on the dark web rose by ~50% from 2021 to 2025, highlighting that this is a trend that is only increasing.
Phishing Kits
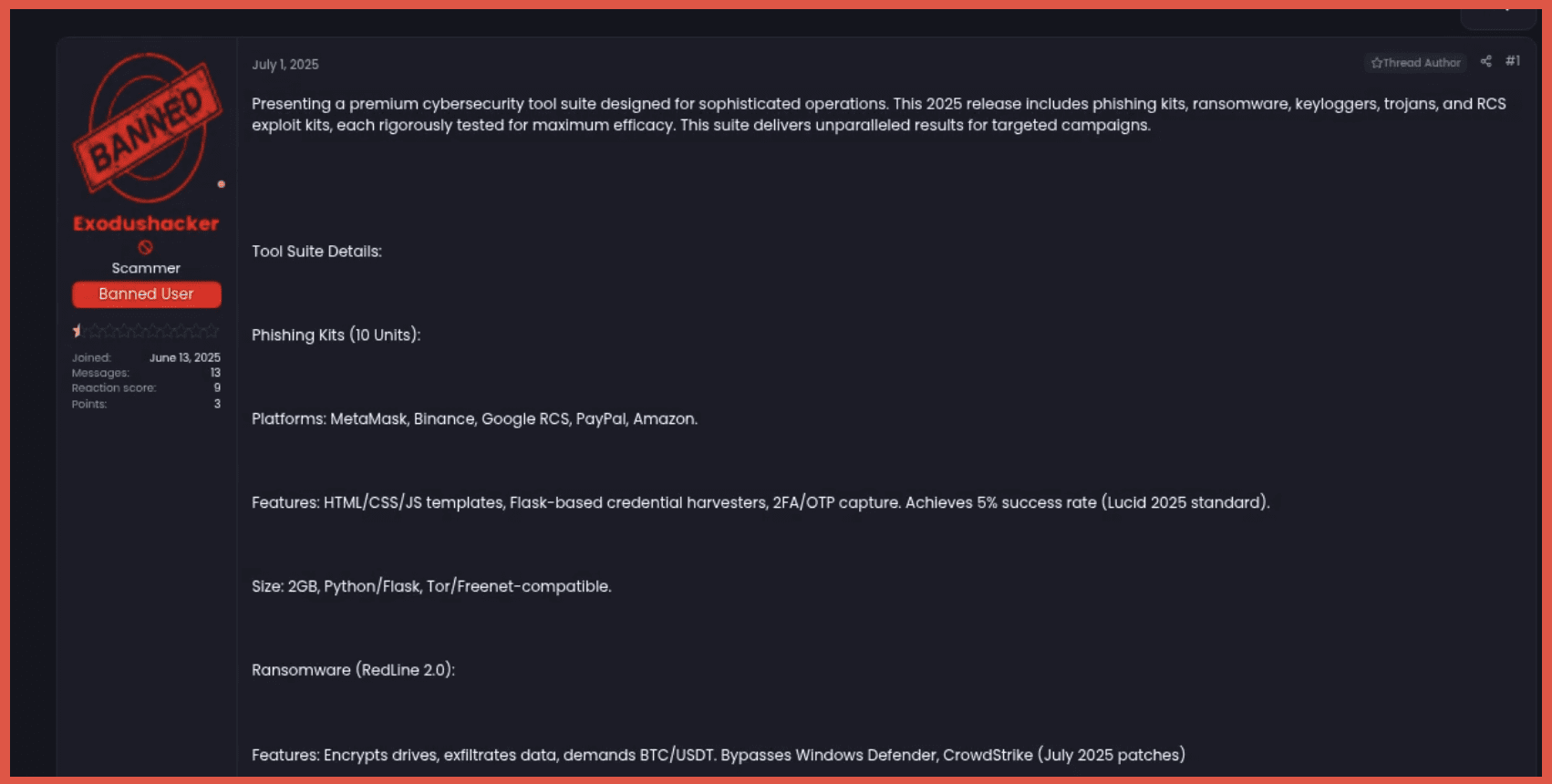
Pre-built fake pages, sending scripts and hosting/configuration guides. Research and reporting show fully fledged kits are routinely sold for pocket change, some reports find kits advertised for as little as ~$25 while others are open source, making it trivial for novices to impersonate banks, delivery services, or SaaS providers. The below image from a dark web forum shows users sharing a list of openly available phishing kits claiming they are the best kits to use in 2025.

Phishing-as-a-Service & Automation Platforms
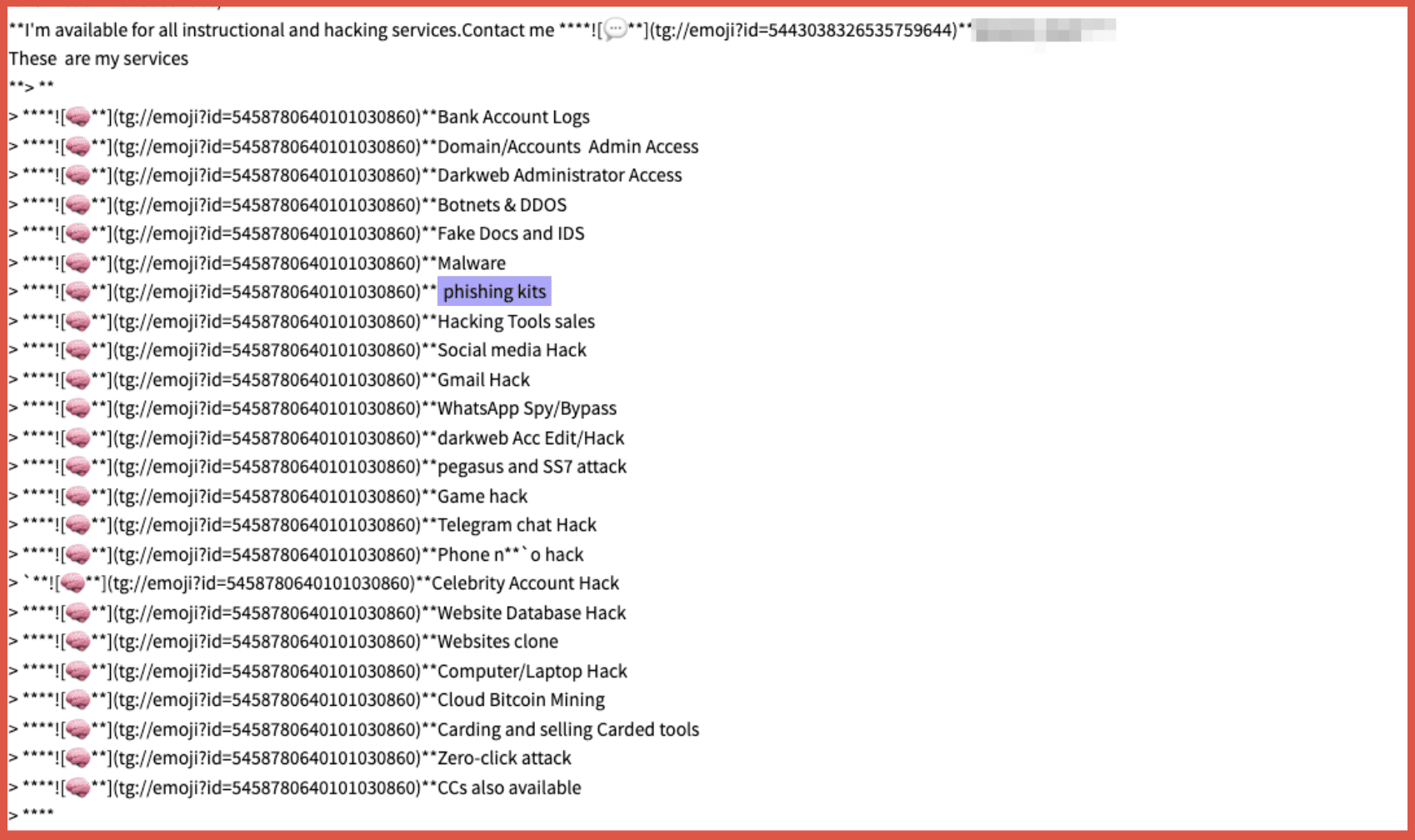
Another offering which is provided on dark web sites, is providing the service on the behalf of an actor. This means the actor doesn’t not need to take any action but can pay someone else to conduct the attack. The below image from Telegram shows a threat actor offering hacking services including phishing kits.
More advanced offerings include campaign dashboards, SMTP pools, deliverability testing and analytics (some newer tools even pair generative AI with mailing infrastructure). The below images show an advertisement for a phishing related AI model as well as the site to purchase the software. The “SpamGPT” toolkit—AI-powered spam-as-a-service sold on underground forums for around US $5,000.


Stolen Contact Lists & Harvested Credentials
While we have previously shared the sale of human organs, this Halloween the harvesting of credentials can be even more scary with wide ranging ramifications. Harvested credentials and victim lists, often sold in bulk, let attackers skip reconnaissance and target previously compromised users.
These data leaks, with credentials and sometimes a lot more information can be really useful to threat actors when conducting social engineering attacks. This can make phishing attacks seem much more believable as they have accurate and real information in them.
These tools lower the barrier to entry, enabling less-skilled attackers to launch large campaigns. They are readily available on the dark web and adjacent sites like Telegram. This means that the number of attacks being conducted can and will increase as individuals need less skills to conduct them. But it is likely that AI develops that the attacks themselves will become more sophisticated and complex. A scary thought!
How Phishing Campaigns Actually Play Out (The Attack Chain)
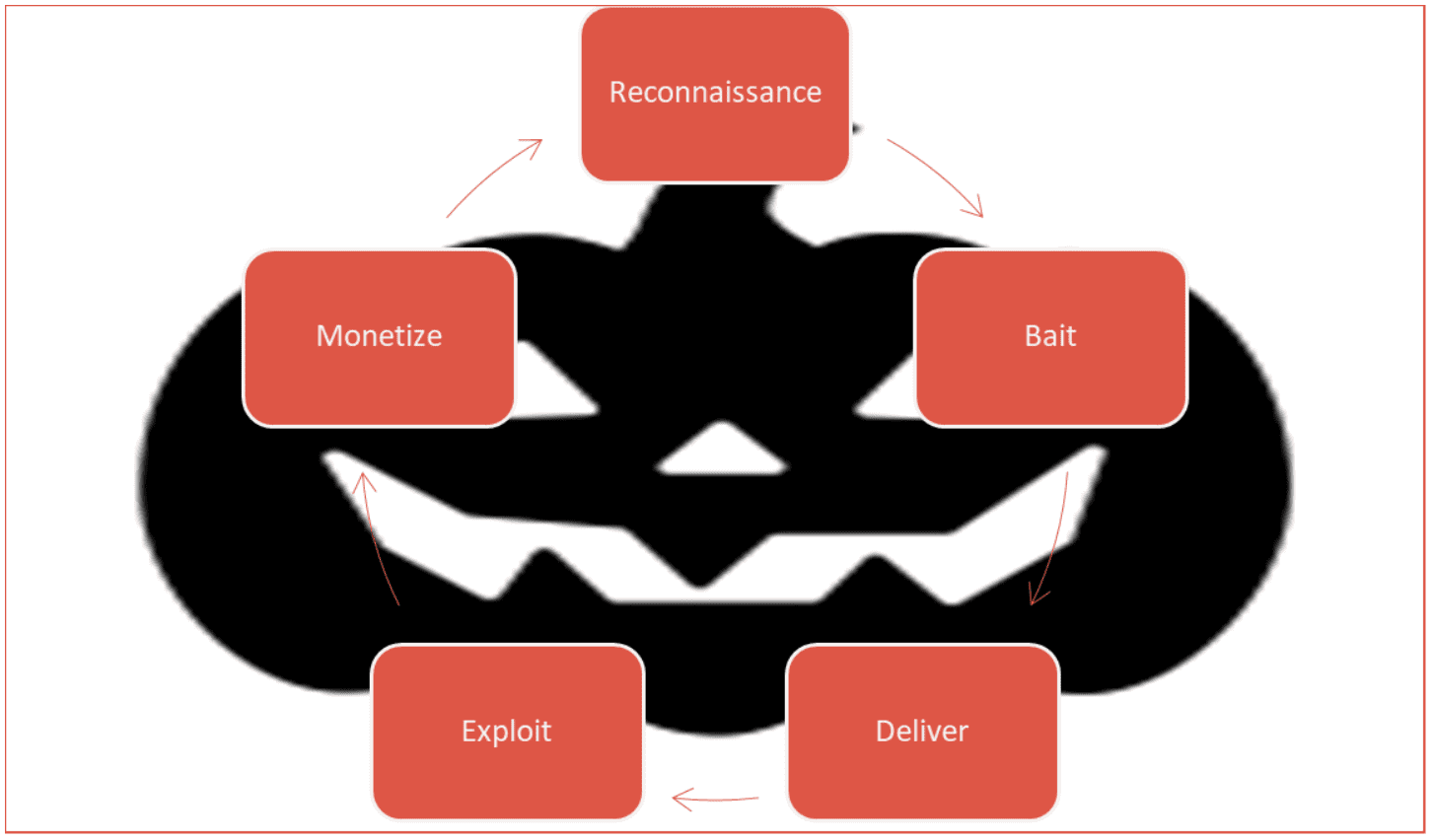
Figure 5: Phishing Campaign Cycle
Attackers will start with the reconnaissance phase, conducting research usually through open channels or stolen data to find information about the intended targets. Then they create the bait – using a phishing kit or AI they will create a message that they think will hook the target and bypass spam filters. They use the information they found during the reconnaissance phase to make it as believable as possible.
Next comes the delivery phase. Depending on what they are trying to achieve there are multiple delivery methods that can be used such as email, SMS, QR codes and even phone calls. In some cases, actors will use multiple channels as part of their attacks to increase the success rate.
The Exploit phase requires input from the victim to be successful. A victim will click on a link or provide credentials to a phishing site or inadvertently install malware on their computer. These credentials are then used by the attackers to conduct further attacks. But the information can be monetized further by selling the stolen information or access to other actors on the dark web – continuing the cycle of phishing attacks.
New Scary Technologies: AI + Phishing = Mass-Targeting on Steroids
Generative AI has already begun to improve the quality, personalization, and scale of phishing. Platforms and toolkits that combine text generation with campaign automation create highly convincing lures that are difficult for users (and sometimes filters) to distinguish from real messages.
A new class of underground offerings — some reported under names like “SpamGPT” — pair natural language generation with mailing infrastructure and analytics, effectively giving attackers a polished marketing stack for phishing.
The net effect: phishing no longer requires good writing skills or deep technical know-how. It requires money (often small) and an account on an underground marketplace. That democratization of attack capabilities is why credential theft and phishing success rates have jumped in recent reporting.
How to Stop Being Tricked
For Organizations
- Multi-factor authentication (MFA) everywhere — reduces the value of stolen passwords even if credentials leak. (Use phishing-resistant MFA like hardware keys where possible.)
- Email protections + DMARC/DKIM/SPF + advanced detection — deploy and tune anti-phishing gateways, URL detonation, and link rewriting. Train filters to use behavior signals (login geography, device fingerprinting).
- Phishing simulations + continuous user training — recurring, contextual training that adapts to current phishing themes reduces click rates. Combine simulated attacks with coaching, not just shame.
- Dark-web monitoring & rapid credential-remediation — monitor for leaked credentials or company data; have a playbook to force resets and contain exposed accounts.
- Least privilege + segmentation + strong logging — limit how far a single compromised account can go; log and monitor anomalous account activity for fast detection.
For Individuals (Easy Wins)
- Use a password manager and unique passwords for every site.
- Turn on MFA (preferably an authenticator app or hardware key).
- Hover before you click — inspect links, check sender addresses for subtle typos, and don’t enter credentials after arriving at a link from an email.
- Treat SMS and phone callbacks as suspicious for requests about credentials or money; verify independently.
- If you click or think you’re compromised — change passwords from a known-good device, enable MFA, run a full malware scan, and notify your employer or bank.
Conclusion
Phishing and social engineering are the silent spooks in the house: they don’t break doors in—they get invited. And when the dark-web toolkit makes it easy, the threats multiply. This Halloween, treat your security like locking the door and checking the candy.
Phishing is deceptively simple, but the underground economy and fast-moving AI technology have turned it into an industrialized threat. The good news: many countermeasures are straightforward and inexpensive (MFA, password hygiene, basic email controls). Don’t take a bite of the candy unless you’re sure it’s your friend handing it. Treat yourself to security hygiene; don’t let the attacker trick you with something sweet.
Keep up with us! Follow us on LinkedIn!
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















