Dark Web Reactions to the Israel–Iran Conflict
March 09, 2026
On 28 February 2026, the United States and Israel launched airstrikes against Iran targeting key military commanders, nuclear facilities, and government infrastructure. The attacks reportedly resulted in the death of Supreme Leader Ali Khamenei, along with several senior officials. Iran immediately retaliated using drones and missiles against U.S. bases in the region as well as targets in Israel. Missile strikes were also reported in Saudi Arabia, the UAE, and Qatar. The conflict continues to escalate, with the U.S. government reportedly pursuing regime change while Iran seeks to demonstrate regional military capability.
As these real-world events unfold, communities on the dark web and adjacent platforms have also reacted to the conflict. Some groups have participated in cyberattacks, others have provided commentary, and many have used messaging platforms such as Telegram to share real-time updates. This blog explores reactions observed across these ecosystems.
Hacktivist Groups
Hacktivist groups are online collectives or loosely organized networks that use hacking or disruptive digital tactics to promote a political, social, or ideological cause. These groups have become increasingly visible on platforms such as X (Twitter) and Telegram, where they seek notoriety for their activities, particularly during major geopolitical events such as the conflict in Ukraine and the October 7 attacks in Israel. The strikes against Iran have similarly prompted increased hacktivist activity.
Common attack types associated with hacktivist groups include:
• Distributed Denial of Service (DDoS) attacks: overwhelming a website or online service with large volumes of traffic, rendering it slow or unavailable to legitimate users.
• Website defacement: compromising a website and replacing its content with propaganda, slogans, threats, or political messaging.
• Data leaks: hackers steal and publish emails, documents, or internal files to embarrass or expose targeted organizations.
Although other types of cyber activity may occur, these represent the primary tactics observed among the hacktivist groups tracked by DarkOwl.
There has been a noticeable increase in hacktivist activity following the airstrikes on Iran, with many groups taking sides and targeting organizations or countries they perceive to be involved in the conflict. Several groups that previously supported pro-Palestinian causes have also opposed the strikes on Iran due to their broader opposition to Israel.
According to a recent report from Radware, 110 organizations were targeted across 149 hacktivist-driven DDoS attacks in the immediate aftermath of the U.S.-Israel campaign against Iran. Of these incidents, 107 were targeted entities in the Middle East, primarily focusing on public infrastructure and government institutions.
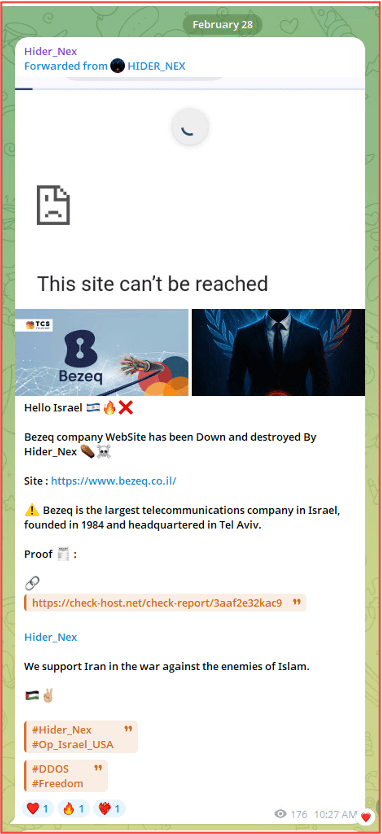
The Tunisian hacktivist group Hider Nex posted on 28 February, after a 10-day hiatus, claiming to have launched an attack against an Israeli telecommunications company in response to the strikes on Iran. The activity appeared to involve a DDoS attack. In their messaging, the group stated they “support Iran in the war against the enemies of Islam.”
The group has continued to target organizations in Israel. However, while conducting these attacks, they have also attempted to sell DDoS services and alleged Israeli data leaks, suggesting their motivations may be partly financial rather than purely ideological.
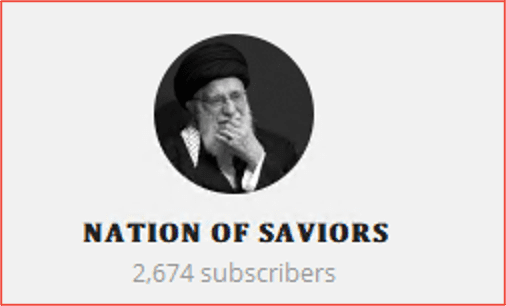
Another hacktivist group, Nation of Saviors, changed its Telegram profile image to depict the deceased Iranian Supreme Leader.
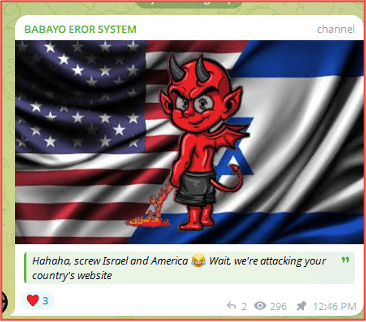
A Russian-affiliated hacktivist group known as Babayo Eror System began posting on 1 March, claiming attacks against U.S. and Israeli websites.
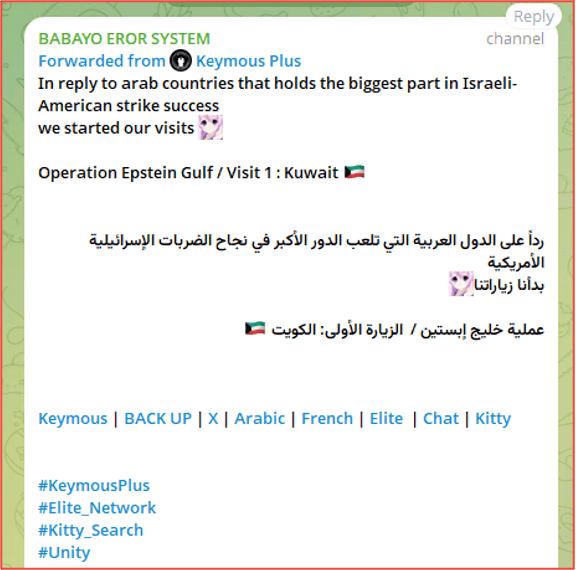
The group has also reposted content from Keymous+, a pro-Russian collective that has issued threats against Gulf states, arguing that these countries stand to benefit from U.S. and Israeli strikes on Iran. The group has framed these activities under the hashtag #Op_Epstein_Gulf, an apparent reference to disgraced financier Jeffrey Epstein.
While most hacktivist groups observed have focused primarily on DDoS attacks and website defacement, some are expanding their messaging to include references to potential targets and reported casualties. Additional information related to this activity is discussed later in this blog.
Many of these groups are also sharing videos and images related to the conflict, as well as commentary from politicians and public figures. While some of this content appears to be AI-generated, other material appears legitimate; however, the authenticity of these images and videos has not been independently verified. Some media also appears to be forwarded directly from news sources.
The mixture of authentic media, reposted news footage, and AI-generated imagery reflects a broader pattern of information amplification and narrative shaping commonly observed in hacktivist online ecosystems.
The group Z-BL4CX-H4T shared a video appearing to show a hanger filled with drones and followed this with posts listing countries they claimed Iran had successfully attacked.

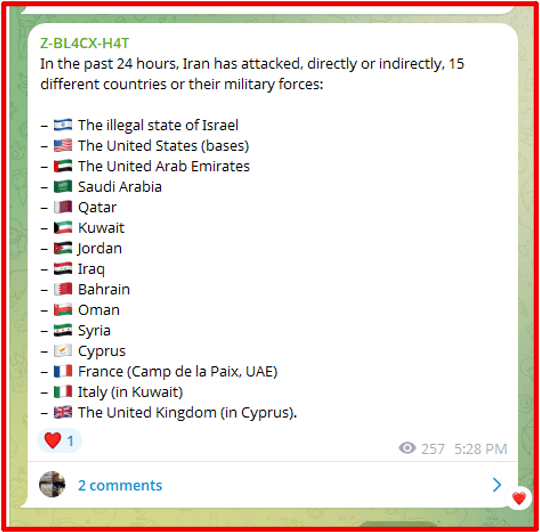
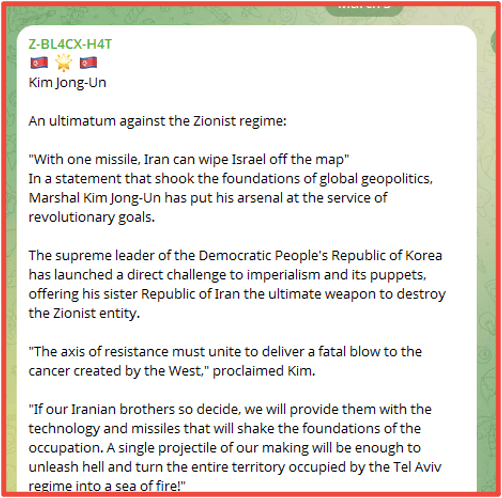
The group also claimed that North Korea was supporting Iran in attacks against US and Israel affiliated sites.
News
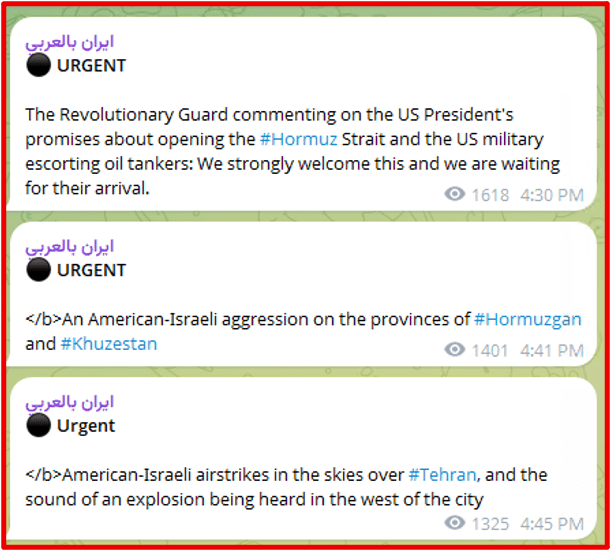
As with previous conflicts, Telegram has become a major source of real-time information sharing. Numerous posts on the platform have circulated footage of missile strikes, images of military equipment, and updates from official organizations.
The Telegram channel ايران بالعربي (Iran in Arabic), which supports the Iranian government, shared images, and video footage of protests allegedly criticizing U.S. imperialism. The post claimed the protest took place in Stockholm, although DarkOwl has not verified the authenticity of these images.

The channel also shared images that appear to show people celebrating in the streets of Tehran.
As during the October 7 attacks, the IDF Telegram channel has been used to share official updates and warnings with Israeli citizens, including guidance on whether residents should take shelter.
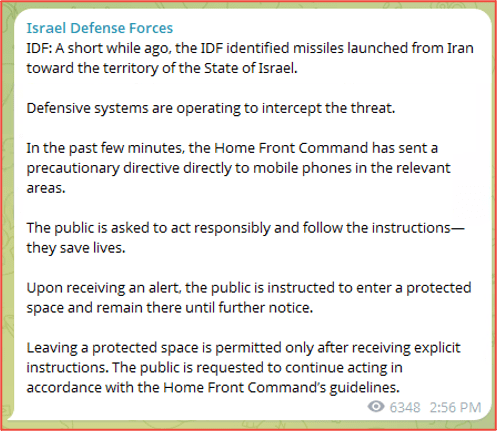
News agencies have also circulated urgent warnings, identifying areas being targeted.
Additional videos circulating on Telegram appear to show damage from airstrikes in civilian areas. These images have not been independently verified by DarkOwl.

Other imagery shared on Telegram attempts to link the conflict in Iran with the ongoing war in Gaza.
Several groups associated with white supremacist ideology have also commented on the conflict.
One group stated that while they oppose Israel due to antisemitic beliefs, they also do not support Iran due to its Muslim identity, reflecting their ideological vision of a white, Christian ethno-state.

However, another Telegram channel shared an AI-generated image supporting Iran, which included both the Iranian flag and the Sonnenrad symbol, commonly associated with neo-Nazi and Atomwaffen-affiliated extremist groups.
This example highlights a broader trend in which ideological boundaries are increasingly blurred, particularly among groups linked to Nihilistic Violent Extremism (NVE).
Islamic Extremist & Jihadist Responses
DarkOwl monitors a range of Telegram and Rocket.Chat channels used by jihadist groups and their supporters, including communities linked to ISIS and al-Qaeda. Early reactions to the Israel–Iran conflict have emerged across these platforms.
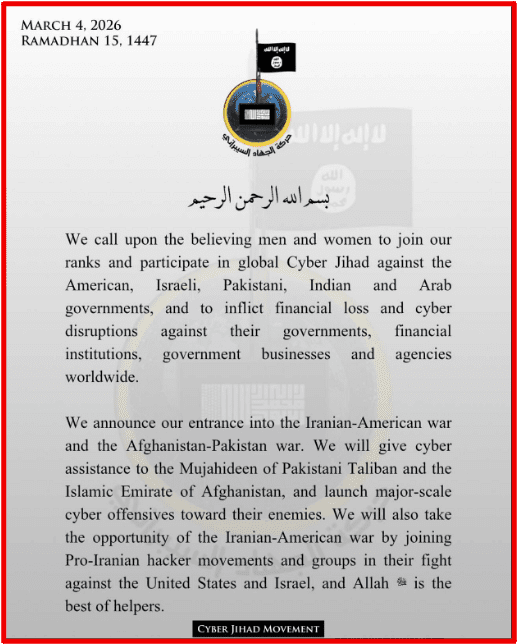
A statement attributed to a group calling itself the Cyber Jihad Movement was identified on March 4, 2026, by counterterrorism researchers. The English-language document presents the group as an “IT organization linked to al-Qaeda” and calls on supporters to participate in what it describes as a “global cyber jihad.”
The statement encourages technically skilled supporters to conduct cyber operations targeting the governments and institutions of the United States, Israel, Pakistan, India, and several Arab countries, including cyberattacks designed to disrupt financial systems and government infrastructure.
The document also announces the group’s “entry” into the Iran–United States conflict and the Afghanistan–Pakistan conflict, expressing support for the Pakistani Taliban (TTP) and the Islamic Emirate of Afghanistan (Taliban).
While there is currently no public evidence of operational capability associated with the Cyber Jihad Movement, the messaging reflects ongoing attempts by jihadist-aligned actors to frame cyber activity as a legitimate extension of militant struggle.
Supporters of the Islamic State also discussed the conflict on an unofficial Rocket.Chat server historically used by IS sympathizers.
Users shared reactions to early reports of the conflict, often expressing hostility toward Iran and Shia Muslims.
Some users suggested that prolonged military pressure on Iran could create opportunities for expansion by Islamic State Khorasan Province (ISKP).
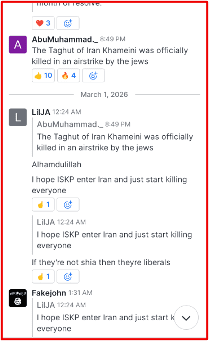
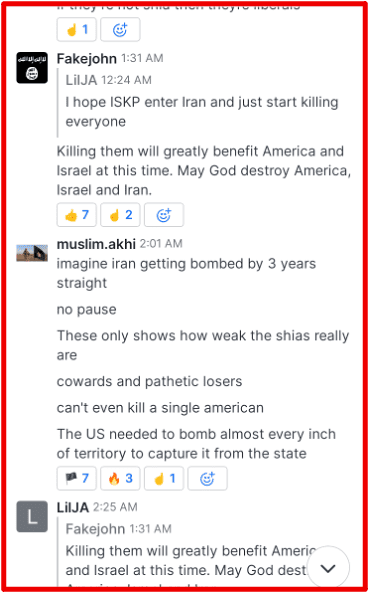
Some participants framed the conflict as validation of Islamic State narratives about its ability to challenge global powers.
Discussion on the server also revealed growing paranoia about infiltration by researchers and law enforcement, particularly following arrests linked to previous administrators of the community.
These conversations illustrate how jihadist communities interpret geopolitical events through ideological narratives while simultaneously dealing with internal distrust and operational pressure.
Iranian Aligned Militia Responses
Iranian-aligned militia groups across Iraq and the broader “Axis of Resistance” ecosystem have also used Telegram channels to shape narratives surrounding the conflict, combining operational claims, ideological messaging, and propaganda directed at regional and Western audiences.
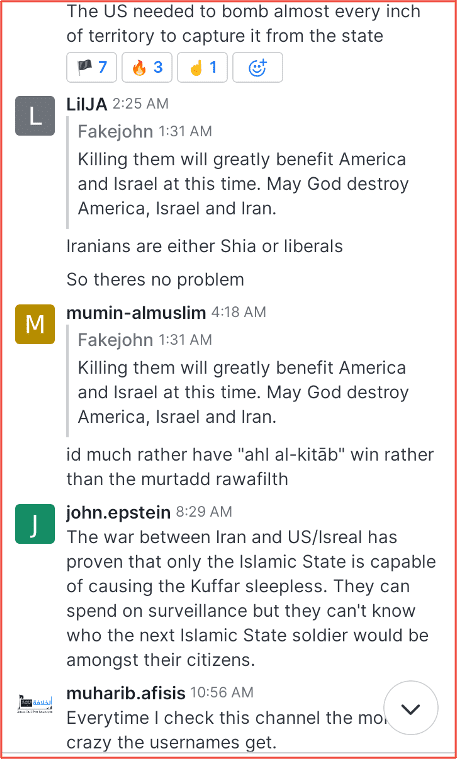
Safwa Unit (Kata’ib Hezbollah)
The group وحدة الصفوة (Safwa Unit), which claims affiliation with Kata’ib Hezbollah, has circulated graphics identifying alleged Israeli targets, including Israeli officials and public figures.
The channel has also shared imagery commemorating individuals it describes as Hezbollah “martyrs.”
Such messaging blends propaganda and intimidation and reflects a broader pattern of militant-aligned channels using visual propaganda to signal potential targets while reinforcing narratives of resistance.
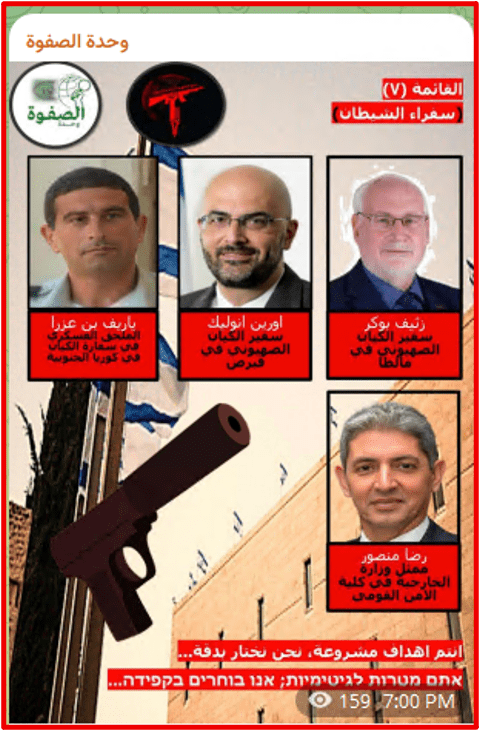
Ashab al-Kahf (PMF / Kata’ib Sarkhat al-Quds)
Another Telegram channel monitored by DarkOwl is أصحاب الكهف (Ashab al-Kahf), affiliated with Iraqi Popular Mobilization Forces (PMF) factions including Kata’ib Sarkhat al-Quds (كتائب صرخة القدس).
Recent posts on the channel have focused on the conflict and tensions involving U.S. forces.
One statement claimed responsibility for targeting a U.S. military base in Kuwait using drones, warning that operations would escalate.

Other posts emphasized ideological alignment with Iranian Supreme Leader Ali Khamenei, framing the conflict as part of a broader struggle against Western influence.
The channel also shared stylized propaganda imagery depicting Khamenei in militant imagery.
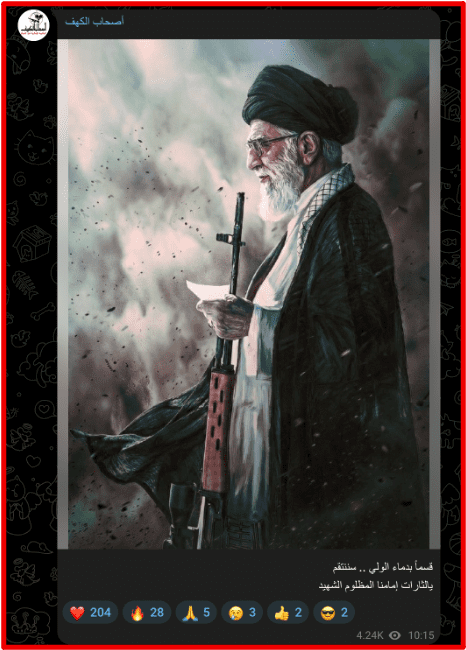
Taken together, this content illustrates how Iranian-aligned militia channels blend operational claims, ideological messaging, and propaganda to frame regional conflict narratives.
Conclusion
Communities across the dark web and adjacent platforms are actively reacting to the escalating conflict between Iran, Israel, and the United States. These reactions vary widely depending on the ideological orientation of each community.
Hacktivist groups have attempted cyberattacks against perceived adversaries; news channels have used Telegram to disseminate real-time updates, and extremist communities have leveraged the conflict to amplify propaganda narratives.
As the conflict continues to evolve, online discourse within these ecosystems will shift alongside real-world developments. DarkOwl will continue monitoring these platforms for emerging threats, cyber activity, and extremist messaging related to the conflict.
Follow us on LinkedIn to stay up to date.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















