[Developing] BreachForums’ Alleged Admin Pompompurin Arrested, Dark Web Reacts
Last Updated 28 March 2023 – 23:09 UTC
28 March 2023 – 23:09 UTC
Connor FitzPatrick Appears in Court
Last week we reported that an individual alleged to be the administrator of the dark web forum BreachForums was arrested in New York. On Friday, March 24, Connor FitzPatrick appeared in court charged with facilitating the unauthorized purchasing and selling of stolen identification documents, unauthorized access devices, unauthorized access to victim computer systems and login credentials.
What is really interesting is how the FBI were able to identify FitzPatrick as Pompompurin. It seems from the affidavit provided in court that Fitzpatrick made several mistakes that ultimately led to his downfall. Proving that human error is a big factor in the attribution of cyber criminals.
FitzPatrick logged on to both BreachedForums and its predecessor RaidForums from IP addresses which were registered to his parent’s home address. Furthermore, he also made access to these forums and cryptocurrency wallets, exclusively funded by the bitcoin address linked to Pompompurin’s account, from a mobile device registered in his name. What’s more, Fitzpatrick provided his real email address to the admin of RaidForums, as proof that a breach he had purchased was not complete. Although he stated this was not his address a fact that was identified by the FBI when they were able to seize RaidForums in early 2022.
Upon his arrest FitzPatrick claimed that he earned approximately $1,000 a day from his activities on BreachForums which he mainly used to maintain the forum – one wonders if this was worth the 5 years in prison he is likely to receive.
March 21, 2023
Almost exactly a week ago on March 15, 2023, an admin of the popular darknet and deep web site BreachForums who goes by the alias Pompompurin was arrested in Peekskill, NY. In this blog, DarkOwl analysts review what has happened to date and will continue to the monitor the situation and update this blog accordingly.
Pompompurin Identified and Arrested
Pompompurin has been identified as US citizen Conor Brian FitzPatrick. FitzPatrick was charged with one count of conspiracy to commit access device fraud and bail was set at $300,000 – paid for by his parents.
After news of the arrest broke publicly on March 17th, the reaction on BreachForums was quick, with members scrambling to find out what had happened and concern that the forum had been taken over by the FBI in a similar way to what happed with RaidForums. Raidforums was seized by the DOJ in April 2022 and had been taken over by them previous to the announcement of the arrest of the alleged administrator “Omnipotent” – Diego Santos Coelho.
Thread chatter on the soon-to-be defunct forum revealed members questioning if the news of Pompompurin’s arrest was real – even pointing to their user activity being “away” for the 48 hours beforehand as evidence that the news was in fact accurate.
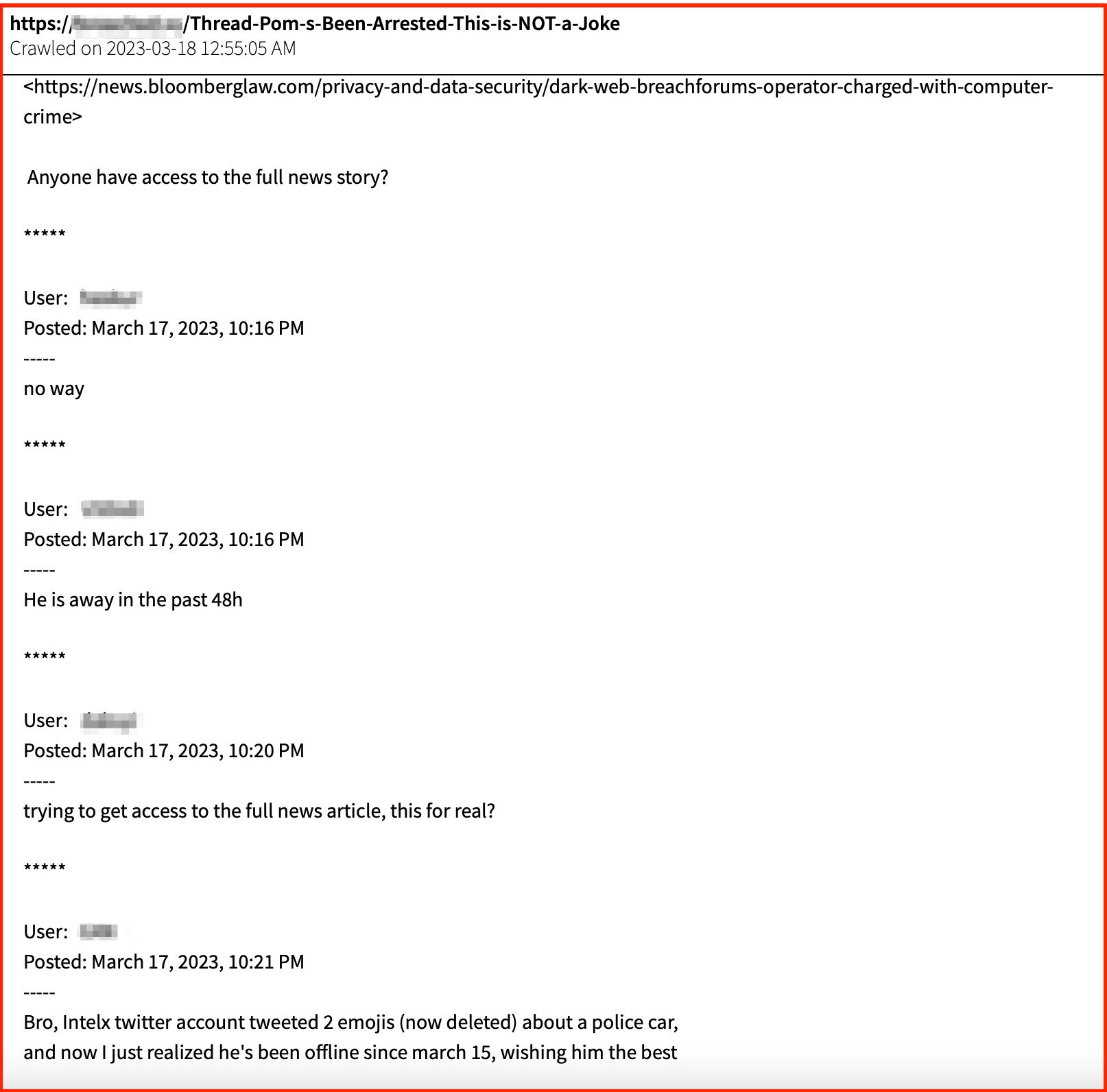
Figure 1: Users on BreachedForums discussing the news announcement of its administrator’s arrest, Source: DarkOwl Vision
The users of BreachForums wanted to know if they could delete their accounts to avoid meeting the same fate as Pompompurin at the same time that they seemed to be discovering that he had been arrested. They posted elements of reporting as well as details of FitzPatricks’s true identity.
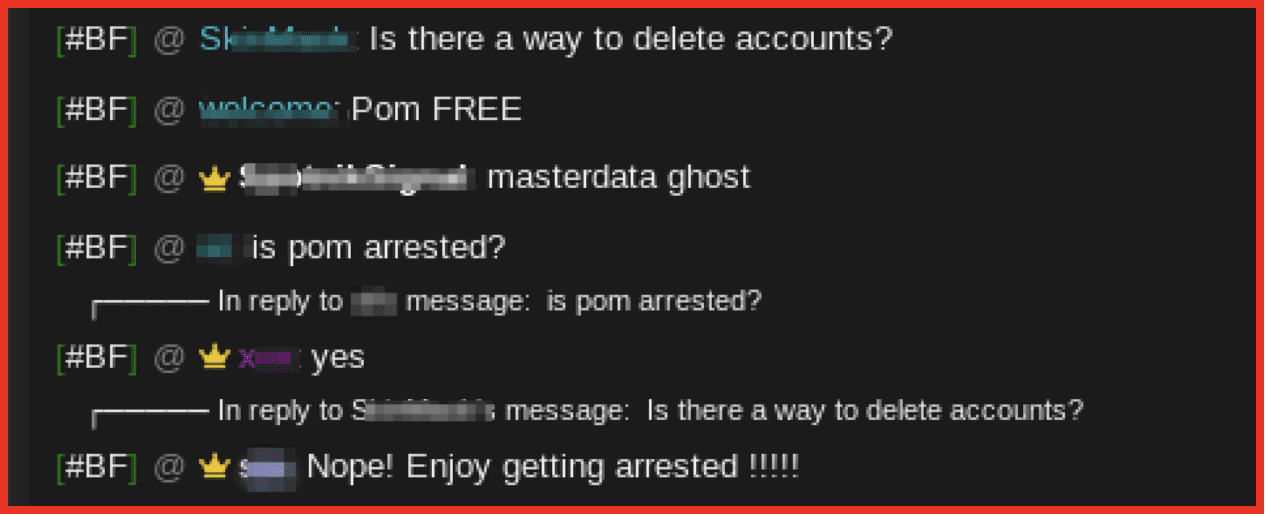
Figure 2: Users of BreachForum discussing arrest, Source: Breachforums
BreachForums emerged in April 2022 in the wake of the takedown of RaidForums, and allowed users to buy and sell data which had been obtained through illegal means. The admins of the site ran an escrow service ensuring that sellers received the funds that they had requested. The site was widely used by cybercriminals to purchase stolen data and hosted controversial leaks such as data stolen from the Washington DC healthcare exchange.
Pompompurin was also known to conduct cyber-attacks himself, admitting in an interview with Brian Krebs in November 2021 that he was responsible for sending fake emails using the fbi.gov domain. He claimed at the time this was done to point out vulnerabilities in the FBI systems, but it undoubtably put him higher on the FBI’s radar leading to his recent arrest.
Interestingly when Pompompurin was arrested, he admitted to his role as admin on BreachForums and the use of this alias.
“When I arrested the defendant on March 15, 2023, he stated to me in substance and in part that: a) his name was Conor Brian FitzPatrick; b) he used the alias ‘pompourin,’ and c) he was the owner and administrator of ‘BreachForums,’ the data breach website referenced in the Complaint,” FBI special agent John Longmire testified.
This fact does not appear to have been looked on favorably by users of his forum, with discussions turning to how to evade the FBI by living in a different country than the US and not attacking US companies from within the US.
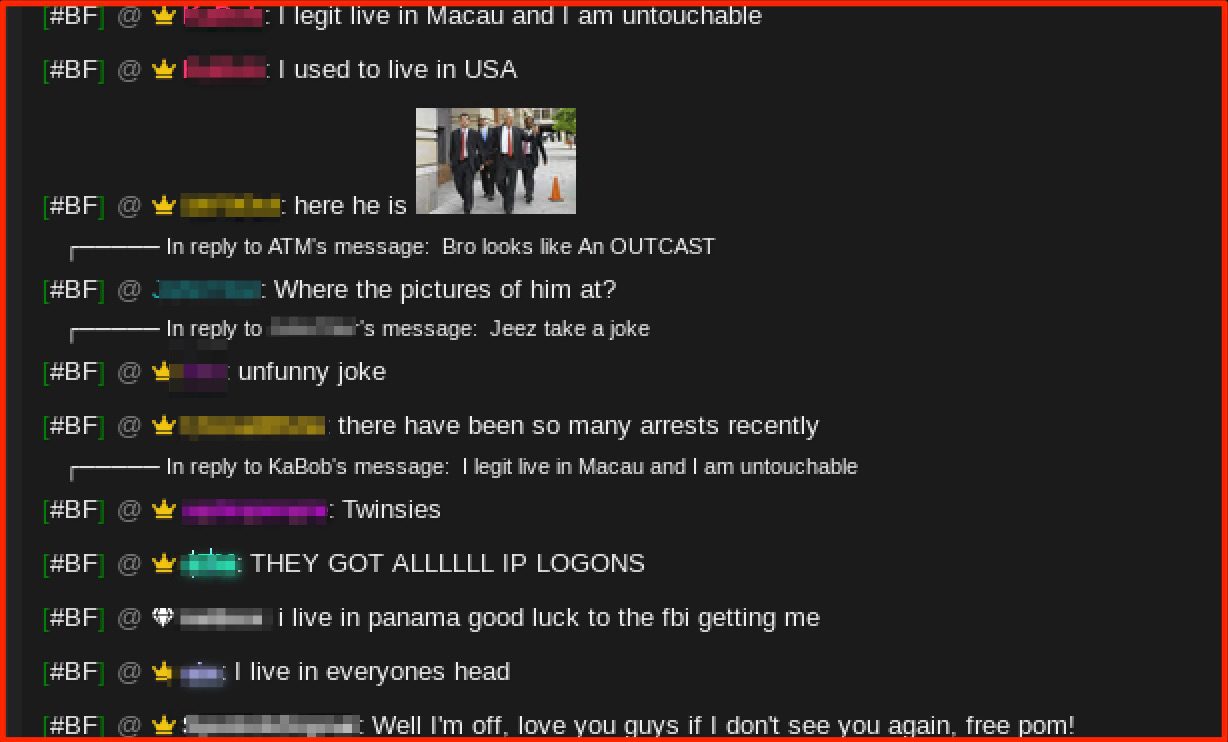
Figure 3: Discussions on how to evade the FBI, Source: BreachForums
On the other side, numerous users appeared to have some sympathy for “Pom” (as he is commonly referred to), with some stating that he was one of the nicest admins they had ever worked with and that he would delete accounts if you asked nicely.
One user even volunteered responsibility for any content they hosted on the dark web forum, ostensibly to alleviate potential legal trouble on Pom‘s behalf
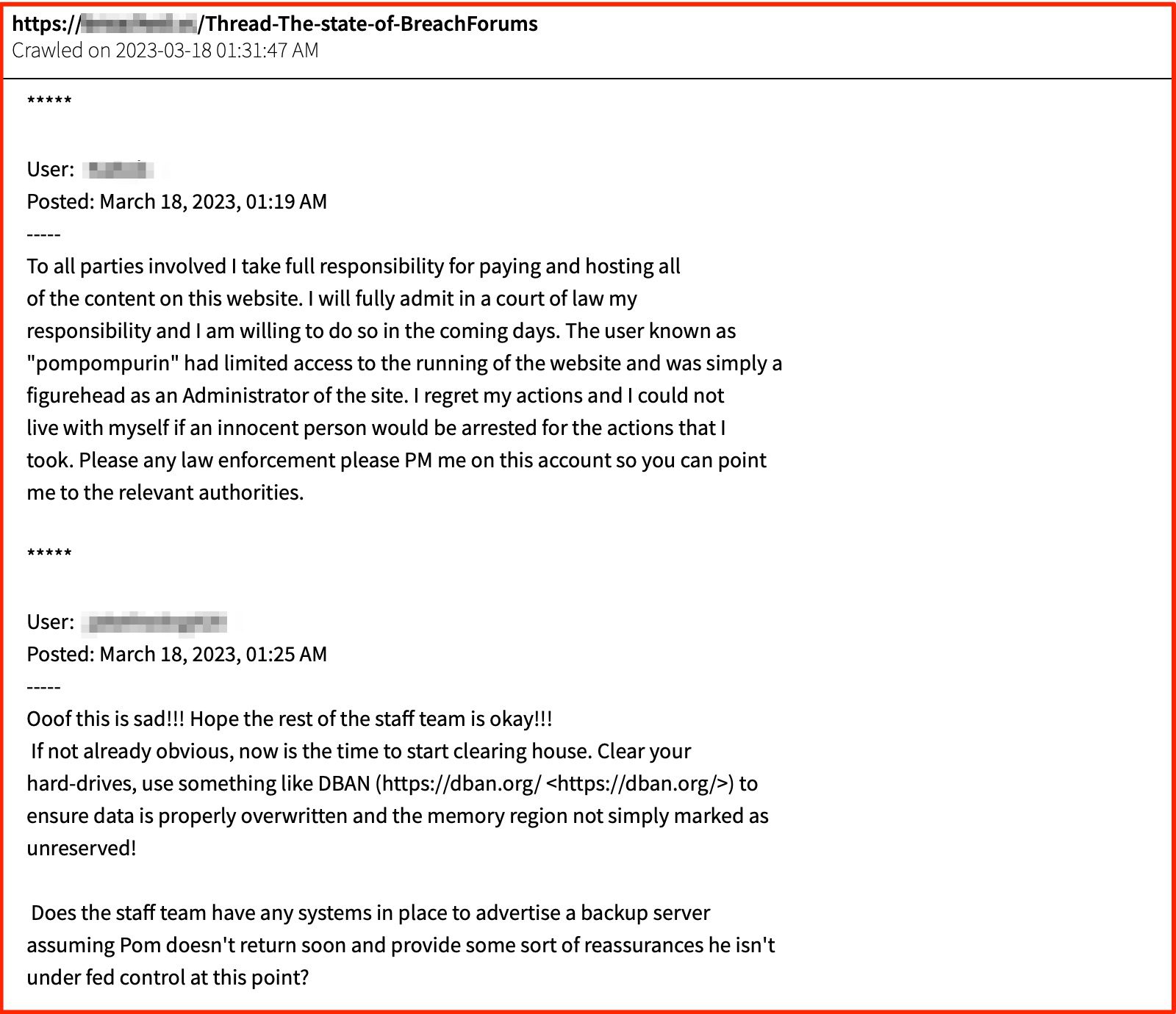
Figure 4: BreachForums posts from users attempting to mitigate legal fallout for their former admin, Source: DarkOwl Vision
Others offered to support him financially in his time of legal trouble.
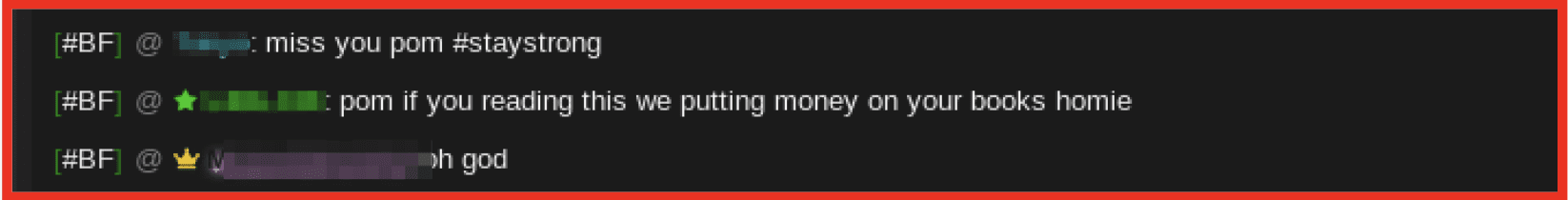
Figure 5: Users voice words of support among the fallout, Source: BreachForums
Discussion also centered around how it was that the FBI were able to identify the true identity of Pom with fingers being pointed at an open source intelligence company, with whom Pom had apparently registered. With threats being made to attack that company.
They also showed concern about whether Pompompurin would share any information or become an informant with the “feds” with users being worried that their registration information would be found by the FBI.
BreachForums had a co-admin who indicated that the FBI may have been able to access the systems if Pompompurin had shared this information or left his computer open when his parents home was raided.
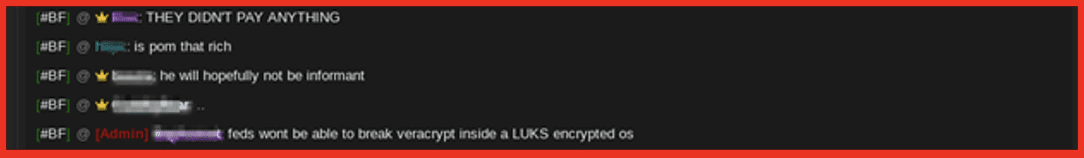
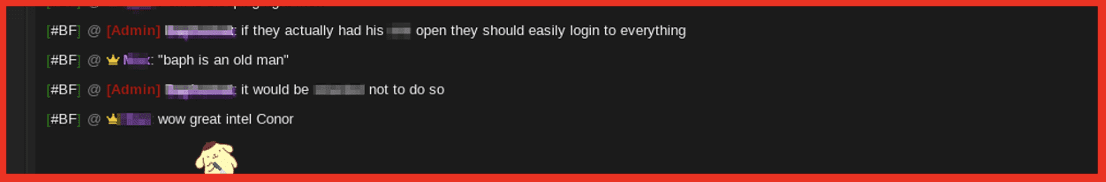
Figures 6 and 7: More chatter around the potential fallout – including FBI involvement, Source: BreachForums
It was quickly shared that all of Pompompurin’s access had been disabled and that the co-admin was checking to see if they could confirm that the FBI were able to infiltrate the site.
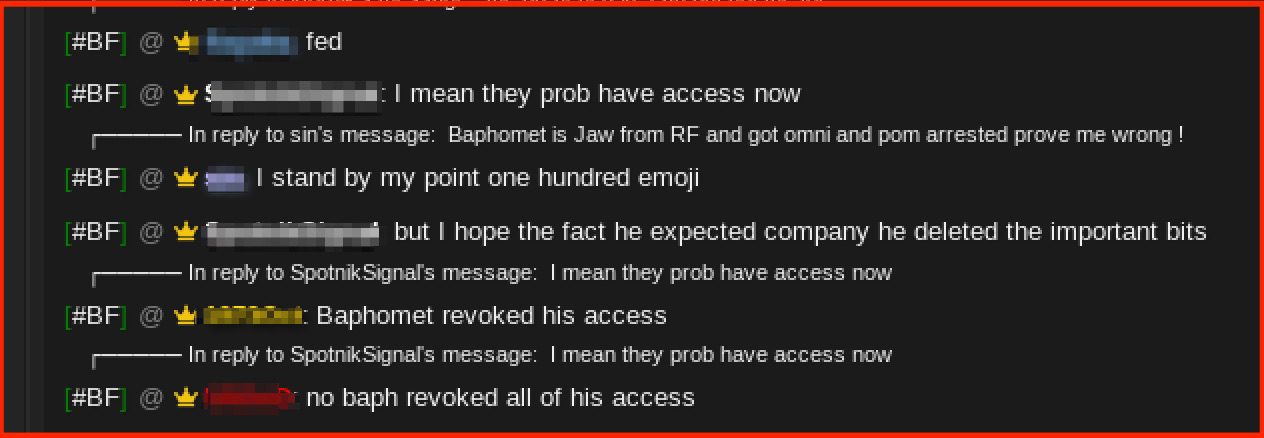
Figure 8: BreachForum’s co-admin chatting about checking FBI access, Source: BreachForums
While the discussions remained largely focussed on potential risks for the remaining active users, others continued to point to a grassroots effort to protect Pom from Law Enforcement Operations.
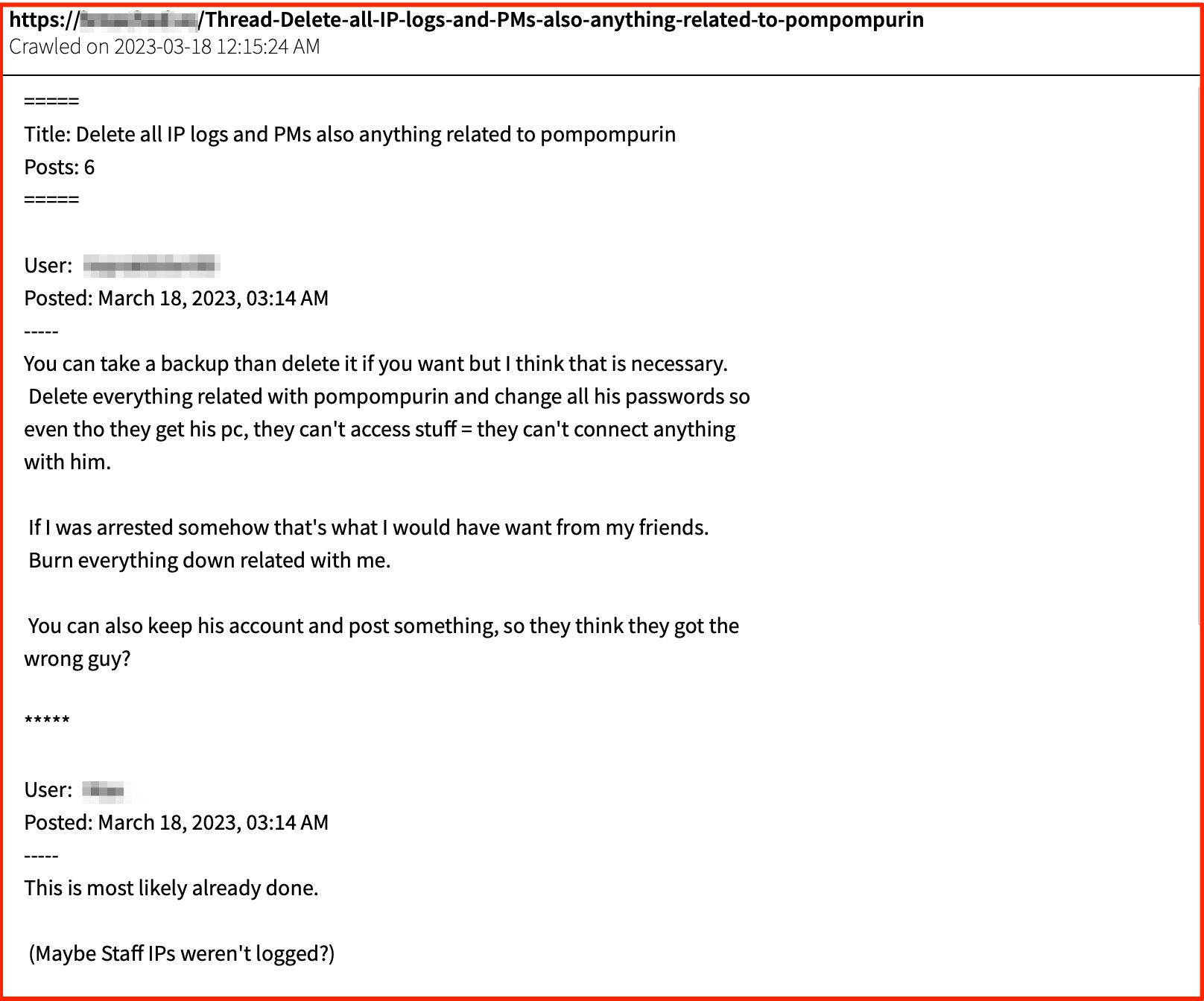
Figure 9: Discussions around how to remove logs and other digital evidence tying Pompompurin to BreachForums, Source: DarkOwl Vision
On Sunday the admin “Baphomet” announced that he would be closing down Breach Forums as he was concerned that the FBI did in fact have access. He posted on the groups telegram channel as well as posting a more complete message explaining his decision.
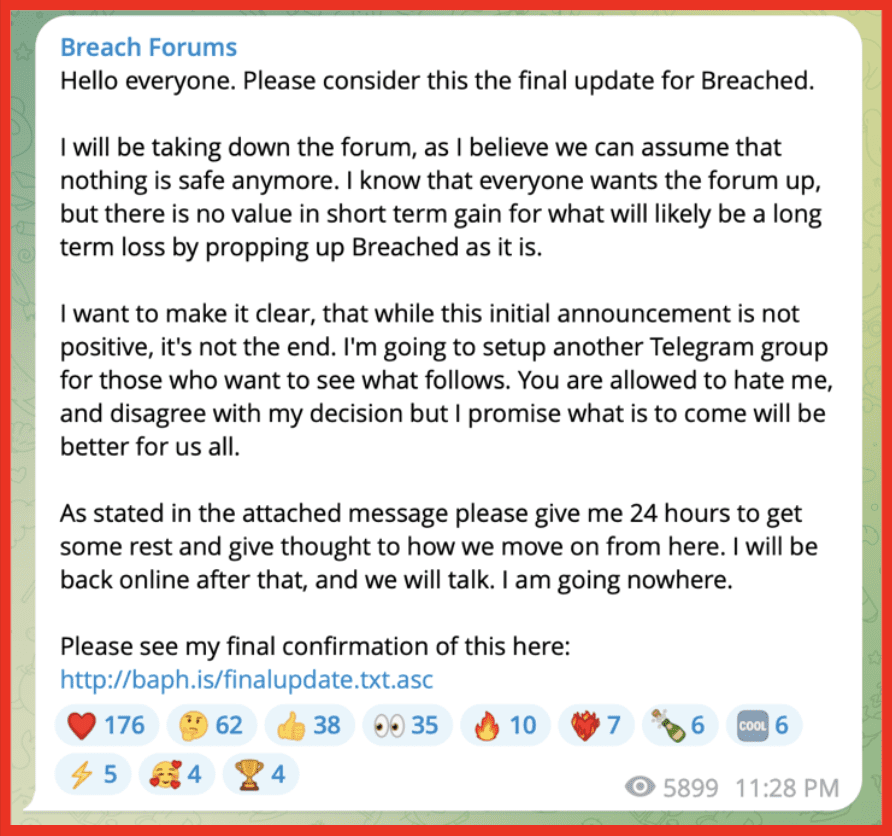
Figure 10: Breach Forums closing down announcement, Source: Telegram
Interestingly, he stated that the Telegram channel would maintain operation and that he was looking to create new infrastructure which would replace BreachForum even working with competitor marketplaces. As of writing, the onion site has been taken down and is unreachable.
DarkOwl will continue to monitor the dark web and adjacent sources such as Telegram to identify any new of emerging groups and sites which may take the place of BreachForums. Stay up to date.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















