Threat Intelligence RoundUp: August
September 01, 2023
Our analyst team shares a few articles each week in our email newsletter which goes every Thursday. Make sure to register! This blog highlights those articles in order of what was the most popular in our newsletter – what our readers found the most intriguing. Stay tuned for a recap every month. We hope sharing these resources and news articles emphasizes the importance of cybersecurity and sheds light on the latest in threat intelligence.
1. US Gov Rolls Out National Cyber Workforce, Education Strategy – Security Week
At the very end of the month, the Biden administration announced the National Cyber Workforce and Education Strategy (NCWES). This comes as the gap in talent needed to fill cybersecurity jobs remains. The new strategy will include a series of “generational investments” to address the cyber workforce needs, starting with education and making training more accessible. Read full article.
2. Researchers Expose Space Pirates’ Cyber Campaign Across Russia and Serbia – The Hacker News
Research has revealed that Space Pirates, a threat actor linked to attacks against at least 16 organizations in Russia and Serbia over the past year, has been harvesting PST email archives and making use of Deed RAT – showing that they are adding new cyber weapons to their TTPs but their main goals are still espionage and theft of confidential information. Read more.

3. Cuba ransomware group observed exploiting high-severity Veeam bug – SC Media
Cuba ransomware group exploits Veeam bug, targets CIKR. The Cuba ransomware group is actively exploiting CVE-2023-27532, which allows for procurement of stored encrypted credentials. Furthermore, their increase of activity allowed for deeper analysis revealing that the ransomware terminates if Russian language packs or the Russian keyboard is detected, likely indicating this is another Russia-based group. Read more.

4. Attackers Dangle AI-Based Facebook Ad Lures to Hijack Business Accounts – Dark Reading

Credentials were stolen after a Facebook advertisement promised to boost business productivity and revenue using the latest trends in AI. TrendMicro discovered the false Facebook pages and alerted Meta, who took the pages down. Clicking on the false ads led unsuspecting users to an LLM-themed website, which then stole cookies, browser information, user access tokens, and other sensitive data. Community researchers compared this latest campaign to the spring 2023 RedLine stealer campaign. Read full article.
5. Syrian Threat Actor EVLF Unmasked as Creator of CypherRAT and CraxsRAT Android Malware – The Hacker News
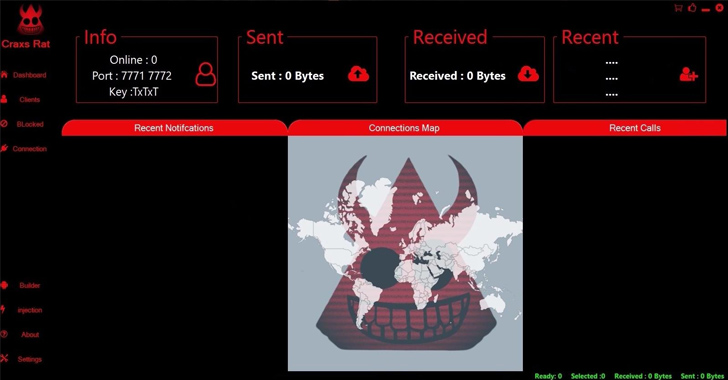
Syrian threat actor EVLF reportedly authored several Android remote access trojans (RATs) which he sold on a marketplace since 2022. The RATs can control device cameras and microphones. EVLF runs several Telegram channels in addition to selling on marketplaces. He posted on 23 August 2023 that he would be shutting down, presumably after being publicly outed by the media. Read more.
6. North Korean Affiliates Suspected in $40M Cryptocurrency Heist, FBI Warns – The Hacker News
The US FBI issued a statement indicating that individuals linked with North Korea could make efforts to convert pilfered cryptocurrency valued at over $40 million into actual funds. They attributed the blockchain activity to TraderTraitor, aka Jade Sleet. Read full article.
7. CISA Adds One Known Exploited Vulnerability to Catalog – CISA
CVE-2023-24489 Citrix Content Collaboration ShareFile Improper Access Control Vulnerability has been added. Learn more.
Make sure to register for our weekly newsletter to get access to what our analysts are reading on a weekly basis.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















