Threat Intelligence RoundUp: July
August 04, 2025
Our analyst team shares a few articles each week in our email newsletter which goes every Thursday. Make sure to register! This blog highlights those articles in order of what was the most popular in our newsletter – what our readers found the most intriguing. Stay tuned for a recap every month. We hope sharing these resources and news articles emphasizes the importance of cybersecurity and sheds light on the latest in threat intelligence.
1. Ukraine arrests suspected admin of XSS Russian hacking forum – Bleeping Computer

In a July 23 press release, French authorities announced the arrest of the alleged administrator of the notorious, Russian cybercrime forum XSS. According to the announcement, the suspect was arrested in Kyiv, Ukraine, by Ukrainian authorities on July 22 in the presence of French police and with support from Europol. The investigation was launched four years ago, on July 2, 2021, by the cybercrime division of the Parquet de Paris (the Public Prosecutor’s Office). In addition to the arrest in Ukraine, authorities also seized the XSS.is domain. As noted by Hackread, following the action the site featured a seizure notice stating that the domain had been seized by French law enforcement. Read full article.
2. Android malware Anatsa infiltrates Google Play to target US banks – Bleeping Computer

Researchers at ThreatFabric have identified a new Android banking malware campaign which utilizes the Anatsa Android banking trojan. According to the report, the campaign is targeting North American users and posed as a PDF viewer app in the U.S. Google Play Store; it was downloaded over 50,000 times before being removed. The app was initially launched as a legitimate app before being “transformed into a malicious one approximately six weeks after release.” The latest campaign is notably characterized by a broadened target list including a range of American mobile banking apps. Article here.
3. Iranian-Backed Pay2Key Ransomware Resurfaces with 80% Profit Share for Cybercriminals – The Hacker News
Researchers at Morphisec have observed the resurgence of the Iranian-backed ransomware-as-a-service (RaaS) “Pay2Key.” The company’s report—released just a month after Israel launched attacks against Iran’s nuclear and military facilities—reveals that the scheme now operates as “Pay2Key.I2P” and offers a greater profit share to those who target Iranian adversaries. As noted by the researchers, “the group offers an 80% profit share (up from 70%) to affiliates supporting Iran or participating in attacks against the enemies of Iran, signaling their ideological commitment.” Read more here.
4. China-Based APTs Deploy Fake Dalai Lama Apps to Spy on Tibetan Community – The Hacker News
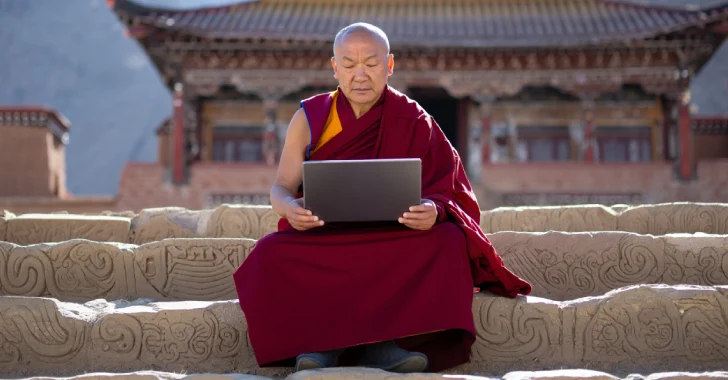
In a July 23 report published by Zscaler ThreatLabz, researchers attributed two cyberattack campaigns against the Tibetan community to a China-linked APT group. The two campaigns—dubbed Operation GhostChat and Operation PhantomPrayers—targeted Tibet with multi-stage infection chains deploying Ghost RAT and PhantomNet backdoors. These attacks capitalized on heightened online activity in the weeks leading up to Dalai Lama’s 90th birthday on July 6. The campaigns functioned by “leveraging multiple subdomains […] to impersonate legitimate platforms.” Read here.
5. CISA and FBI warn of escalating Interlock ransomware attacks – Bleeping Computer

On July 22, the Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Agency (CISA), Department of Health and Human Services (HHS), and Multi-State Information Sharing and Analysis Center (MS-ISAC) released a cybersecurity advisory warning of the ongoing threat posed by Interlock ransomware. According to the report, the relatively new ransomware operation has targeted a variety of sectors since it first emerged in September 2024. Targets have included “a wide range of business and critical infrastructure sectors in North America and Europe.” Learn more.
6. FBI seizes $2.4M in Bitcoin from new Chaos ransomware operation – Bleeping Computer
On July 28, Dallas FBI announced the seizure of over $1.7 million worth of cryptocurrency in mid-April 2025. According to the statement, the funds were “traced to a cryptocurrency address allegedly associated with a member of the Chaos ransomware group.” The seized amount has now been valued at over $2.4 million. The alleged member of Chaos has been tied to ransomware attacks carried out against Texas companies and other targets. Read full article.
7. Four arrested in UK over M&S, Co-op, Harrods cyberattacks – Bleeping Computer
In a July 10 press release, the U.K.’s National Crime Agency (NCA) announced the arrest of four individuals for their suspected involvement in a series of cyberattacks against three major retailers (Marks & Spencer, Co-op, and Harrods). According to the statement, the arrested individuals include two 19-year-olds, one 17-year-old, and a 20-year-old. They were arrested on suspicion of “Computer Misuse Act offences, blackmail, money laundering and participating in the activities of an organised crime group.” Read full article.
8. US sanctions North Korean firm, nationals behind IT worker schemes – Bleeping Computer

In a July 24 press release, the U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) announced the sanctioning of the North Korea-based Korea Sobaeksu Trading Company and three associated individuals for their participation in fraudulent remote IT worker schemes. As previously noted in DarkOwl’s Weekly Intelligence Summaries, the DPRK government uses these IT worker schemes to generate illicit revenue. The IT workers involved in the scheme use “fraudulent documents, stolen identities, and false personas to obfuscate their identities and infiltrate legitimate companies.” Learn more.
Make sure to register for our weekly newsletter to get access to what our analysts are reading on a weekly basis.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















