Threat Intelligence RoundUp: September
October 02, 2023
Our analyst team shares a few articles each week in our email newsletter which goes every Thursday. Make sure to register! This blog highlights those articles in order of what was the most popular in our newsletter – what our readers found the most intriguing. Stay tuned for a recap every month. We hope sharing these resources and news articles emphasizes the importance of cybersecurity and sheds light on the latest in threat intelligence.
1. MGM cyberattack claimed by ALPHV/BlackCat ransom gang – Cybernews
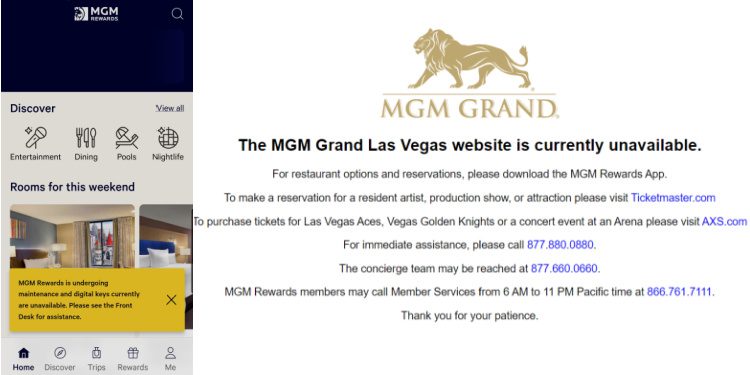
ALPHV/Blackcat ransomware group claimed responsibility for the MGM cybersecurity incident this week. Down slot machines, nonfunctioning key cards, and more services were interrupted at MGM resorts and hotels nationwide. News articles broke Wednesday, 13 September, that ALPHV/Blackcat ransomware gang was responsible. However, DarkOWL analysts went to the ALPHV onion page, and no new data was listed yet. MGM data from 2013 were the only results. On 14 September, new rumors emerged that “Scattered Spider” was also involved in the incident. Scattered Spider is an English-speaking cybercrime group which teamed up with ALPHV in early 2023. Additionally, Scattered Spider hit Caesars Entertainment on 7 September. Caesars paid tens of millions to remain operational and did not experience an outage. Read full article.
2. Hackers backdoor telecom providers with new HTTPSnoop malware – Bleeping Computer
Threat actor group “ShroudedSnooper” has installed HTTPSnoop and PipeSnoop malware throughout Middle Eastern telecom providers. HTTPSnoop imitates legitimate URL patterns and blends into legitimate traffic, making detection very difficult; it also targets public servers. PipeSnoop takes advantage of deeper compromise within networks. No attribution has been discovered regarding the country of origin or intention of ShroudedSnooper. Article here.
3. Payment Card-Skimming Campaign Now Targeting Websites in North America – Dark Reading
Attacks starting in May 2023 (or earlier), by a Chinese-speaking threat actor, has exploited vulnerabilities in Web applications in the Asia/Pacific region. This month, they have expanded their targets into Latin and North America. The attacks involve skimming credit card numbers off ecommerce sites and point-of-sale service providers. Read more.
4. GhostSec Leaks Source Code of Alleged Iranian Surveillance Tool – Dark Reading
Hacktivist group GhostSec revealed the source code from Iran’s FANAP group, a technology conglomerate that has ties to the financial, government, and technology sectors in Iran. The source code reveals facial recognition, GPS and tracking systems, car license plate recognition, and other efforts in the surveillance space. DarkOWL analysts have procured the available files from Telegram. GhostSec established two Telegram channels to share with the media covering this event, as well as the files, stating the second channel was a backup in case the first was shut down. Learn more.
5. Vietnamese Cybercriminals Targeting Facebook Business Accounts with Malvertising – The Hacker News
Cybercriminals are using LinkedIn to find accounts tied to the digital marketing space, and compromising those accounts to use in social engineering incidents. Digital marketing accounts often have high numbers of followers and connections, and these numbers are easier to use to expand credential theft operations and reuse that information in malicious operations. After compromising LinkedIn accounts, the Vietnamese cyber group is using Duckport malware to perform information stealing ops, and then moving to other social media platforms such as Facebook, continuing to steal account credentials and in some instances, cookies, to reuse in the operations. Read full article.
6. Finnish Authorities Dismantle Notorious PIILOPUOTI Dark Web Drug Marketplace – The Hacker News

Law enforcement in Finland, including Finnish customs, announced the takedown of illegal dark web narcotic marketplace, Polopuoti on September 20. The drugs came from abroad into Finland, and this was a joint operation that also involved parties from Germany, Romania, and Lithuania. The marketplace had been active since May of 2022. Read full article.
7. FBI, CISA Issue Joint Warning on ‘Snatch’ Ransomware-as-a-Service – Dark Reading
Snatch ransomware employs a method to force Windows computers to go into safe mode and reboot before encrypting. The Snatch group is targeting CI/KR, including IT and agricultural firms, and the defense industrial base. They also purchase stolen data from other ransomware variants. Snatch has a very active extortion blog and has significantly ramped up activity in the past 12 months. Snatch also takes advantage of RDP, using the credentials from other ransomware campaigns to gain access and then move around the network. Learn more.
Make sure to register for our weekly newsletter to get access to what our analysts are reading on a weekly basis.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















