After RAMP: What Comes Next for the Ransomware Underground?
March 12, 2026
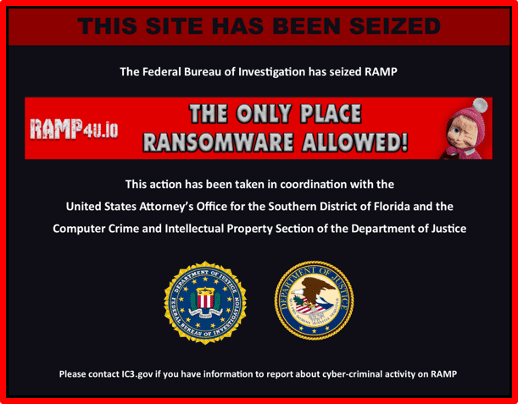
The January 28 law enforcement seizure of RAMP (Russian Anonymous Marketplace) marks another inflection point in the ransomware ecosystem.
According to security researchers, RAMP was created in 2012 but “rose to prominence” in 2021 and was reportedly operated by members of the Babuk ransomware group. RAMP functioned as a Russian-language darknet forum positioned as a curated space for ransomware operators and affiliates.
Research from Yelisey Bohuslavskiy suggested RAMP may have been created by individuals with ties to Russian security services, partly as a countermeasure to the rapid expansion of Ransomware-as-a-Service (RaaS). Prior to 2020, Russian, Belarusian, and Ukrainian security agencies reportedly had substantial visibility into highly organized groups such as Ryuk, Conti, REvil, and Maze. In that context, RAMP may have functioned, in part, as an environment that allowed continued observation of the ransomware landscape as it evolved.
In a LinkedIn post, Bohuslavskiy offered a nuanced assessment of the forum’s seizure:
- Impact on lower-tier actors: RAMP’s closure disproportionately affects smaller operators who relied on the forum for distribution, recruitment, and visibility.
- Distribution disruption: Underground sellers lose a structured marketplace, though platforms like Telegram may absorb some of that displacement.
- Limited impact on top-tier groups: More sophisticated ransomware groups largely avoided RAMP, wary of its associations and potential exposure.
- Reduced visibility for Russian security services: If RAMP did function as a monitoring node, its disappearance may reduce insight into ransomware activity.
Daniel Wilcock, a threat intelligence analyst at Talion, also noted that while the RAMP operator claims to have no plans to create a new forum, actors will likely migrate to alternative darknet forums. As a result, the broader impact on the cybercrime ecosystem may be limited. In the short term, fragmentation is likely. Lower-level actors lose access to established reputation systems and launch channels. Larger entities, however, have historically demonstrated strategic resilience and operational adaptability.
The broader takeaway remains consistent: infrastructure disruptions rarely eliminate ransomware ecosystems; they redistribute them.
From a collection standpoint, this reinforces how quickly reputation and activity shift across forums when a central node disappears. We see similar dynamics in other threat environments. When a TOR-based extremist site is seized or a Telegram channel is banned, communities rarely dissolve; they fragment, migrate, and reconstitute elsewhere. The same adaptive behavior applies to cybercriminal ecosystems.
Lower-tier actors will likely continue interacting across a mix of darknet forums and messaging platforms, including Telegram.
Forums to Monitor Post-RAMP
With RAMP offline, attention is shifting toward other established and emerging hubs:
- Exploit – A longstanding Russian-language forum with structured reputation systems and consistent exploit sales, initial access offerings, and broker activity.
- DarkForums – An English-language platform blending data leaks, credential sales, cracking services, and mid-tier cybercriminal collaboration.
- XSS – Historically one of the most influential Russian cybercrime forums. Despite recurring honeypot rumors, it remains active and operational.
- BreachForums (clones and successors) – High churn, rapid rebranding cycles, and volatile trust environments that often attract opportunistic actors following major disruptions.
- ReHub – A smaller but growing Russian-language forum that has seen increased visibility following recent enforcement actions, frequently hosting access sales and service advertisements.
- LeakBase – Primarily focused on breached data distribution, credential leaks, and database sales, functioning more as a leak-centric marketplace than a full-service criminal forum.
- XForums – A mid-tier forum combining exploit discussions, account sales, and service advertisements, attracting actors displaced from larger platforms.
- HydraForums – Not directly affiliated with the original Hydra marketplace but leveraging brand recognition; hosts cybercrime services, data leaks, and marketplace-style listings.
Rather than a single dominant ransomware forum emerging immediately, we may be entering a prolonged phase of decentralization: parallel ecosystems, shorter trust cycles, and increased cross-platform migration. The BreachForums seizure produced a similar dynamic. These actors do not stop operating – they evolve, reorganize, and migrate. For threat intelligence teams and researchers, this reinforces the need to expand monitoring horizontally and strengthen cross-forum actor correlation.
Stay up to date with the latest in the dark web space. Follow us on LinkedIn.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















