Cyberattacks on Universities
December 9, 2025
Hackers are always looking to gain access to sensitive information to ransom or sell. In recent years, there has been a surge in universities being attacked due to their large databases and typically more vulnerable systems. The most common attacks that compromise universities’ systems are phishing, ransomware, and denial of service (DDoS) attacks. Phishing involves tricking users into revealing login credentials, ransomware locks critical data until a payment is made, and DDoS attacks overwhelm systems to disrupt services.
Why Should Universities Take Precautions?
Universities can face major disruptions if their network is compromised by threat actors. There have been multiple cases where universities have had to shut down their networks to solve the problem, causing huge disruption to their staff and students. If a university deems it necessary to shut down their network, the immediate effects are an annoyed student body, frustrated staff, and long term can cost the school millions. Students expect their university to stay on schedule throughout the year, which is why a network shutdown can reflect poorly on the university.
Ransomware groups especially put pressure on universities because attackers assume they will receive a payment shortly after ransoming data due to a universities’ low tolerance of leaked information being made public and possible long periods of downtime. Furthermore, the school can face lawsuits from students if information is not handled correctly. This is why often when a ransomware group successfully attacks a university, the ransom appears to be paid within a few days.
Universities are required by law to keep any sensitive information like social security numbers, banking accounts, and health records secure. One example of laws that govern universities and how they handle information is FERPA (Family Educational Rights and Privacy Act). Since this is in the context of students who are above the age of 18, this law ensures that schools do not release any information without a student’s consent. This is why when breaches occur, universities tend to face lawsuits for not properly securing their students’ and or alumni’s data. Even when the ransom is paid and not leaked, students, alumni, or faculty can still pursue legal action on the grounds of negligence.
Recent Cyberattacks on Universities
University of Michigan
In August 2023, a major data breach occurred at the University of Michigan. Around 230,000 students, alumni, and employees were affected by the breach. The threat actors stole financial accounts, social security numbers, driver’s license details, and health information.
While the vulnerability that the attackers exploited was never released to the public, the University found the attackers stole the information from the University’s Health Service and School of Dentistry. Once the attack was detected by the University, they immediately shut down their network. The internet shutdown across all three of their campuses ultimately lasted four days during the first week of classes and stopped University operations during that period. The University of Michigan faced two lawsuits after the attack. Both claim that the University was negligent with the security of information. It is unknown if this information was released or who was behind the attack.
Stanford University
Another 2023 cyberattack, coming only a month after The University of Michigan breach was the cyberattack on Stanford University. Unlike Michigan, this attack on Stanford University was claimed by a ransomware group called Akira.
The data Akira gathered was from Stanford’s Department of Public Safety. They claimed to have 430GB of data that would be released unless a ransom was paid. The group later released a link in order for others to download this data. The data they claimed to have was “private information and confidential documents”. Stanford never released the information stolen or if they paid Akira. What we do know is that the FBI has advised companies and universities not to pay ransoms and instead immediately report it to law enforcement.
The below image shows Akira announcing information about the leak on their leak site, as well as the download link which is not shown in the image below.
Ransomware groups will make data available if victims do not pay, this can lead to further attacks against the victims or organizations in their supply chain as information found in this data can be used for further phishing or social engineering attacks.
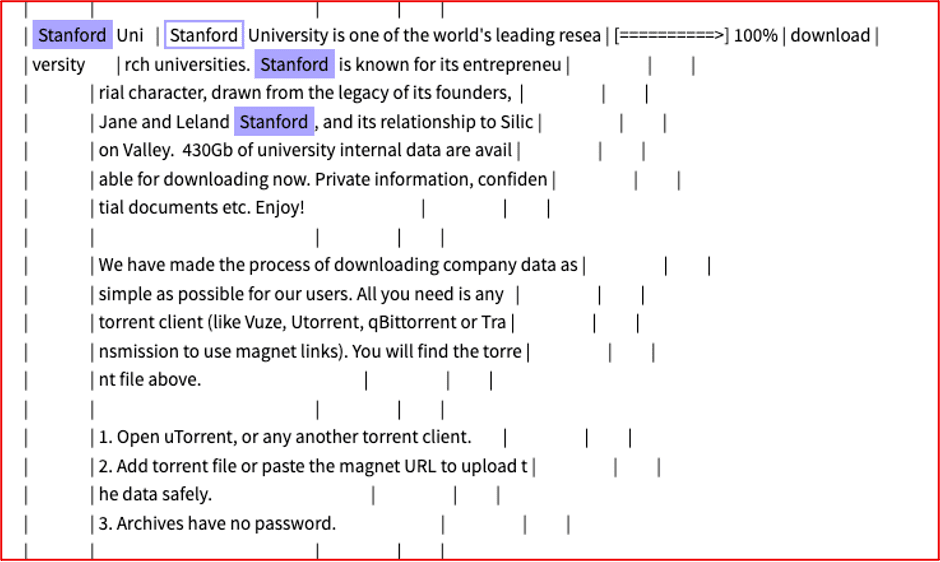
Figure 1: Akira announcing information about the leak on their leak site; Source: DarkOwl Vision
Multi University Attack
The ransomware group Cl0p was responsible for a series of attacks on universities in May of 2023. They were able to exploit the software called MOVEit which is a file transferring tool. MOVEit at the time was known to have a high level of security, especially because many of the files moved within the software contained sensitive information. MOVEit handled file transferring of many other organizations, meaning this attack was not limited to just universities.
Some of the universities that reported the attack included UCLA, Rutgers, and Missouri. These universities reported student and faculty Social Security numbers and financial account information being posted online.
Some analysts believe this attack should not be considered a ransomware attack since the compromised data was never encrypted. However, Cl0p still demanded payments from some universities for the return of data. Recently, some ransomware groups like Cl0p have not been encrypting stolen data and instead pressure people or organizations into paying purely on the threat of releasing the data online.
Have These Attacks Increased?
A company called Netwrix, surveyed 1,309 IT and security professionals globally during 2024, finding that 77% of organizations in the education sector reported an attack on their systems within the past 12 months. This number was up 8% from 2023, which suggests a trend upwards of cyberattacks on schools and universities.
In 2025, the education sector has been the number 1 target for cyber-criminals and ransom groups. Specifically, DeepStrike reported that the two main threats are phishing and ransomware, while explaining that schools and universities typically have high vulnerability in their systems and have large amounts of data, two characteristics that make them top targets.
Protection Against These Attacks
The easiest way for universities to protect against an attack is to have strong authentication requirements. When trying to access the network, the university should require a login via student ID/faculty ID – a second layer to this is multi-factor authentication. This method can also make it easier to track malicious activity by linking activity on the network to an ID.
Another measure that can be overlooked is security software on school computers. These computers are often directly connected to the network, therefore exploiting one can give an attacker access to all of them. The main problem with updating all the software is that it takes a lot of time and most of the time this can’t be done all at once. A good time to update systems would be over Fall, Thanksgiving, Winter, or Spring break when these computers are not being used.
Finally, make sure faculty and students are aware of phishing emails. Humans can be just as vulnerable as a computer – make sure to always keep your passwords secure and do not download suspicious looking files.
To read more about security best practices, check out this blog.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















