What is Ransomware as a Service?
March 19, 2026
Cybersecurity might as well have its own language. There are so many acronyms, terms, sayings that cybersecurity professionals and threat actors both use that unless you are deeply knowledgeable, have experience in the security field or have a keen interest, one may not know. Understanding what these acronyms and terms mean is the first step to developing a thorough understanding of cybersecurity and in turn better protecting yourself, clients, and employees.
In this blog series, we aim to explain and simplify some of the most commonly used terms. Previously, we have covered bullet proof hosting, CVEs, APIs, brute force attacks, zero-day exploits, doxing, data harvesting, IoCs, and credential stuffing. In this edition, we dive into Ransomware as a Service.
Ransomware as a Service 101
Ransomware has become one of the most disruptive cyber threats affecting organizations worldwide. What was once a technically complex attack carried out by a small number of sophisticated hackers has evolved into a scalable criminal ecosystem. Today, ransomware can be purchased, deployed, and monetized through a model known as Ransomware-as-a-Service (RaaS). It is a business model for cybercriminals to hire ransomware operators to launch ransomware attacks on their behalf.
DarkOwl research and analysis shows how ransomware groups operate like structured businesses on darknet forums and marketplaces—recruiting affiliates, sharing tools, and dividing profits. Understanding how this ecosystem works is critical for organizations seeking to defend against it.
RaaS is a business model in which ransomware developers create malware and infrastructure, then lease it to affiliates who carry out attacks. In turn, the developers get a percentage of the ransom earnings from the affiliates. Typically, the affiliate keeps 70-80%, while the developer takes a 20-30% “licensing fee.” This model lowers the barrier to entry and this model of cybercrime is now the driving force behind the global surge in extortion attacks. Individuals with limited technical skills can participate in ransomware campaigns simply by purchasing access to a RaaS toolkit.
Ransomware groups often operate similarly to legitimate businesses, complete with recruitment processes, internal management tools, and operational dashboards used to track victims and ransom payments. DarkOwl analysts often find “starter kits” for sale on darknet forums. These kits include everything a criminal needs: the malware, a user manual on how to infect a target, and even 24/7 technical support from the developers. It is a professionalized industry where reputation and “customer service” matter to the criminals.
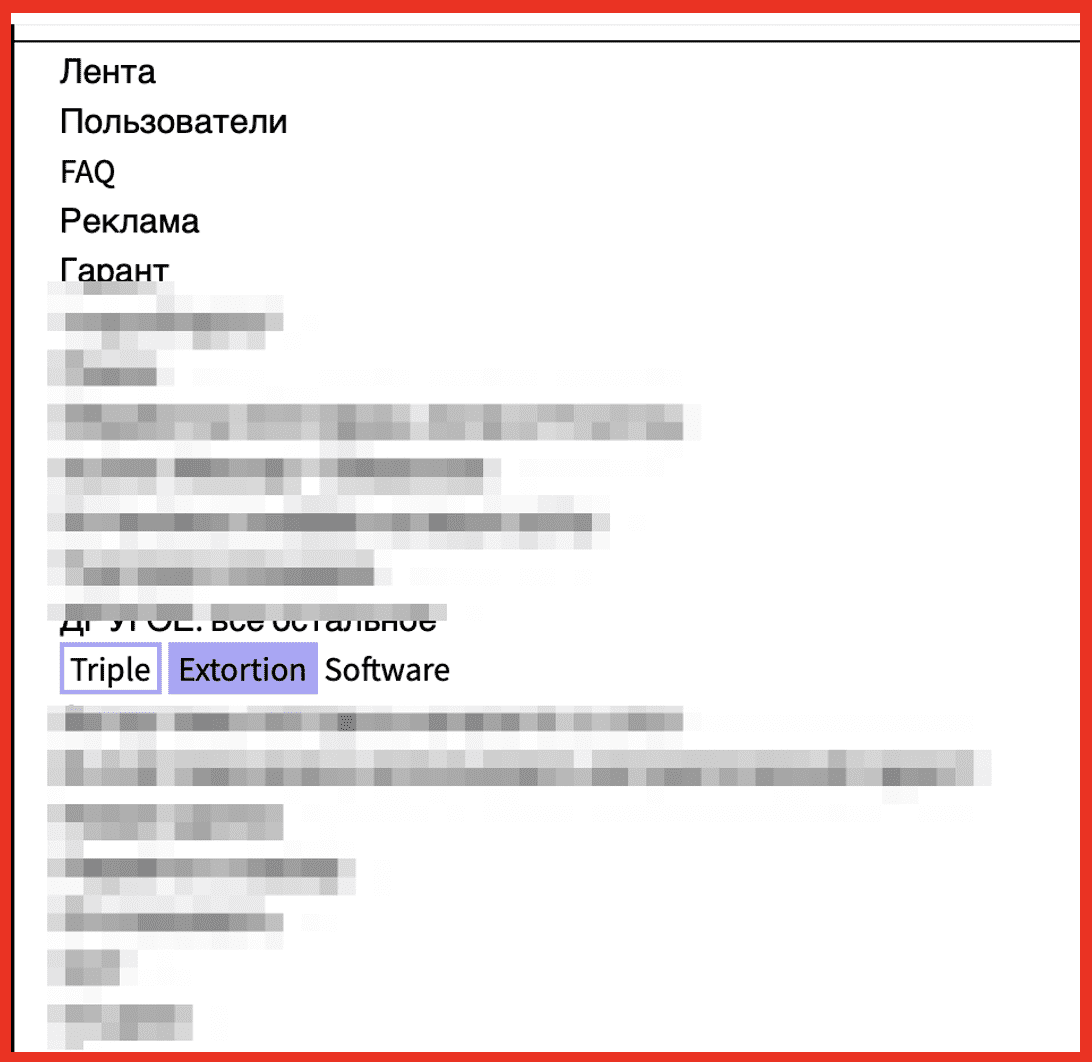
Figure 1: Post on criminal market XSS offers triple extortion software for purchase; Source: DarkOwl Vision
Ransomware as a Service in the Wild
RansomHub
The group RansomHub first appeared in February 2024, with an announcement on the Russian forum RAMP. The group operates a ransomware-as-a-service (RaaS) model, targeting multiple platforms, including Windows, Linux, and ESXi. A user named “koley” made the announcement and invited others to join their affiliate program. RansomHub quickly became one of the most active ransomware groups, claiming 593 victims by the end of the year. RansomHub’s affiliate program has been prolific over taking established groups, such as LockBit, in the number of victims they have. Notably, RansomHub was responsible for a significant breach of the U.S. healthcare payment system in 2024.
Hive
First observed in 2021, Hive operated as a RaaS platform with affiliates targeting organizations worldwide. The group notably targeted healthcare organizations and used double-extortion tactics—encrypting systems while also threatening to release stolen data. In 2023, an international law-enforcement operation seized Hive’s infrastructure after the group had already impacted more than 1,500 organizations globally.
Conti
Conti was one of the most prolific ransomware operations in the world. Internal chat logs leaked in 2022 revealed a highly organized operation that included employee-like roles, development pipelines, and operational dashboards used to track victims and payments. Although the group officially shut down, many of its members dispersed into other ransomware operations, continuing the ecosystem under new names.
BlackCat
Also known as ALPHV, BlackCat emerged in 2021 and quickly gained attention for being written in the Rust programming language. The group implemented a public data-leak site that indexed stolen files, increasing pressure on victims to pay ransom demands.
Protection and Mitigation
Ransomware is an efficient criminal operation yielding high profit for minimal work. Due to pseudo-anonymous technology, using the dark web for ransomware operations and cryptocurrency for payments, as well as email and VPN services that do not track physical location, ransomware groups will continue their activities because the risk of punishment is minimal, and the operations are profitable.
As always, DarkOwl recommends practicing cyber hygiene at work and home.
- The 3-2-1 Backup Rule: Keep three copies of your data, on two different media types, with one copy stored completely offline. By using multiple storage types and locations, it helps you avoid having a single point of failure.
- Enable Multi-Factor Authentication (MFA): Turn on MFA for every account. It adds a second proof (app prompt, code, or security key) so a stolen password alone won’t grant access.
- Patches and Updates: Keep everything current—laptops, phones, browsers, and even routers/IoT. Updates patch known flaws attackers actively exploit. Criminals look for “holes” in outdated software.
- Phishing Awareness & Training: Most RaaS attacks start with a simple phishing email. Slow down on links and attachments. Verify unusual requests on a separate channel and report suspicious emails/messages to IT.
Product Highlight: Ransomware API
Ransomware is not only a problem for those directly affected. Awareness of events among your own or your customers’ supplier ecosystems can help you stay aware of potential vectoring threats. The DarkOwl Ransomware API is designed to answer the essential question: Has an organization I monitor been extorted or compromised in a cybersecurity incident?
Leveraging the world’s leading and continuously updated darknet data index, you can gain insight into potential risk by conducting targeted ransomware searches. Ransomware API enables users to safely query continuously sourced and updated ransomware sites, primarily but not exclusively hosted in TOR and Telegram, run by criminal gangs, and threat actors to detect mentions of criminal activity against an organization.
Search parameters enable queries by company website, company name, contact name, or other proximity indicators such as products, brands, or other intellectual property. Automated monitoring and alerting ensure continuous vigilance to a dynamic list of sources continually updated by DarkOwl.
Curious to learn more about Ransomware API? Contact us.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















