[Speaking Session Transcription] What is the Darknet and how is it used in Cybercriminal Investigations?
July 12, 2023
Or, watch on YouTube
Have you ever heard of The Onion Router (TOR) ? Have you ever ventured onto the dark web, maybe a forum or a marketplace? Or have you heard of Open-Source Intelligence (OSINT)? Or have you ever been curious to learn more about what it is like to work in cybersecurity?
The American University of Cairo welcomed Richard Hancock from DarkOwl, an experienced cybercrime investigator, on the history and evolution of the darknet, how it is typically accessed, and how the darknet can be used in threat intelligence and cybercrime investigations.
NOTE: Some content has been edited for length and clarity.
Dr. Sherif Aly: Gives me a pleasure to introduce Richard Hancock today, who works for DarkOwl. Richard has a quite a bit of extensive experience in digital forensics and mining the dark web, if I can say. And it’s a good opportunity to hand it over to you to better introduce yourself and what you do.
Richard Hancock: Absolutely. Thanks a lot, Sherif. Thanks for having me and appreciate you guys taking time out of your day to listen to me speak about the darknet and all the cool things I see on there. So, I work for a company called DarkOwl. What we do is we have a user interface, a searchable user interface, that we give to clients that want to search on the darknet in a safe way.
Going into a little bit about my background before we go into what the darknet is and how to use it for cybercriminal investigations. So a little bit about my background. I have over 7 years experience as an open source intelligence investigator. I spent 4 years living in Amman, Jordan and Abu Dhabi as well. So some of the topics that I’ve focused on would be Arabic linguistics, counterterrorism darknet intelligence, social engineering, and cybercrime.
One of the things I focus on right now, my current job title is Darknet Intelligence Analyst and Sales Engineering Team Lead. It’s a really long title, but kind of my everyday. What my everyday looks like is, I start out my day getting onto various darknet forums in marketplaces and I direct our collections team to collect from the most high value content – usually digital fraud goods, counterfeit items that are things that would be of interest to our clients. So spending a lot of time in the darknet, and then also getting on calls and speaking to people to try to get them to pay for our platform. And I also wanted to share some of my other hobbies outside of this work because it is pretty serious work; you have to make sure that you have fun outside of work. After I lived in the Middle East for several years I returned back to Colorado, where I went to college, and I’m really big into backcountry skiing as well as DJing underground parties and house music.

What is the Darknet?
The surface net is what you guys would be most most familiar with; this would be any websites that are indexed by search engines like Google, Bing, etc. The deepnet – that’s just a layer further, it’s still the same sites that you’re accessing through those same search engines. However, you need some sort of credentials, username and password to get on to these sites. It could be Netflix. It could be social media. It could also be some criminal hacking forums that are accessible through the surface net.
The part of the Internet that we really focus on is here in the darknet. So in order to get on the darknet, it’s still technically the same Internet. But you need special software in order to access this hidden layer of the Internet, which is used for anonymous communication, selling drugs, or selling counterfeit items. This is the part of the Internet that we really focus on at DarkOwl.
You primarily access the darknet, using all of these software right here. The one that is most popular would be Tor, also known as the onion router. i2p is also popular and same as Zeronet.
The deep net, as I’ve mentioned, is still the same Internet but it’s accessible through search engines like Google and Bing and it can represent social media websites, Netflix, as well as some underground criminal forums that are not darknet specific. That would be like noel.to which is a hacking forum.
However, something that’s really increasing the last several years would be the rise of direct messaging platforms. So criminals are obviously going to be living on the darknet. They’ll be living on the deep web.
But how are they communicating with each other? Are they just using these marketplaces and forums to talk to each other? Not necessarily. An app that we’re seeing is really on the rise right now is Telegram. And that’s primarily because it’s really really easy to use. The cybercriminal ecosystem on Telegram is absolutely massive these days. Whether it’s right wing extremism, Islamic extremism activities, Russia Ukraine and the invasion, misinformation, and people selling Netflix accounts, etc.
History of the Darknet
Let’s talk a little bit about the history of the darknet. When was it created? The Tor browser was created by the Naval Intelligence Unit in the CIA in the United States, back in 2002. It was originally used as a way for agents to communicate with each other in the field, so primarily in places like Iran or Russia. It was just for military intelligence and communication. Since then it has evolved a little bit. It then evolved for agents to use the Tor browser to communicate with their family members, and then the next step was the Tor board of directors allowing public use of the Tor browser for free speech, for activism, for journalism, and then obviously cybercriminal ecosystems quickly grew on here.
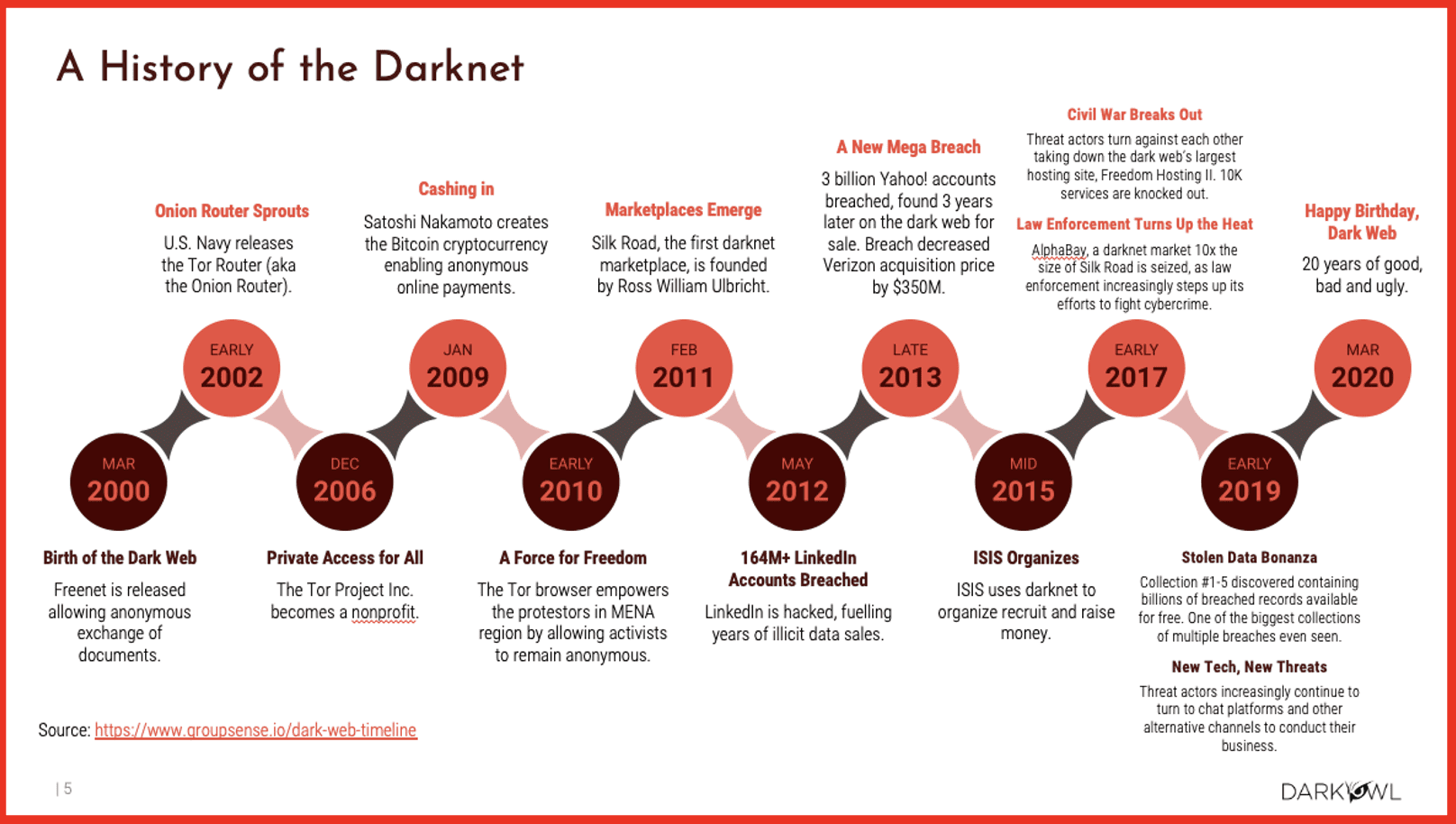
So, going into this a little bit further, Bitcoin was created in 2009, and that’s what really facilitated the emergence of the marketplaces and forums, because it allowed people to buy things and make transactions. And in an anonymous way.
The first really big marketplace was the Silk Road. If you guys are familiar with this, you might know the guy, the founder, Ross Ulbricht. There’s a lot of good movies on Netflix, or documentaries that you could probably find on YouTube about this instance. If you’ve not heard of Ross Ulbricht and Silk Road, highly encourage you to check out that story. It’s quite fascinating. He ended up getting arrested by law enforcement in 2016, which marked the shutdown of the Silk Road. And I actually know some of the people who were involved in that investigation, in the arrest of that individual. As the darknet has continued, we’ve seen an increase of law enforcement presence in the rise of something called honeypots. So that’s when Russ Ulbricht, the Silk Road founder was arrested. At that point, that is when we really saw an increasing presence of law enforcement on darknet marketplaces, forums, etc. It really started with a lot of American-centric law enforcement presence but quickly expanded to other countries. And I will tell you from personal experience, one of the most savvy NATO countries in terms of darknet investigations would definitely be the German Government. The German Government is very skilled with darknet cybercrime.
2020 marked the twentieth year that the darknet has been around. The future of the darknet is really going to be interesting, because we will always see things like Tor. People will probably stick around. But as I mentioned, we’re really seeing an increasing use of chat applications which are not part of the darknet. But let’s say you’re a ransomware actor – you’re definitely going to be using Telegram just like you would those forums and marketplaces, or in the [.] onion sites where you start, where you actually are hosting corporate leaks, databases, and things like that.
Content in the Darknet
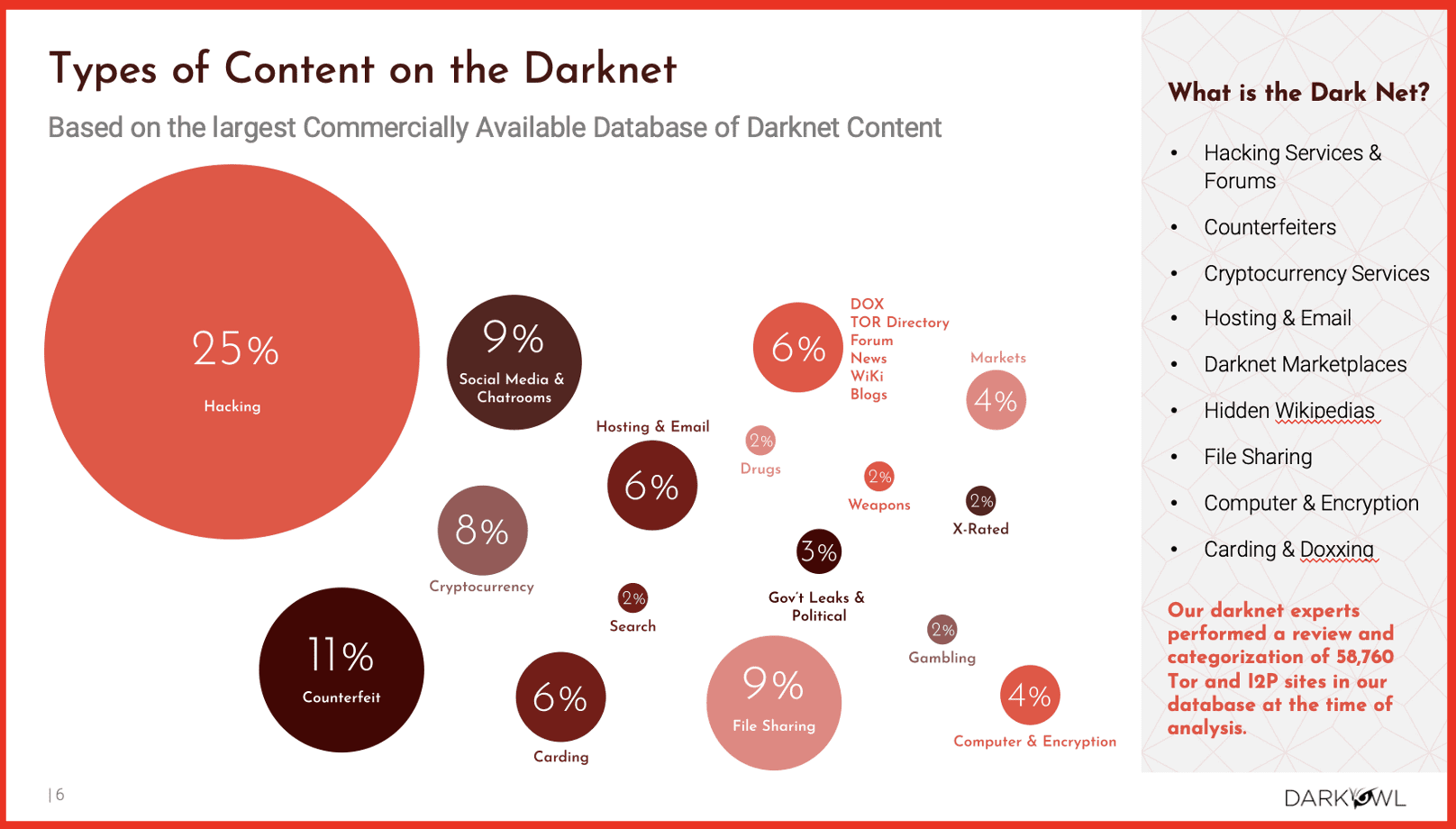
There’s a lot of different things on the darknet. Some things that are really popular in the media about the darknet would be drugs or assassins for hire, and while those things definitely exist on there, it’s not very actionable, especially for the kind of clients that we help in the kind of investigations that I am doing. The primary content that we’re seeing is hacking related. So whether that’s somebody that’s developed an exploit for a specific tool, somebody’s leaked source code for a particular company, or maybe somebody’s sharing leaked databases that contain usernames and passwords associated with like admin credentials for a company.
You know, there’s a lot of different things you can see on there: counterfeit items, passports, pilot certificates, cryptocurrency, fraud, credit card fraud is super widespread. And then, as well, as you know, drugs, weapons, there is quite a bit of child exploitation, child pornography material on the darknet as well. Unfortunately.
So pointing out some more additional examples and some of the things that we we are able to collect when we’re crawling from the darknet:
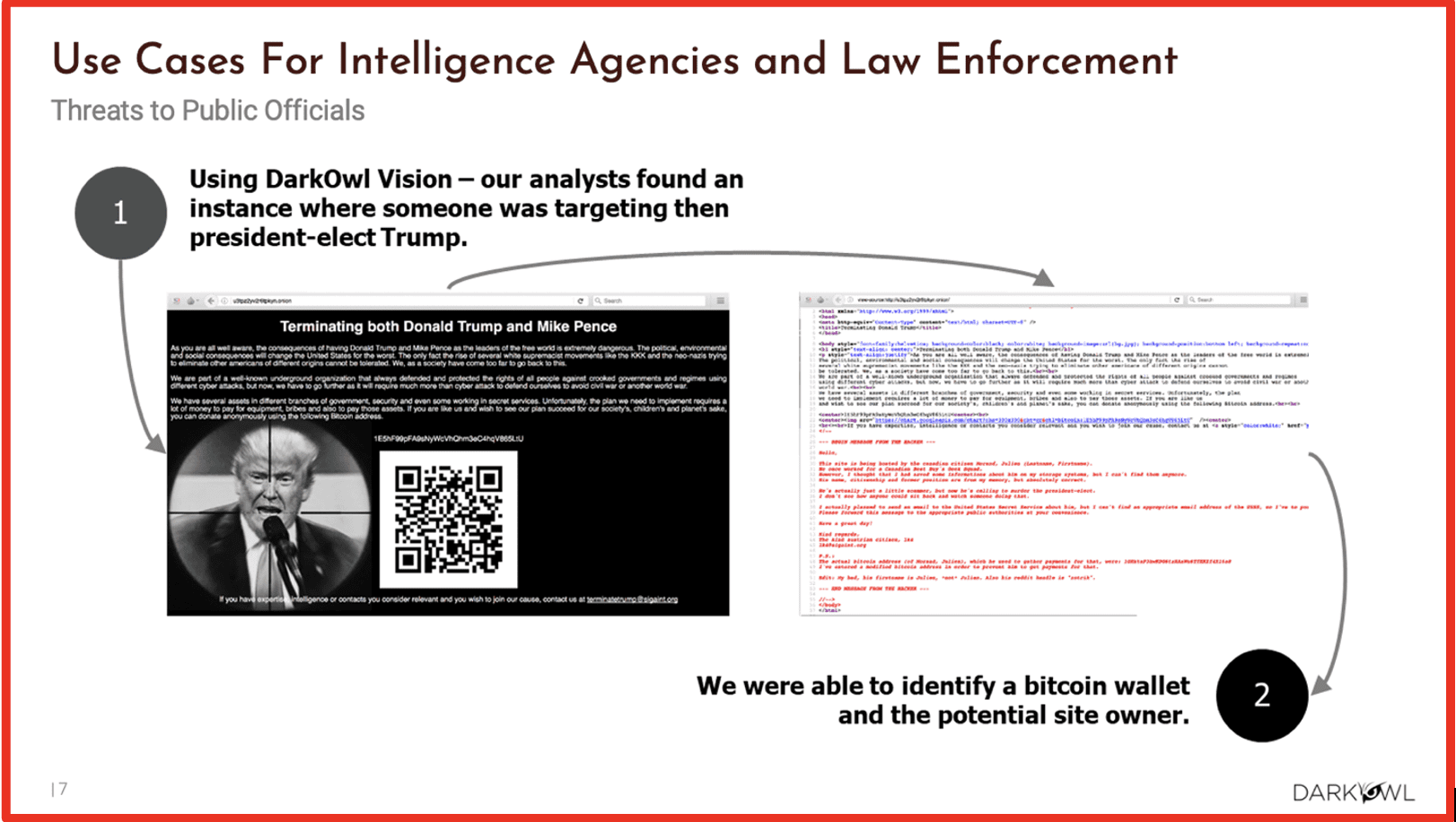
So when we’re crawling information from the darknet, we’re not scraping pictures like this [see image above]. We’re just scraping the raw text. In this specific example, we’re seeing somebody who’s hosted this information on a [.] onion site. I’m not sure how serious this threat was, but they were claiming to be targeting Donald Trump and Mike Pence for an assassination, and they actually included a QR code with a Bitcoin wallet address, and we were able to track that wallet. This is the kind of information that investigators use within our platform and our data to pull on strings and investigate individuals further, because if you’re able to identify a Bitcoin wallet with an individual on the darknet you can search upon that Bitcoin wallet and see where else they might be using it, maybe on Telegram, a marketplace or a forum. As I mentioned, there’s a lot of counterfeit documents being sold on the darknet. During Covid we saw a lot of Covid scams, tons of counterfeit, fake covid documents, vaccinations cards, as well as we see passports, drivers licenses, certificates and other things as well.

I did mention that there is extremism presence in the darknet. When ISIS was starting in 2014, they actually did have quite a big presence on an onion site. However, today we’re not seeing a very big presence of Islamic terrorists, Islamic extremist groups on the darknet itself. However, we do see quite a bit on Telegram. So this specific shot is from a group known as Jerusalem Electronic Army, which is loosely affiliated with the some Hamas cybergroups. And this is issuing out a target for a water sanitation facility in Israel. And these kinds of attacks, cyberactors targeting industrial control systems for critical infrastructure, is definitely something that’s on the rise. We’ve seen that in Russia, Ukraine. We’ve seen it within the United States, and I can tell you from a Federal government level within the United States, we’re putting a lot a lot of money and effort into building coalitions between agencies to monitor these types of things. Sometimes here at DarkOwl, we actually get agents who ask us specific questions about threats to critical infrastructure. So it’s something that’s on the minds of a lot of people these days. As I also mentioned, drugs are really big on the darknet, going back all the way to the beginning of the Silk Road. That’s what it was primarily used for. I would say, again, it’s probably not the most popular part of the darknet these days. Like I said, it’s going to be that hacking information – basically selling data on individuals and corporations.
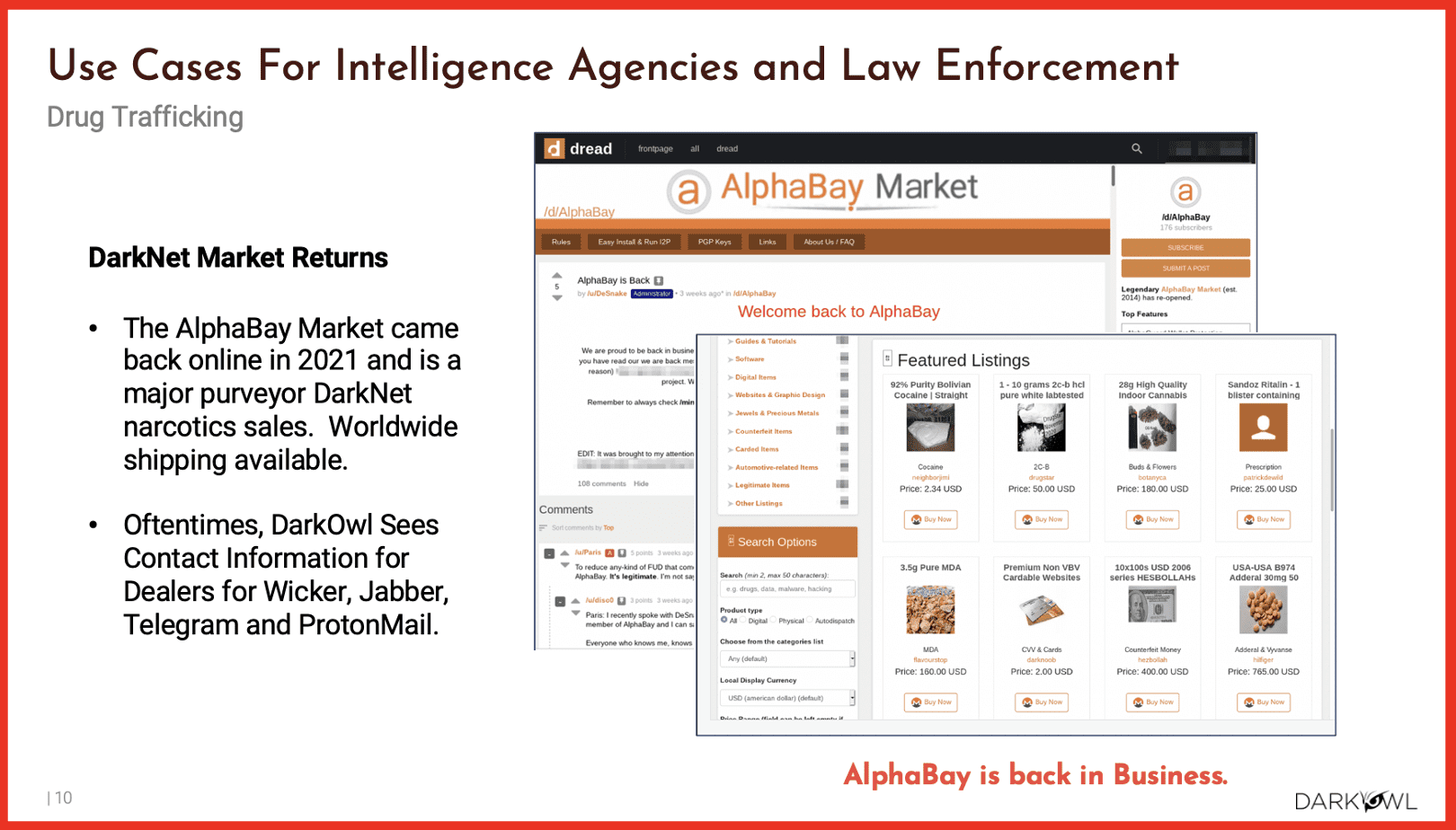
This specific screenshot is showing AlphaBay Market, which is a really popular market that had temporarily gone offline after a law enforcement seizure, and then did come back online in 2021. This is something that we’ve seen quite a bit in the last 2 years. I know recently 2 marketplaces that have been shut down: Genesis as well as Monopoly market.
Something that a lot of people in my industry are very skeptical of is when a marketplace is offline by law enforcement seizure, whether it’s Interpol or the United Nations, Drug Enforcement, or whatever it is, if that marketplace or forum returns, at a certain point we pretty much consider that to be co-opted by law enforcement. So probably the admin of that site has been arrested, and maybe they’re using that admin for their skills and things like that. But they’re continuing the existence of that market or forum for the primary purpose of collecting information on individuals and surveillance.
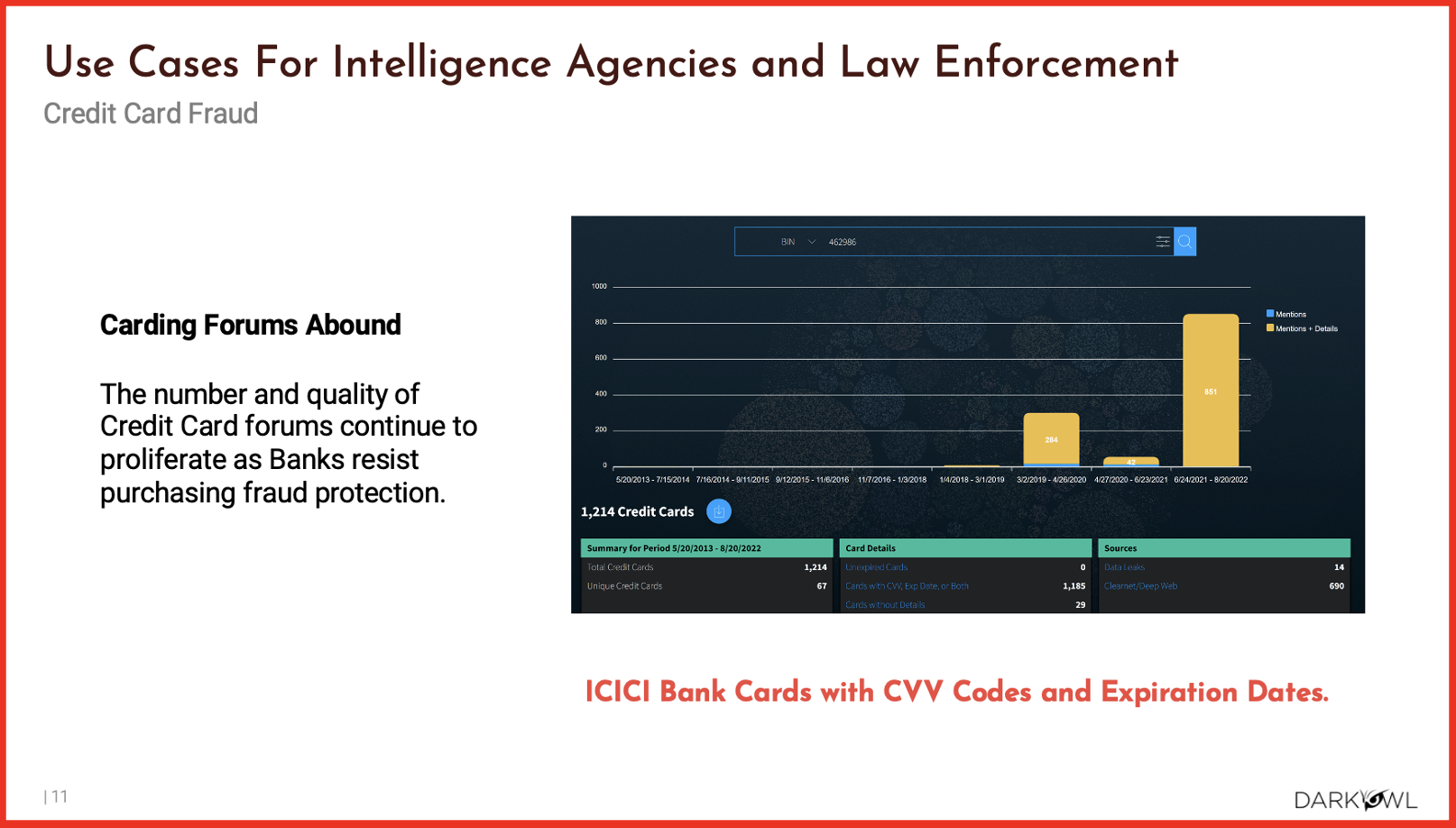
I also mentioned credit card fraud, which is really widespread on the darknet. There’s just huge databases out there that people can easily pay for, that include, credit card numbers, bin numbers, as well as the personal identity, the PII, associated with the individuals bank account information. So that’s really widespread in the darknet as well as people who are selling methodologies to target specific banks. Maybe it’s check fraud, wire fraud, all different types of fraud. It’s really widespread not just to sell access to somebody’s credit card information, but actually to sell access to information, how to commit fraud against a bank or a credit card company.
Right here is an example of telecommunications fraud.
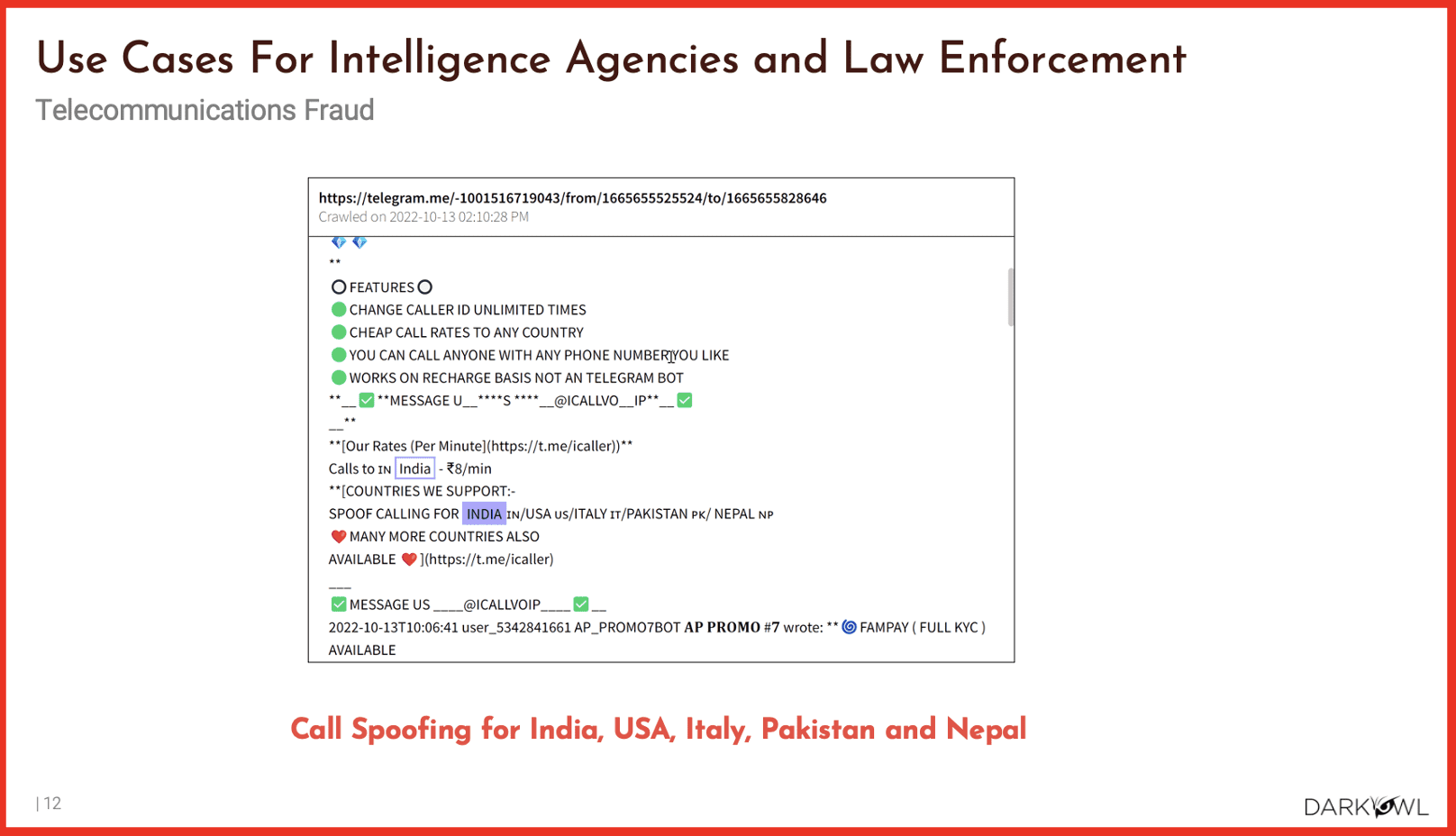
This specific example looks like spoof calling in India. This is absolutely widespread. Any company that has a large mobile application user base, eo whether that’s Coinbase, Netflix and those kind of companies are going to be targeted for fraud the most on the darknet. It’s actually, it’s pretty funny. And a lot of the investigations that we’re going through, from a government level, people are always asking about sophisticated nation state actors. But I’ll tell you, the people that I interact with the most on the darknet are really eager, like 15 to 17 year olds that are trying to become hackers. And for a long time people weren’t taking these individuals serious because they’re like, how serious can you take a teenager? Well, I can tell you that most of the fraud of those companies I just mentioned, UberEats and Netflix, etc – that type of fraud is usually perpetrated by teenagers, and it’s quite often these days when their parents aren’t home, a 15 year old, hanging out with their buddies Friday night, rather than you know, maybe 10 years ago, trying to take money from their parents purse, they’ll actually try to steal somebody’s Pizza Hut account on Telegram and get free pizza for the night. So kind of funny, the world that we’re living in today.
So different types of cryptocurrency used on the darknet.
If you want to purchase something in the darknet, be it a legal or illegal item, cryptocurrency is how you purchase that item anonymously. These 6 cryptocurrencies that are most used are: Bitcoin, Monero, ethereum, Zcash, Dash, and litecoin. There are others, for sure, and you will actually see on one of the emerging dark parts of the darknet called Loki – they’ve actually created their own cryptocurrency within their network, which is pretty sweet. Cryptocurrency is the primary vehicle for illegal transactions on the darknet, and as I mentioned, monitoring cryptocurrency and wallet address activity is a really good way to monitor cybercriminal activity. And when we’re dealing with law enforcement, this is one of the primary vectors in the primary information that they’re searching within our platform.
How do we get to the Darknet?
I had mentioned Tor, the onion router. This is this the primary way people get to the darknet and as I mentioned, it was created all the way back in 2002 – I’m sure it looked a little bit different. When you do get on the darknet, you can enter addresses above in the search bar, or you can search for DuckGo. But the thing that you guys need to understand about the darknet is this is a community and you can only find information if you become an active member of the community. So what I’m trying to say is, if you want to search in that search bar, show me the top 10 criminal marketplaces – you’re just not going to get anywhere. If you’re a new threat actor, you’ll start on one site and that’s called Dread. Dread is the reddit equivalent of the darknet. It’s a great place for young hackers to start their journey and to find links to different marketplaces and forums and basically to interact with users who might be vendors selling illegal items on those forums.
Dread is kind of the the starting point if you will. But you need to know what the URL is for, that there might be a way you can use some open source, Google dorking technique on Google to find some links for that. But it’s really a need to know. And yeah, as as you find more and more links, you get deeper and deeper into these communities.
There are other ways to get to the darknet. It is really popular, this actually re-surged in popularity, since the Russian invasion of Ukraine. So there’s a huge, heavy Russian language, cyberactor presence on this site. It’s a lot more difficult to set up than Tor. If you want to set up the Tor browser, you really just need to have pretty basic understanding of setting up virtual machines, manually configuring proxies and downloading the Tor browser, and using burner numbers and things like that. But I2P is a bit more technical in terms of setting up the server. And it’s something that I’m actually trying to learn more this year, because it’s a it’s a part of the darknet that’s been growing recently, especially with the Russian cyber threat actor community.
There are other ways to get there. There’s a lot of different ways to access the darknet. The one I primarily use is gonna always be Tor but also ZeroNet and FreeNet. What you need to know is the darknets evolving and changing constantly. I keep mentioning Loki, and that’s because it’s quite interesting, because they have their own cryptocurrency known as on oxen.
How is Darknet Data used in Cyber Investigations?
So darknet intelligence is just a one component of open source intelligence. Open source intelligence – there’s social media intelligence, there’s private intelligence. There’s a lot of different kinds of intelligence data feeds that investigators use to conduct investigations. Darknet data is really useful to add into the full spectrum of sources that you’re using. So you can make informed decisions to strategic decisions, right? So if somebody’s looking at somebody’s username on a clearnet, maybe on a social media website, maybe they’re using a similar username on a darknet forum or some other tools.
If you guys are interested in open source search techniques, Michael Basil’s book right here. This guy is awesome. He is really, really, really, knowledgeable and he’s got the most extensive book for all the different types of open source intelligence, searching techniques. If you guys are interested in this stuff, highly encourage you to check him out.
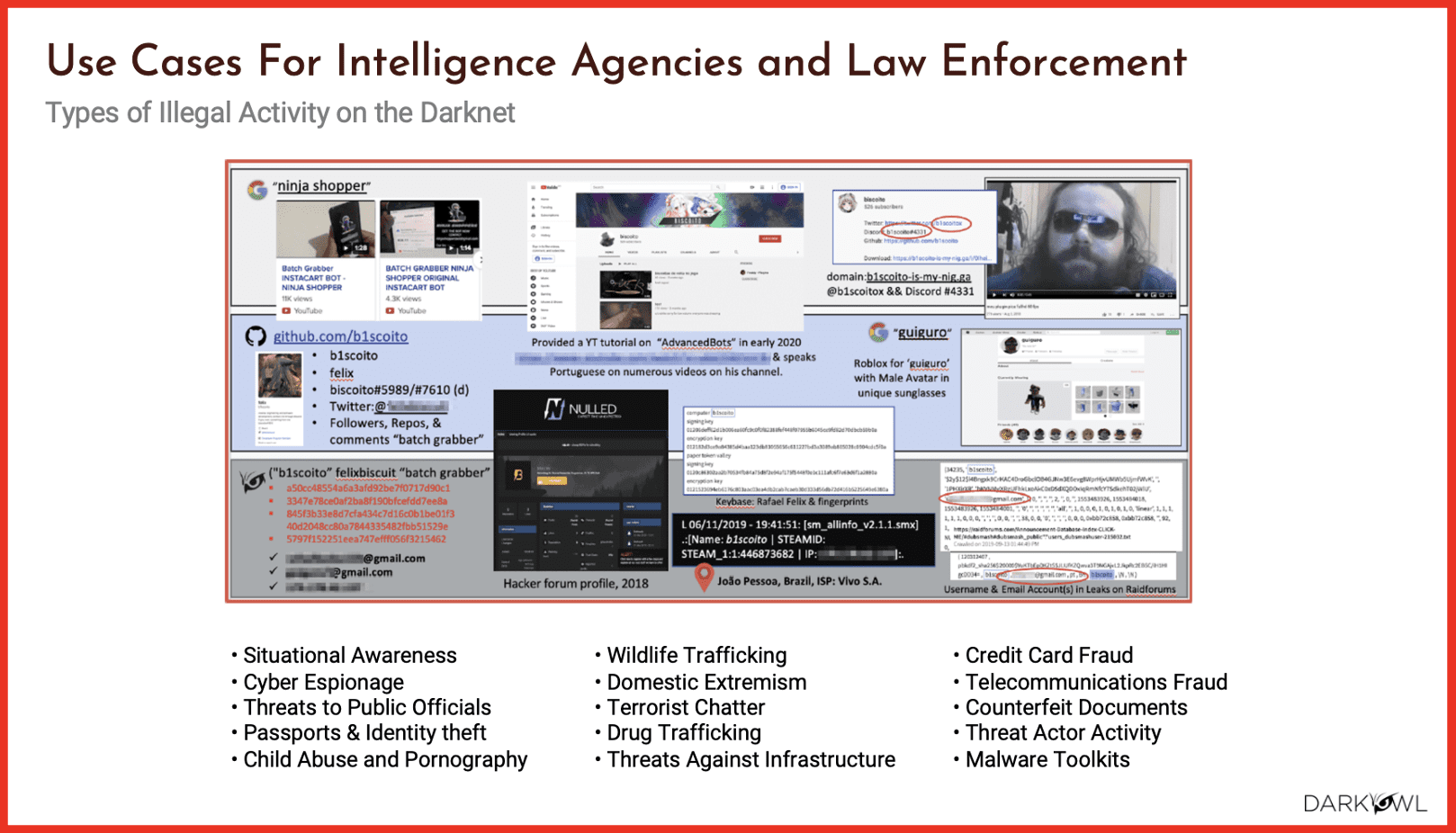
And here’s a quick example of basically what I was explaining; searching a username on Google and then eventually leading out to darknet forums. So in this specific example, we found somebody had asked us about an individual who goes by the name of Ninja Shopper. So we first search that on Google and find a YouTube page. And then we were able to find actually a Discord server where this individual has a presence as well as another alias. We found this guy and his sunglasses over here, and his long beard – looks like a pretty typical sitting behind the computer threat actor. We were then able to find a Github account, which gave us more information, which eventually led us to this male avatar for unique sunglasses, and then searching for this username, these 3 usernames, I should say we were able to find this individual’s presence on darknet forums like RaidForums. Some personal information was leaked on RaidForums. So this is just showing you that these are the kinds of investigations that we’re doing all day. Some of the other illegal activity you’ll see out there is cyber espionage, threats to public officials, child abusive materials, wildlife trafficking, domestic extremism, drug trafficking, threat against critical infrastructure, credit card fraud, telecommunications fraud, counterfeit documents, malware, and a lot more.
Interested in learning how DarkOwl can help with your darknet investigations? Contact us.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















