Cyber Security Awareness Month: Upcoming Content
October 01, 2025
In light of Cybersecurity Awareness month, DarkOwl is committed to sharing research, trends and industry news from our analysts.
Be the first to know as we release new research by entering your email below!
Upcoming Content This Month
BLOG
Threat Intel Round Up: September
Our analyst team shares a few articles each week in our email newsletter which goes every Thursday. Make sure to register! This blog highlights those articles in order of what was the most popular in our newsletter – what our readers found the most intriguing. Stay tuned for a recap every month. We hope sharing these resources and news articles emphasizes the importance of cybersecurity and sheds light on the latest in threat intelligence. Check it out.
EVENT
it-sa Expo & Congress
We will be at it-sa 365, Europe’s largest trade fair for IT security and one of the most important dialogue platforms for IT security solutions. The trade fair covers the entire range of products and services in the field of cybersecurity: hardware, software, training and consulting services as well as Security as a Service. Stop by and meet with us at Booth 9 – 349. Meet us!
WEBINAR
New Regulations & What They Mean for Your Supply Chain
This fireside chat explores challenges and opportunities of incoming regulations impacting cybersecurity in the UK and EU.
Greater digitalization brings with it an avalanche of Third Party integrations and supplier exposure. Rich Hanstock (pwn.legal) and Lindsay Whyte (DarkOwl) explore what new regulations mean for cybersecurity teams, and the change in attitudes required to reassure regulators and customers alike.
Discover how DarkOwl’s DarkSonar helps organizations build a resilient, responsive supply chain security strategy that aligns with Europe’s regulatory future. Transcription and recording here.
BLOG
What is a DDoS Attack?
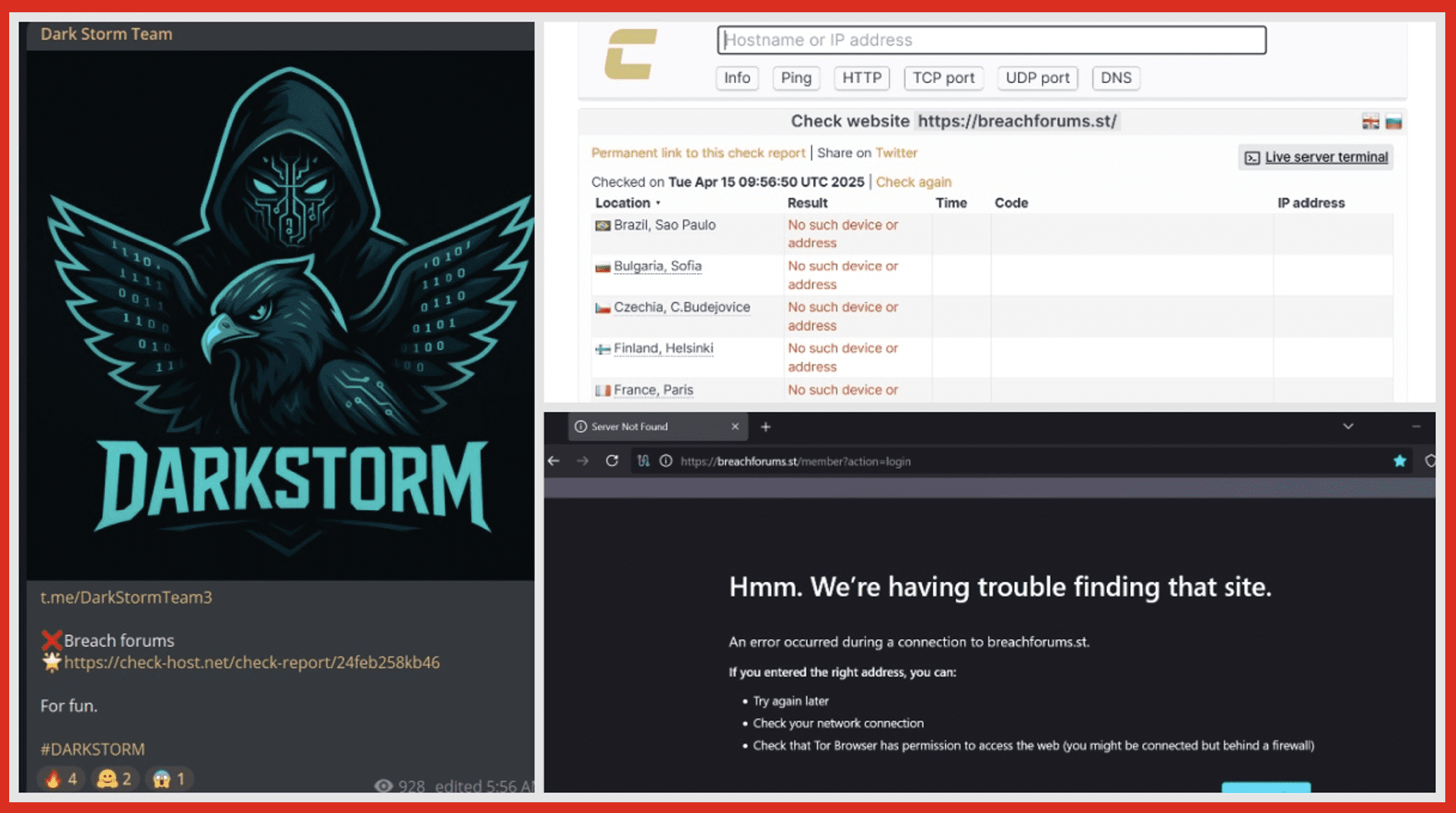
Cybersecurity might as well have its own language. There are so many acronyms, terms, sayings that cybersecurity professionals and threat actors both use that unless you are deeply knowledgeable, have experience in the security field or have a keen interest, one may not know. Understanding what these acronyms and terms mean is the first step to developing a thorough understanding of cybersecurity and in turn better protecting yourself, clients, and employees.
In this blog series, we aim to explain and simplify some of the most commonly used terms. Previously, we have covered bullet proof hosting, CVEs, APIs, brute force attacks, zero-day exploits, doxing, data harvesting, IoCs, and credential stuffing. In this edition, we dive into DDoS attacks. Read it here!
WEBINAR
AI vs AI: How Threat Actors and Investigators are Racing for Advantage
AI is transforming investigations, but also transforming adversarial tradecraft. How do we keep pace? From Telegram channels to dark web marketplaces, threat actors are using AI to accelerate crime, propaganda and deception. OSINT Combine and DarkOwl break down what’s happening behind the scenes and how investigators can keep up. Topics of discussion:
- Exploration of how cybercriminals and terrorist groups are experimenting with AI technologies
- Emerging dark web trends
- Overview of AI-augmented investigation techniques
- How investigators use AI for data collection
- Detecting Disinformation and Synthetic Content
- Live collaborative analysis by DarkOwl and OSINT Combine
Register here. Transcription to follow.
BLOG
Q3 Product Updates
Stay tuned for our quarterly update blog highlighting new product features and collection stats updates. There is always something exciting coming from our Product and Collections teams and the team is excited to share this round of updates!
BLOG
Cyber Hygiene at Work & Home
In this blog, we will highlight best practices for a safer digital life.
BLOG
Command-and-Control Frameworks – Post Exploitation in Plain Sight
The blog “Indicator of Attack 101” introduces the concept of Indicators of Attack (IoAs), explaining how they differ from Indicators of Compromise (IoCs) and why IoAs are crucial for proactive cyber defense.
BLOG
How Cybercriminals Build Trust in Darknet Marketplaces
Command-and-control (C2) frameworks are used by both red teams and cybercriminals. They provide a wide range of functionality and capabilities that make post-exploitation tactics easier and more effective. In simple terms, a C2 acts as a central server that connects to, communicates with, and manages compromised systems. It establishes persistence and allows the operator to control dozens of infected machines from one central environment.
BLOG
Halloween: Spooky Finds on the Dark Web

The darknet can be a scary place. 👻 For Halloween, we will highlight some spooky findings from our analyst team that they have come across this past year. In the meantime, check out our previous edition where the team uncovered human organs for sale, human meat for sale, and hitmen for hire! Check out last years’ blog here.
Curious to see how darknet data can improve your cybersecurity situational awareness? Contact us.
Explore the Products
See why DarkOwl is the Leader in Darknet Data
Products
Services
Use Cases















