Difference Between Information Security and Cybersecurity
February 19, 2026
In an era of data breaches and constant headlines focused on “security” topics, “security” has become a catch-all term. While the terms cyber security and information security are often used interchangeably, it is important to acknowledge that they focus on different areas – they are related, but their scope differs. In this blog, we will explore how they differ in scope, focus, and application.
Information Security Vs Cybersecurity
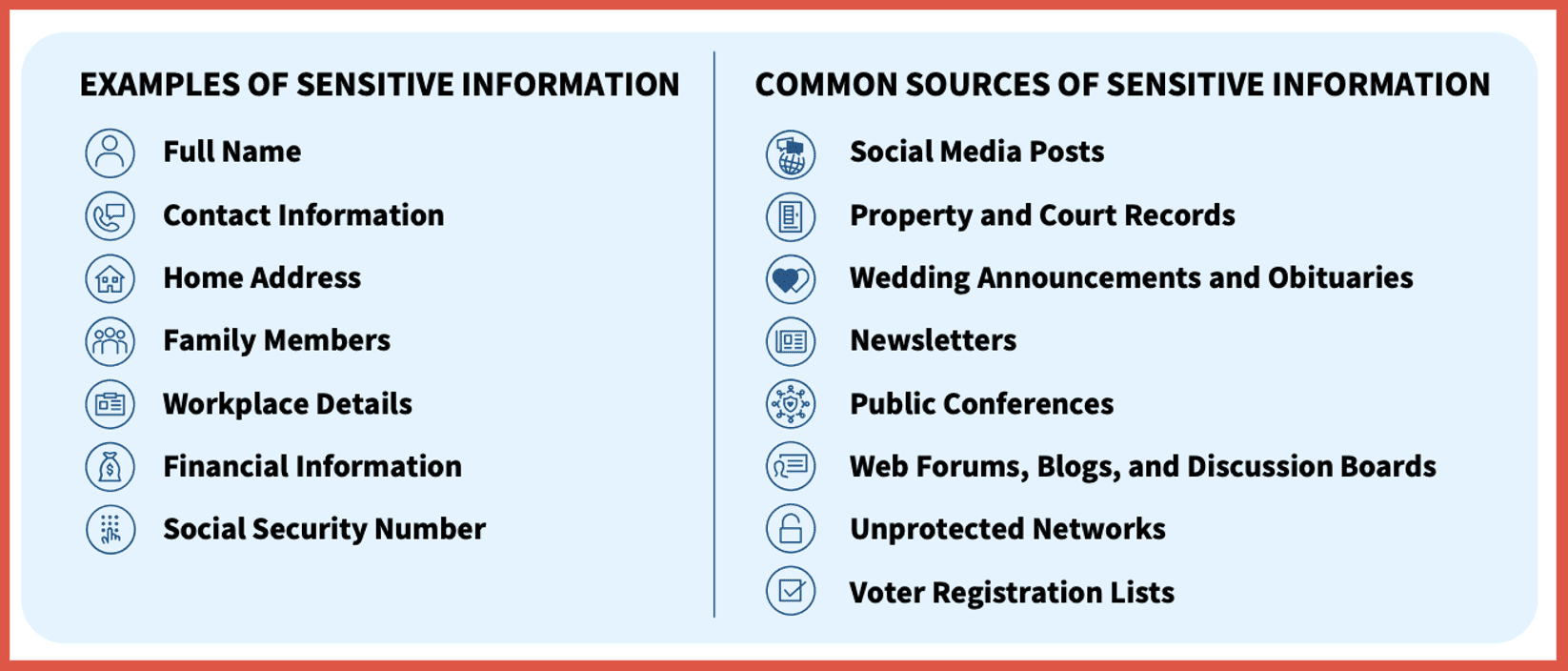
To start, information security (infosec) can be thought of as an umbrella term, while cybersecurity is a specialization underneath that umbrella. Using the terms interchangeably can lead to gaps in your defense strategy as cyber security focuses on the digital realm, while information security protects data in all forms.
Information Security
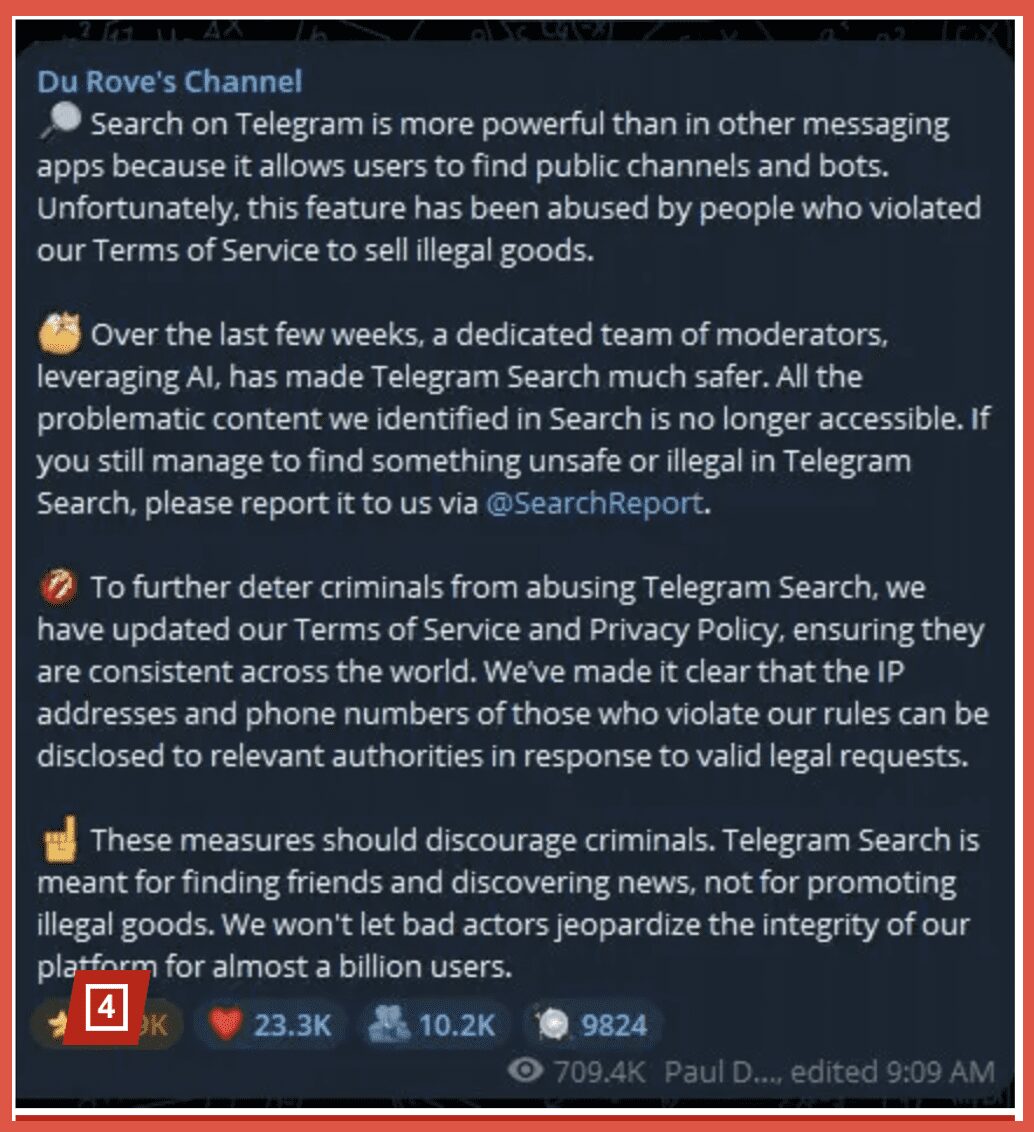
Information Security is the broad practice of protecting information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction. This includes both data in the digital realm, as well as physical data (think of a file on your computer and a file in your filing cabinet). The goal of information security is to protect the CIA Triad (note that since cybersecurity is a subset of information security, these goals align to cybersecurity as well – the scope is just more specific). The CIA Triad stands for confidentiality, integrity, and availability:
- Confidentiality: is your sensitive information only accessible to those authorized to see it?
- Common Threats: phishing, man in the middle attacks, human error
- Integrity: is your data authentic, accurate, and reliable?
- Common Threats: man in the middle attacks, human error, malware, hardware/software glitches
- Availability: are the systems, networks, and data up and running whenever authorized users need them?
- Common Threats: distributed denial of service attacks, hardware failure, ransomware, natural disaster
Examples of information security would be the practice of shredding sensitive paper documents, office keycard systems, and encryption policies. Threats against strong information security include theft, natural disasters, and physical breaches.
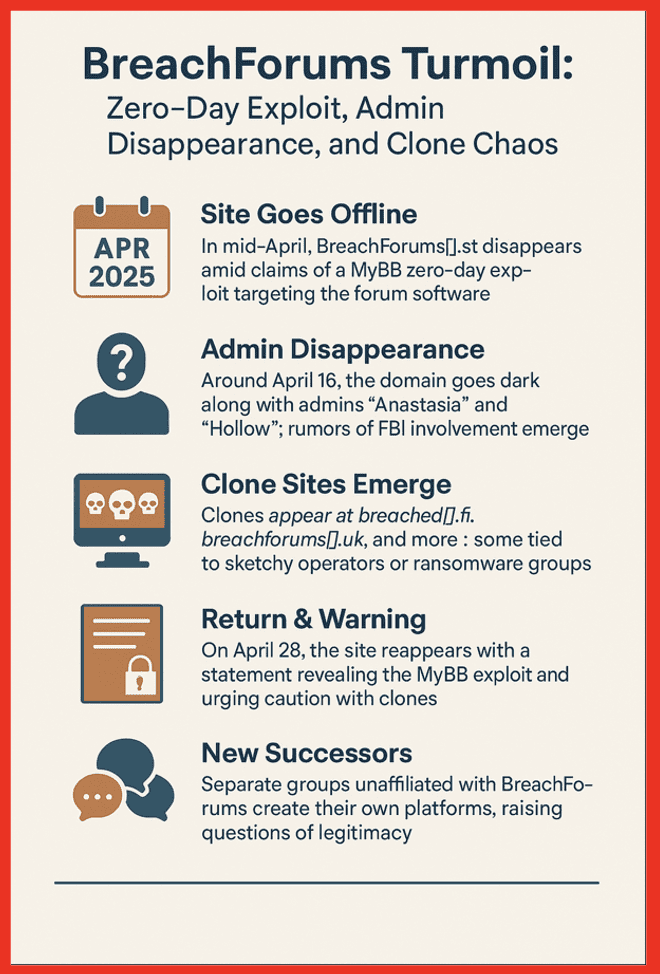
Cybersecurity
Cybersecurity is the practice of defending computers, servers, mobile devices, electronic systems, networks, and data from malicious digital attacks. If it involves the internet or a digital network, it’s cybersecurity. In the example above, cybersecurity is the data in the digital realm – a file on your computer (and the systems, networks, and hardware that house it). The goal in cybersecurity is to protect against cyber attacks – hacking, malware, phishing – to name a few. Examples of cybersecurity would be firewalls, antivirus software, and securing “Internet of Things” (IoT) devices. Threats against secure cybersecurity include cyber warfare, hacking, and data breaches.
How They Work Together
Security is a holistic culture, not just a software update. Information security and cybersecurity work together in creating overlapping layers of defense. You cannot have a robust security policy without incorporating both: the physical and digital layers of defense and policies covering both.
For example, infosec would set the overall policy of protecting and encrypting data (business level decision based on risk), while the cybersecurity division would implement the tech to do so (firewalls, encryption, multi-factor authentication, etc). In a situation where a breach or attack does happen, the two have distinct roles but cannot be successful without the other:
- Information Security
- Determines the data that was stolen
- Manages the legal and regulatory fallout (GDPR/HIPAA notifications)
- Initiates the Business Continuity Plan to ensure the company stays operational during the cleanup
- Cyber Security
- Identifies the threat details
- Isolates the issue and stops it from continuing
- Patches the vulnerability that the hacker used
In short, cybersecurity handles the threats (hackers, viruses, bots) while information security handles the risks (legal compliance, physical safety, data integrity).
Best Practices
With so many of us working from home, it is important to practice good daily security hygiene to make sure that not only the digital data of your company is safe, but potential physical risks are minimized as well. Below is a checklist covering the digital and physical bases to ensure your data stays private and your hardware stays safe:
Digital Checklist (Cybersecurity):
Protect your devices and network from remote attacks.
- Secure the Router:
- Change the default admin password
- Enable WPA3 (or WPA2-AES) encryption
- Turn off WPS (Wi-Fi Protected Setup
- Segment Your Wi-Fi:
- Set up a “Guest Network” specifically for your work laptop
- This keeps your work data separate from “unsecure” items like an Amazon Alexa or gaming console
- Set up a “Guest Network” specifically for your work laptop
- Enable MFA/2FA:
- Use an authenticator app (like Google Authenticator or Authy) on every account
- Automate Updates:
- Set your OS (Operating System) and browser to “Auto-Update” so you get security patches immediately
- VPN for Public Use:
- Use a reputable VPN to create an encrypted “tunnel” for your data
InfoSec Checklist:
Protect the physical environment and the data itself.
- Full Disk Encryption:
- Ensure BitLocker (Windows) or FileVault (Mac) is on
- The “Clear Desk” Policy:
- Don’t leave passwords on sticky notes
- Shred any documents containing client names, addresses, or account numbers before throwing them away
- Visual Privacy:
- Use a privacy screen filter on your monitor
- Secure Backup (3-2-1 Rule):
- Keep 3 copies of your data:
- 2 different types of media (laptop and an external drive)
- 1 copy stored off-site (encrypted cloud storage like Backblaze or iCloud)
- Keep 3 copies of your data:
- Webcam Cover:
- Have a physical slide cover for your camera is the only 100% guarantee against “cam-fecting”
- Lock your computer when you step away