April 16, 2026
A previously unknown group calling itself Harakat Ashab al-Yamin al-Islamia (Ashab al-Yamin) has recently emerged, claiming responsibility for a series of attacks across Europe and quickly attracting attention from analysts and media outlets. Reporting by CBS News, citing researchers from Tech Against Terrorism and others, has highlighted the group’s sudden appearance and raised questions about whether it represents a genuine operational network or a rapidly assembled media construct linked to broader geopolitical dynamics.
The group’s presence appears largely confined to Telegram, where it publishes a mix of attack claims, propaganda, and geopolitical commentary. Its Telegram footprint is fragmented, with limited persistent content and much of its activity preserved through secondary or supporter accounts.
Rather than evaluating Ashab al-Yamin as a standalone entity, a closer examination of its Telegram activity suggests a different framing. Patterns of shared content, cross-channel distribution, and overlapping narratives indicate that the group operates within a broader, loosely connected ecosystem of Iranian-aligned channels. This ecosystem overlaps with networks commonly associated with the “Islamic Resistance,” where claims, media, and messaging circulate across multiple accounts rather than originating from a single source.
This raises a central question: is Ashab al-Yamin a distinct organization, or a visible node within a broader networked ecosystem? Let’s dive in.
Telegram Activity and Content Patterns
As of early April 2026, the group’s primary Telegram channel, Harakat Ashab al-Yamin al-Islamia, appears to have been removed or banned from the platform. The most recent identifiable content, dated April 4, included a video claiming responsibility for an attack targeting a building associated with Christians for Israel in Nijkerk, Netherlands. No clear successor channel has been identified at the time of writing, further reinforcing the group’s fragmented and unstable presence across Telegram, where continuity appears dependent on redistribution rather than sustained ownership of a single channel.
As a result, much of the group’s observable activity is derived from secondary or supporter channels, such as صفي الدين, which continues to circulate attack claims, propaganda, and related content attributed to the group.
Initial review of these channels suggests they do not function solely as claim-of-responsibility outlets. Instead, they operate as hybrid media nodes, combining attack claims, geopolitical commentary, and propagandistic amplification of broader regional narratives.
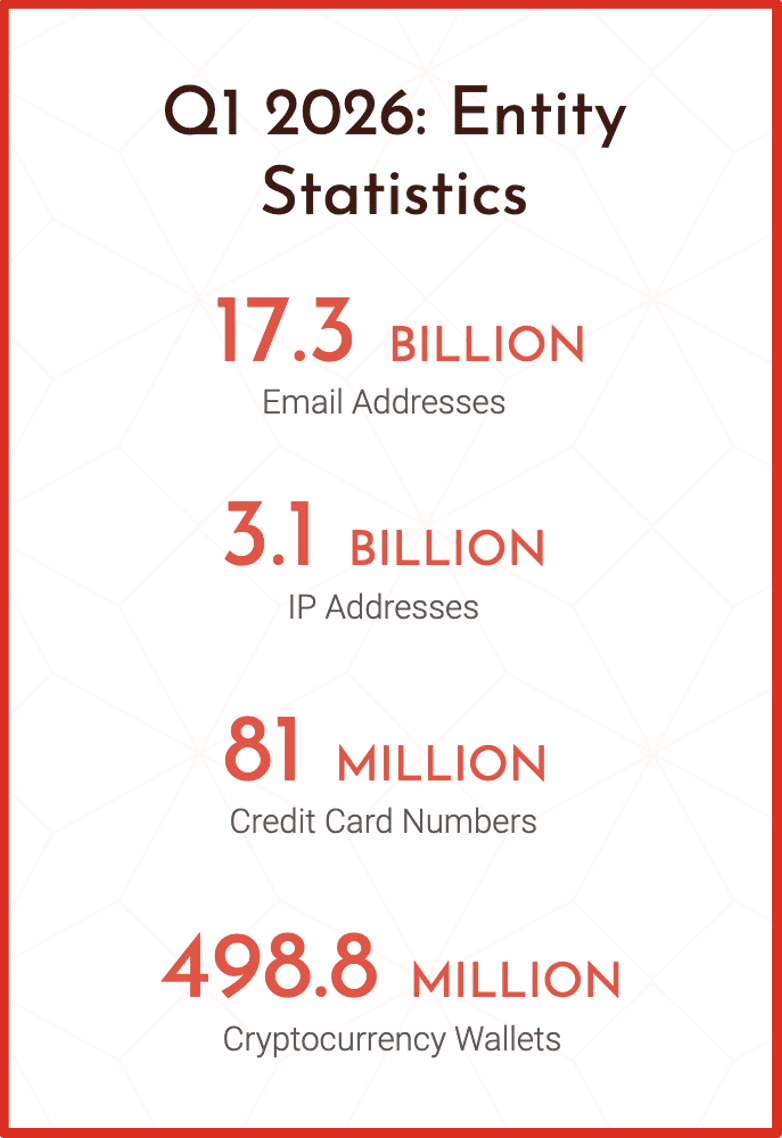
For example, content includes battlefield or intelligence-style analysis, such as satellite imagery purportedly showing damage to U.S.-linked air facilities in Bahrain and Kuwait following Iranian strikes. The accompanying text describes specific targets such as hangars, fuel storage, and drone infrastructure.
Figure 1: Satellite imagery / strike analysis post
This style of posting is consistent with content observed across pro-Iranian Telegram channels, where content blends battlefield updates, geopolitical commentary, and narrative amplification alongside claims of responsibility for attacks in Europe.
Figure 2: London ambulance attack claim video
One such example includes a video documenting an arson attack in London targeting ambulances associated with a Jewish community organization. The accompanying Arabic-language caption frames the incident as an operation carried out by Ashab al-Yamin, referencing a synagogue in the British capital and linking the action to broader anti-Israel narratives.
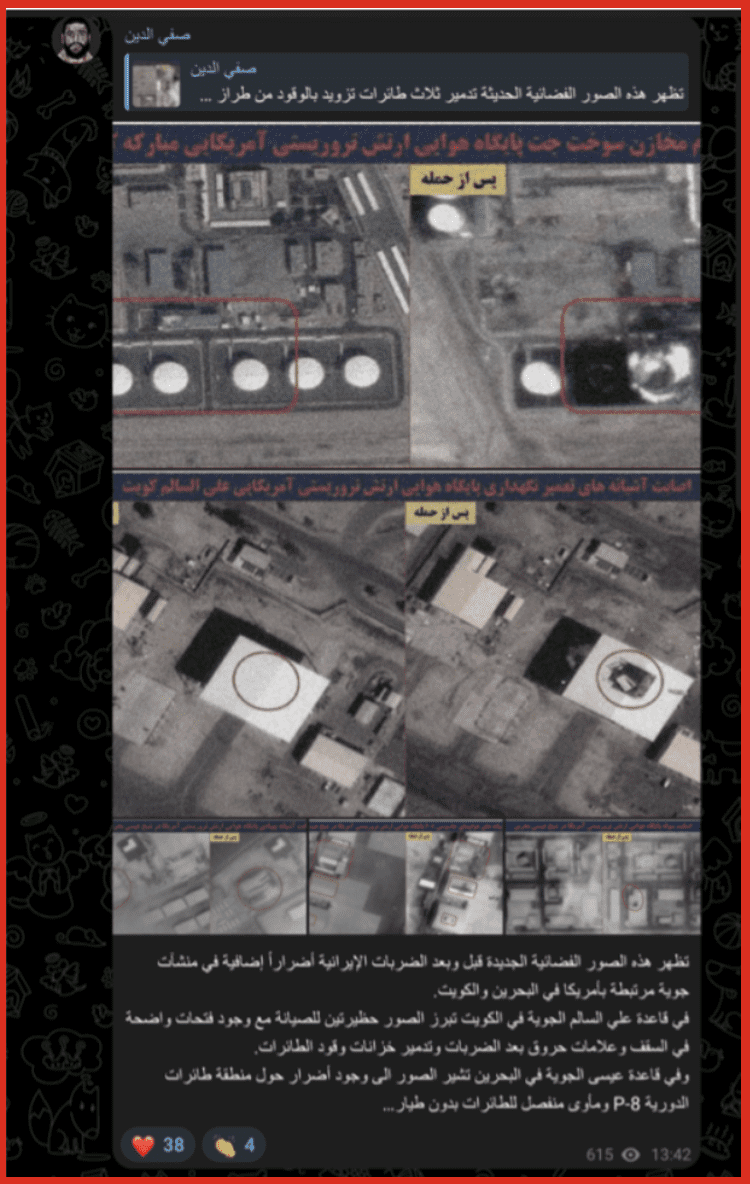
More recent content attributed to the group includes claims related to an attack targeting a commercial center in Amsterdam. One such post states:
Figure 3: Amsterdam attack video from Ashab al-Yamin
حركة أصحاب اليمين الإسلامية تتبنى استهداف المركز التجاري العالمي في أمستردام، وتدعو شعوب أوروبا إلى الابتعاد عن المصالح الأمريكية والصهيونية فوراً.
The limited availability of such claims on the group’s official channel, combined with their continued circulation across secondary and affiliated channels, complicates efforts to assess a single point of origin. Instead, messaging is distributed across multiple accounts, where content persists through redistribution rather than consistent publication from a single source.
Content Origination and Cross-Channel Linkages
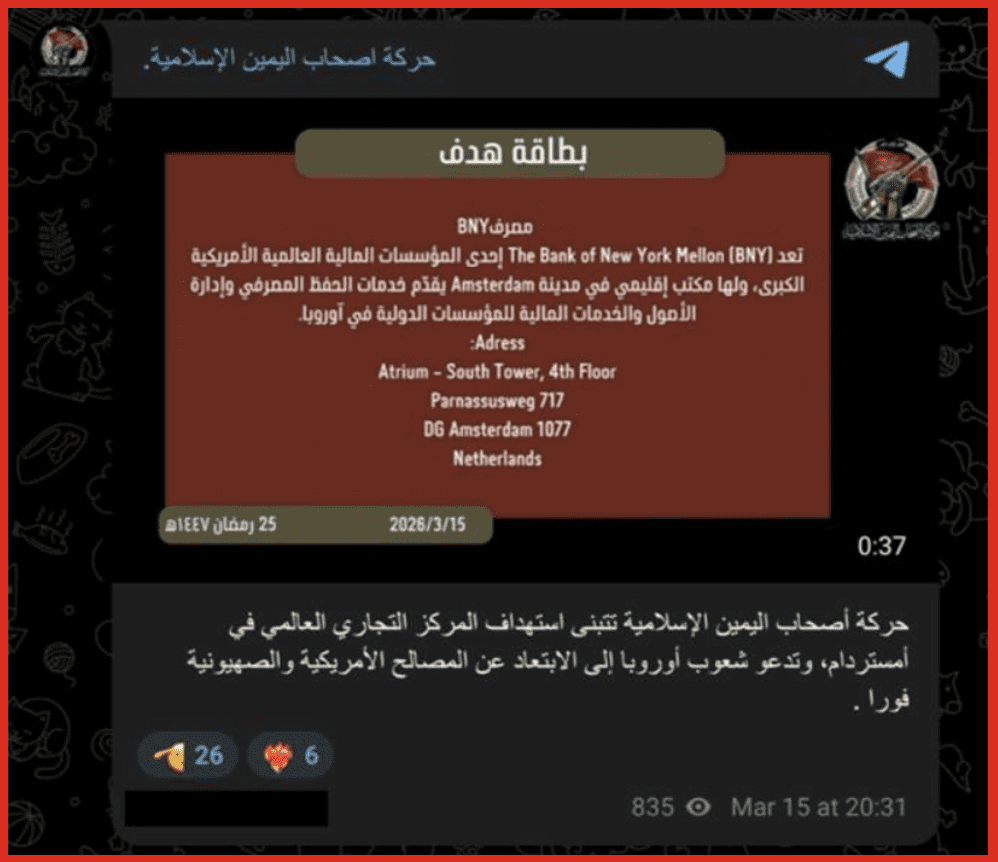
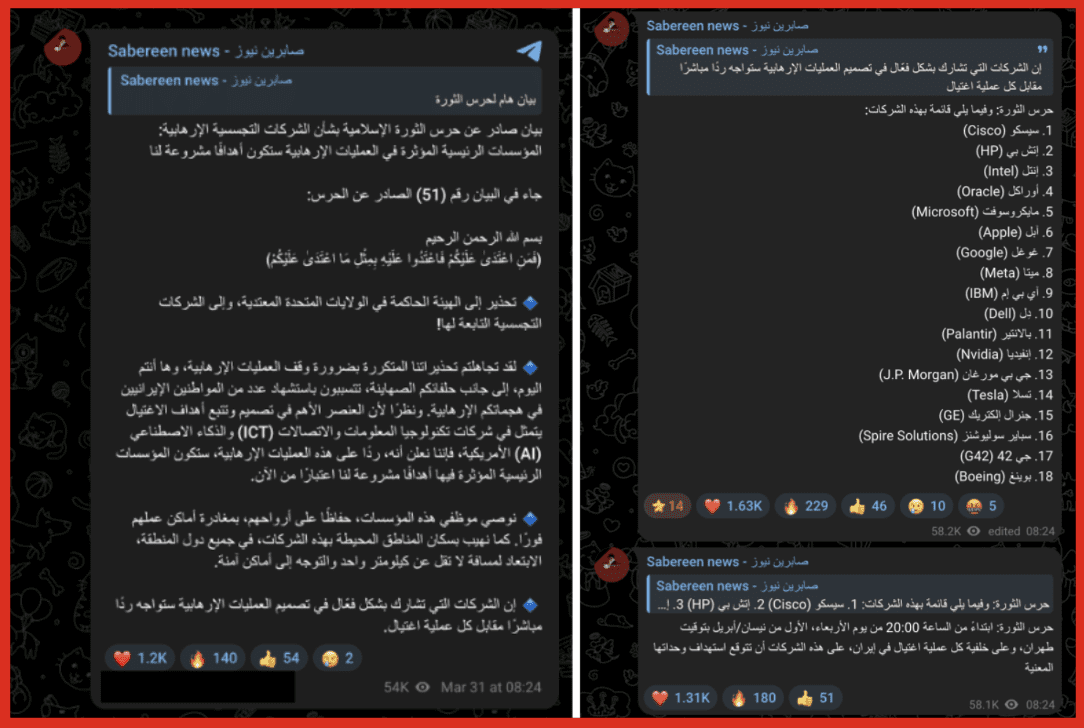
One particularly notable detail is the presence of Sabereen News branding within video content that was previously reposted by Ashab al-Yamin’s official Telegram channel.
Figure 4: Ashab al-Yamin post showing Sabereen News watermark; London attack
Sabereen News is a Telegram-based media outlet widely associated with Iranian-aligned networks, with multiple analyses pointing to links with Iran’s Islamic Revolutionary Guard Corps–Qods Force (IRGC-QF) and Iran-backed militia groups. Research by the Washington Institute for Near East Policy notes “strong indicators” of IRGC-QF connections and highlights that the channel first appeared on Telegram in January 2020. More recent reporting from Iran International similarly reflects its position within IRGC-linked messaging networks.
The visible Sabereen News watermark within the footage of the London ambulance attack suggests that the video was either sourced from, or circulated through, an Iranian-aligned media channel prior to being reposted by Ashab al-Yamin. Rather than serving as definitive proof of origin, this overlap indicates participation in a shared media pipeline where content is reused and redistributed across channels.
This interpretation is further supported by activity observed on Sabereen News channel, which regularly publishes operational updates, threat messaging, and geopolitical narratives aligned with Iranian interests.
Additional Sabereen content illustrates this narrative.
Figures 6 & 7: Sabereen News corporate targeting / company list
In this example, Sabereen News publishes a list of Western companies, including technology firms, financial institutions, and defense-related entities, framing them as potential targets linked to broader geopolitical events. While this is not a direct claim of responsibility, it reflects a broader pattern of signaling and narrative shaping seen across affiliated channels.
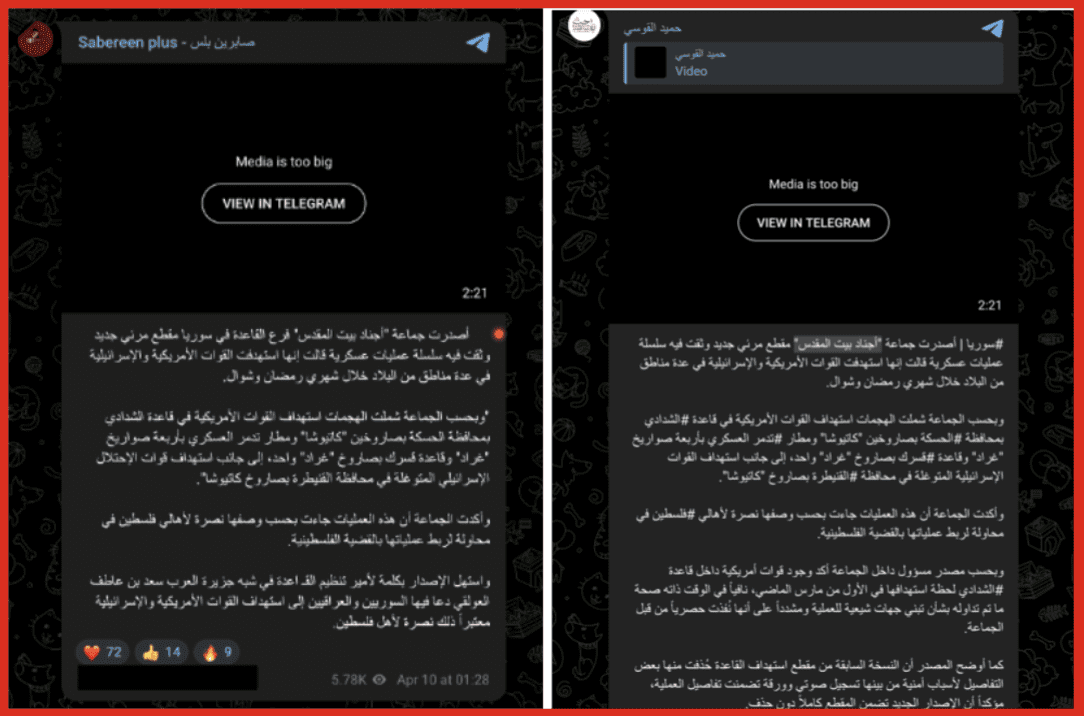
Additional recent content from Sabereen News further illustrates its role as a central distribution node within this ecosystem. In some cases, this aggregation extends beyond Iranian-aligned actors.
For example, Sabereen News has been observed resharing content attributed to Sunni jihadist groups, including material linked to Ajnad Bayt al-Maqdis. The original post appears to have been published by a Telegram account operating under the name “hamid alqawsi,” before being redistributed through Sabereen. The group’s recent pledge of allegiance to al-Qaeda, dated February 2026, coincides with broader regional escalation reinforcing patterns of opportunistic emergence tied to major geopolitical events. This further illustrates how content moves across distinct networks through centralized amplification channels.
Figures 8 & 9: Original Telegram post from “hamid_alqawsi” account and subsequent repost by Sabereen News
In a separate example, the channel reposts video footage attributed to Hezbollah depicting a missile strike on the Israeli town of Kiryat Shmona. While not directly linked to Ashab al-Yamin, this type of cross-group content aggregation highlights how Sabereen functions as a broader amplification hub, circulating material from multiple actors and reinforcing shared narratives across the network. Channels such as Sabereen News therefore remain key points of observation for tracking how new identities emerge and reappear within this network.
An earlier Telegram channel, Haraka Ashab Al Yamin, identified as one of the first to publish content associated with the Amsterdam attack, appears to have been removed or banned from the platform, further complicating efforts to trace content back to a single point of origin.
Across posts, several additional patterns emerge that reinforce this ambiguity. The language is primarily Arabic, with no observable use of Farsi despite speculation of Iranian association, and messaging consistently incorporates anti-Israel and anti-Western themes aligned with broader regional narratives. Taken together, these characteristics further complicate attribution and raise questions about the group’s structure, consistency, and underlying coordination, which become more apparent when examining its claims and media output more closely.
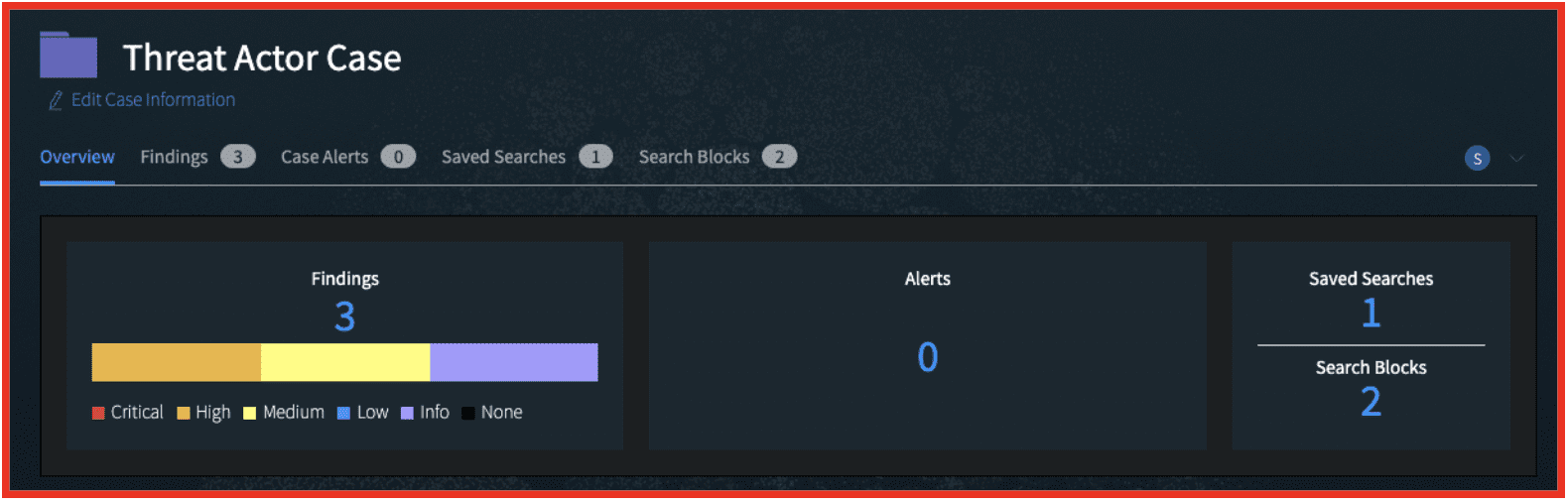
Indicators of Authenticity vs Narrative Construction
The available Telegram content presents a mixed picture of Ashab al-Yamin’s credibility as an operational group. While the channel attempts to project visibility through attack claims and messaging, it lacks several features typically associated with more established militant organizations.
Unlike known Iranian-aligned and PMF-affiliated groups, Ashab al-Yamin does not consistently produce formalized statements, leadership messaging, or a clearly defined media structure. Its presence appears limited in scale, with no clear evidence of sustained or centralized coordination.
At the same time, the quality and style of its media output vary noticeably, with some videos appearing more refined and others more rudimentary. This inconsistency likely reflects contributions from multiple actors rather than a single coordinated media wing. This aligns with assessments from analysts cited in CBS News, who note that such output may be designed to generate psychological impact rather than demonstrate operational sophistication.
The group’s messaging also closely tracks ongoing geopolitical developments, suggesting a degree of responsiveness and an understanding of how to maximize visibility within a rapidly evolving information environment. Taken together, these patterns support the interpretation put forward by the Foundation for Defense of Democracies: that Ashab al-Yamin may function less as a centralized organization and more as a front identity used to claim attacks carried out by loosely connected or externally recruited individuals. This ambiguity becomes more meaningful when placed alongside the wider ecosystem in which the group operates.
More broadly, this model reflects a pattern observed across comparable ecosystems, where decentralization, narrative amplification, and perceived reach are often prioritized over formal organizational structure. In such contexts, visibility and attribution can be strategically leveraged to amplify perceived impact without requiring sustained operational capability.
PMF and Iranian-Aligned Telegram Ecosystem
Rather than viewing Ashab al-Yamin in isolation, its activity is more clearly understood when placed alongside a broader cluster of Telegram channels linked to the “Islamic Resistance” ecosystem.
This ecosystem includes a mix of militia-linked channels, media outlets, and amplifier accounts. Channels such as:
· شباب الإسلام
· أصحاب الكهف
· جيش الغضب
· صفي الدين
· التعبئة الشعبية للمقاومة الإسلامية في العراق ( بسيج العراق)
· القدرات العسكرية الإيرانية
These channels regularly publish claims, updates, and propaganda tied to attacks against U.S. and allied targets, while also forwarding and resharing content from one another. These channels function as an interconnected network, regularly cross-posting and reinforcing shared narratives.
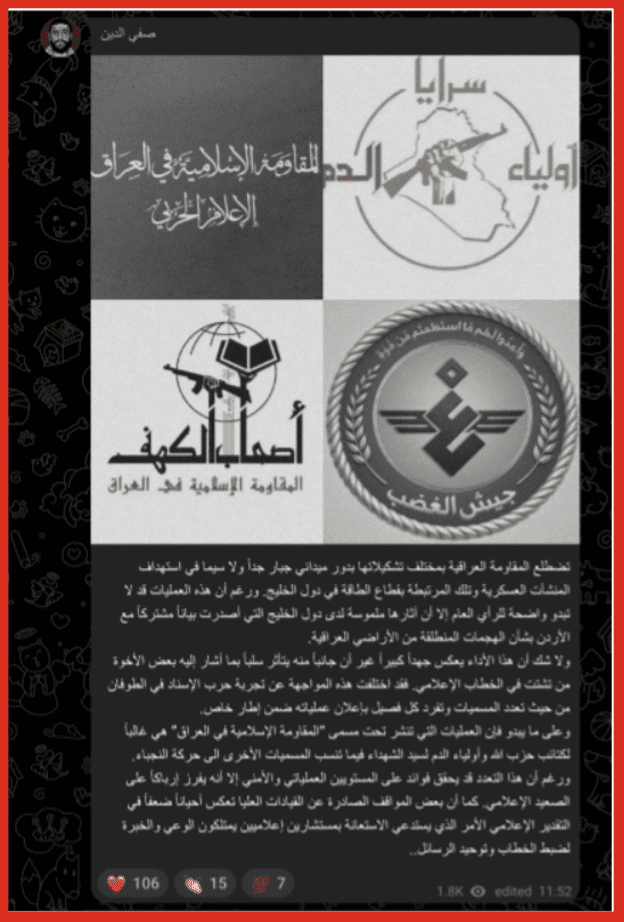
Figure 11: Safee al-Deen / ecosystem connections post
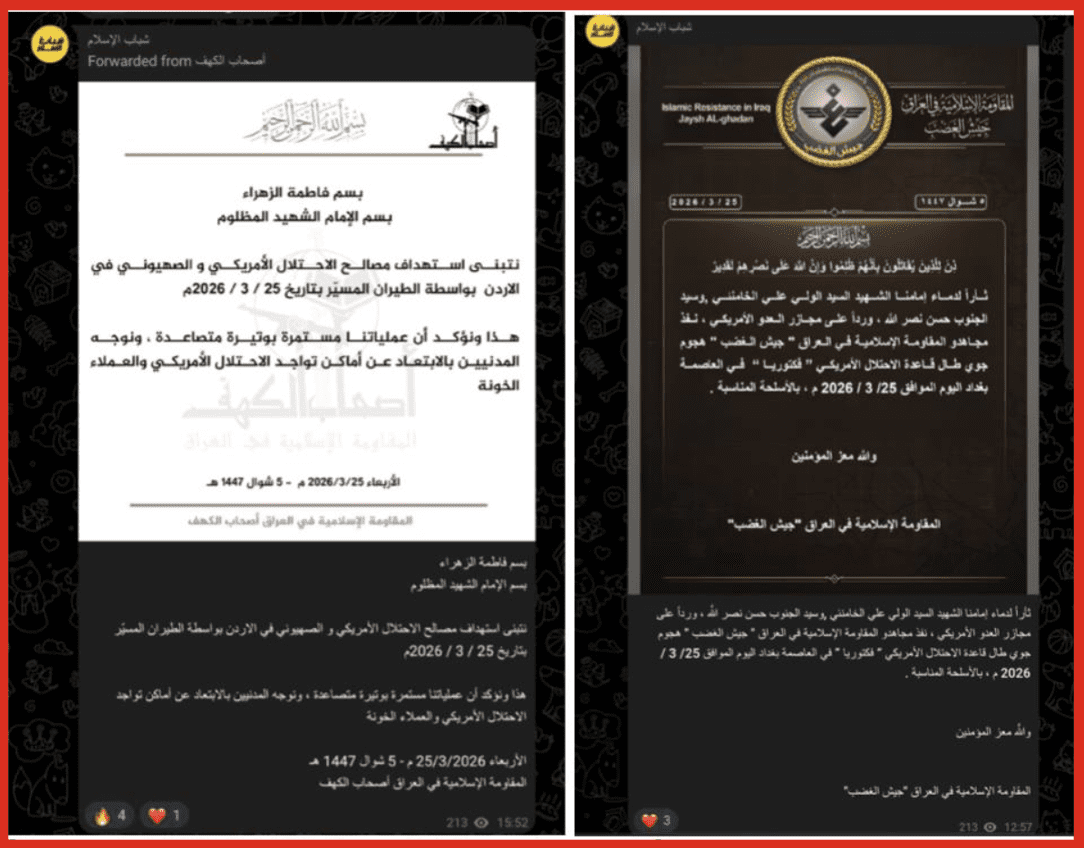
Posts such as the above highlight explicit relationships between multiple groups operating under the umbrella of the “Islamic Resistance,” including Ashab al-Kahf and Jaysh al-Ghadab.
Ashab al-Kahf is an Iraqi militia group aligned with the Islamic Resistance in Iraq, known for claiming attacks against U.S. military and allied targets in the region. Its Telegram presence reflects a structured communication style, including consistent branding, formalized statements, and clearly framed claims of responsibility.
Jaysh al-Ghadab similarly operates within this ecosystem, publishing claims and messaging tied to attacks and broader resistance narratives. Like Ashab al-Kahf, its content reflects a more established and consistent media presence, with recognizable visual identity and integration into a wider network of affiliated channels.
While these groups exhibit more structured branding and communication styles, they operate within the same broader environment as Ashab al-Yamin. Figures 14 and 15 illustrate formalized statements published by Ashab al-Kahf and Jaysh al-Ghadab, both of which were subsequently forwarded by the Shabab al-Islam channel. This pattern highlights how official statements originating from more established actors are redistributed across affiliated channels, reinforcing shared narratives, and expanding reach.
Figures 14 & 15: PMF formal statement example
Both statements follow a consistent format typical of PMF-aligned media output, including religious framing, attribution of attacks against U.S. and Israeli interests, and references to specific operations. For example, one statement claims responsibility for a drone attack targeting Israeli-affiliated infrastructure in Jordan, while emphasizing civilian evacuation warnings and framing the operation within a broader resistance narrative. The second statement similarly adopts formalized language, invoking religious justification, and positioning the attack within the context of ongoing regional conflict. This contrast becomes more apparent when comparing how similar attack-related content appears across different channels within the network.
Figure 16: London ambulance attack claim Ashab al-Yamin TG channel
Figure 17: London ambulance attack claim: Safee al-Deen TG channel
Figures 16 and 17 show the same London ambulance attack being circulated through Ashab al-Yamin and Safee al-Deen channels, illustrating how identical content is redistributed across different nodes within the network, often with variations in framing and presentation.
These examples illustrate how similar content is circulated, reframed, and redistributed across different channels, reinforcing visibility and narrative consistency.
A Networked Playbook
The emergence of Ashab al-Yamin aligns with a broader pattern seen across similar ecosystems: the rapid creation of new identities designed to claim responsibility, amplify narratives, and generate strategic effects. Recent analysis by Militant Wire similarly suggests that the group may function less as a traditional organization and more as an “astroturfed” identity embedded within existing Iranian-aligned networks, leveraging low-cost, high-visibility activity to maximize perceived impact.
Rather than representing the development of a traditional, hierarchical organization, this model prioritizes speed, flexibility, and visibility. New entities can quickly establish a presence, insert themselves into ongoing events, and reinforce narratives already circulating across interconnected channels. As noted in reporting by CBS News, even relatively unsophisticated or ambiguous content can achieve outsized strategic effects. This aligns with analysis from the Foundation for Defense of Democracies, which notes that such models can rely on low-cost, deniable actors and coordinated messaging without requiring a formal organizational structure. Recent research by the Global Network on Extremism and Technology similarly highlights how digital actors across different ideological and operational backgrounds can converge within shared wartime ecosystems, forming loose networks that amplify common narratives and targets.
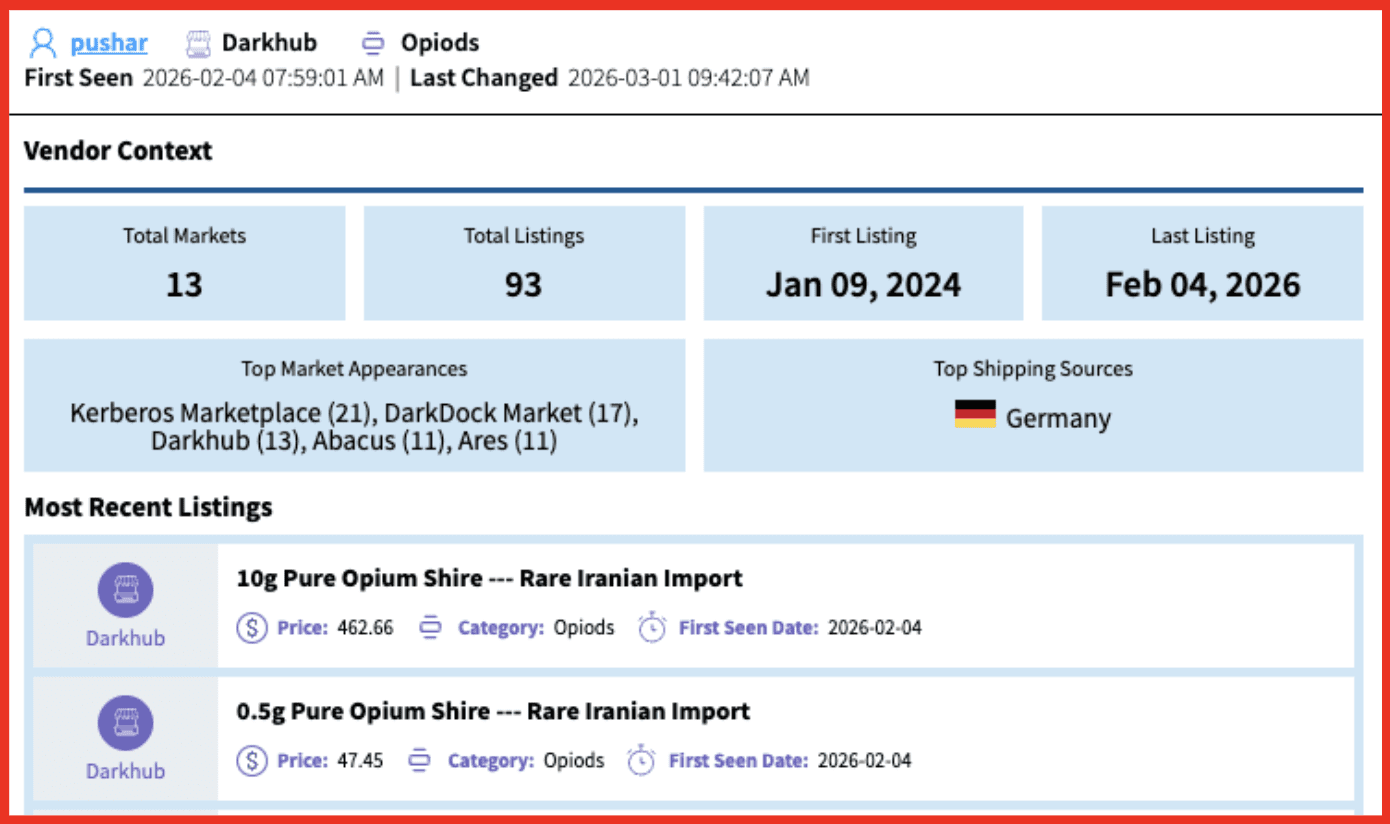
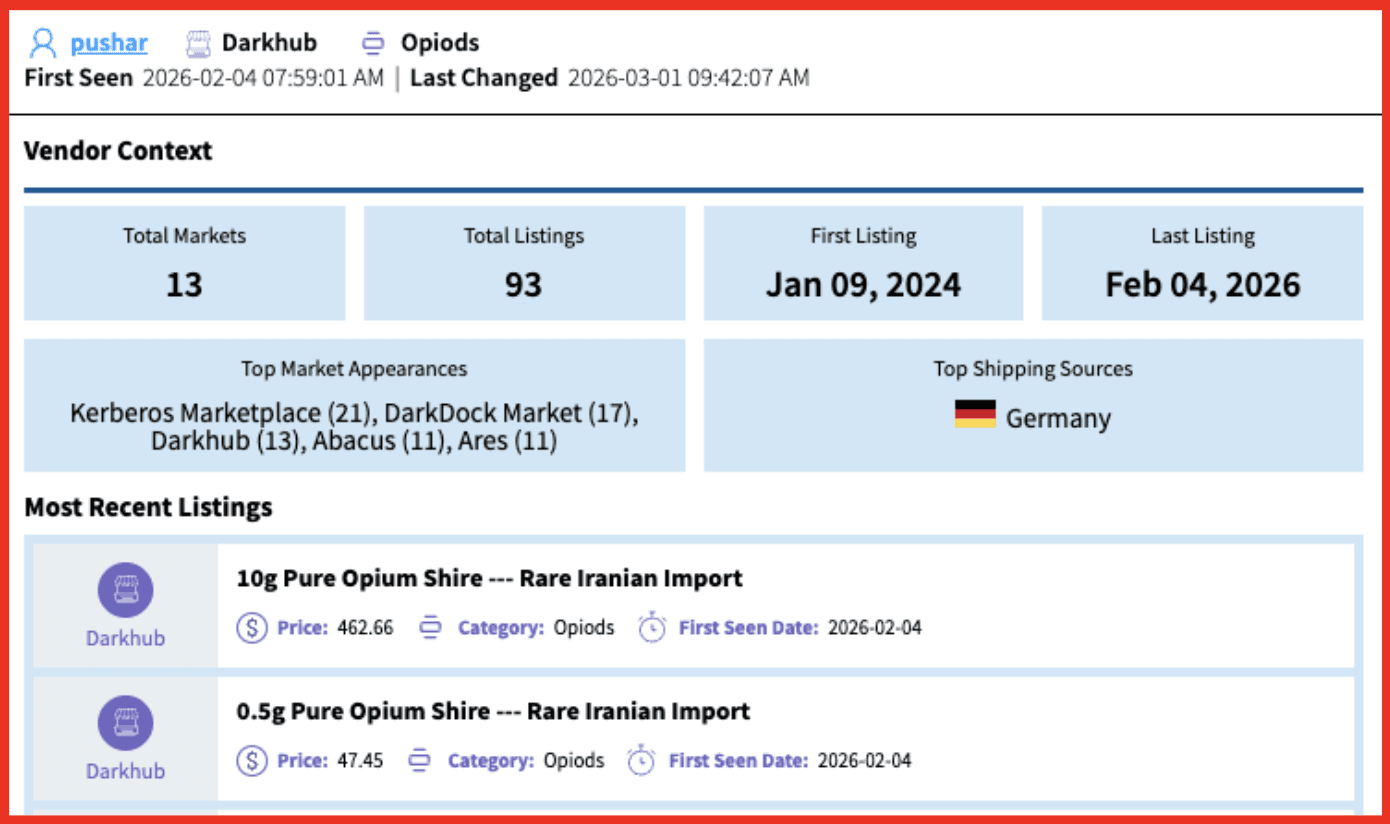
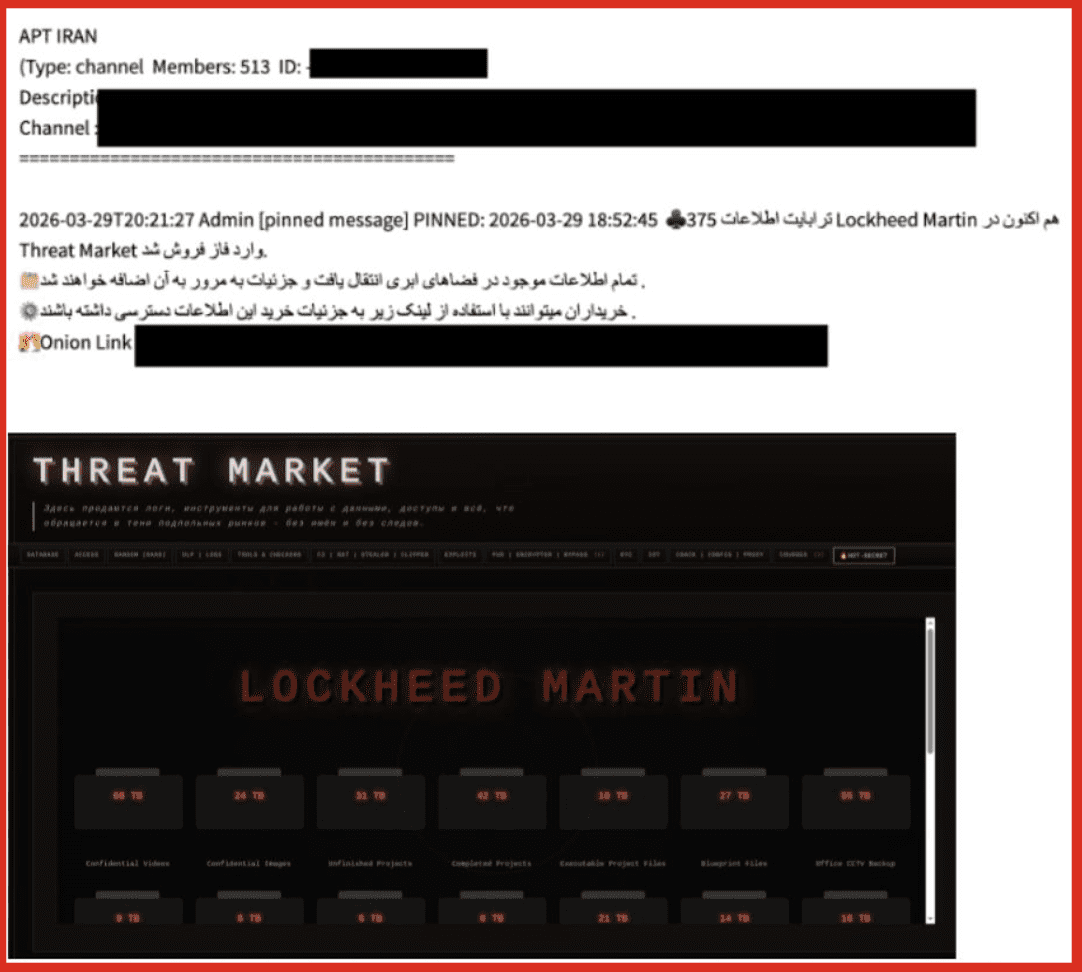
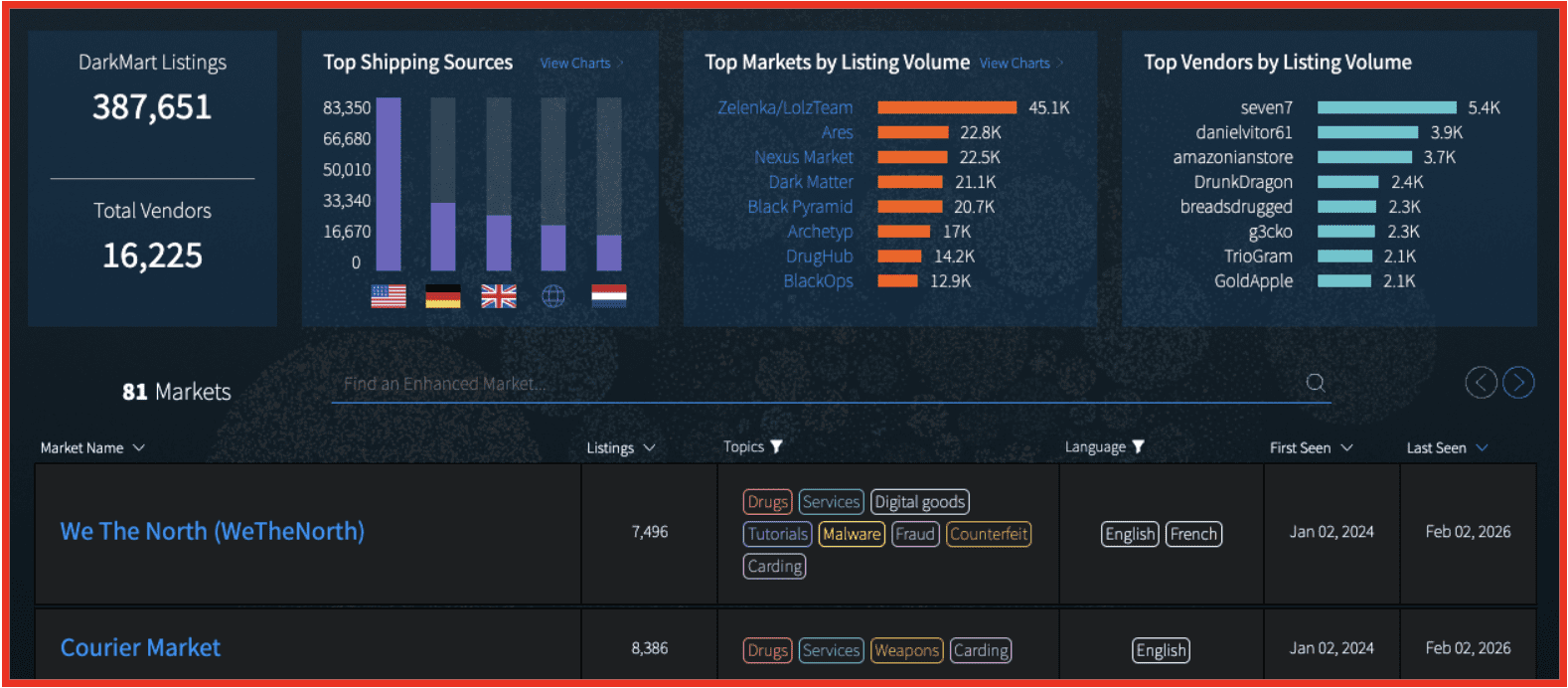
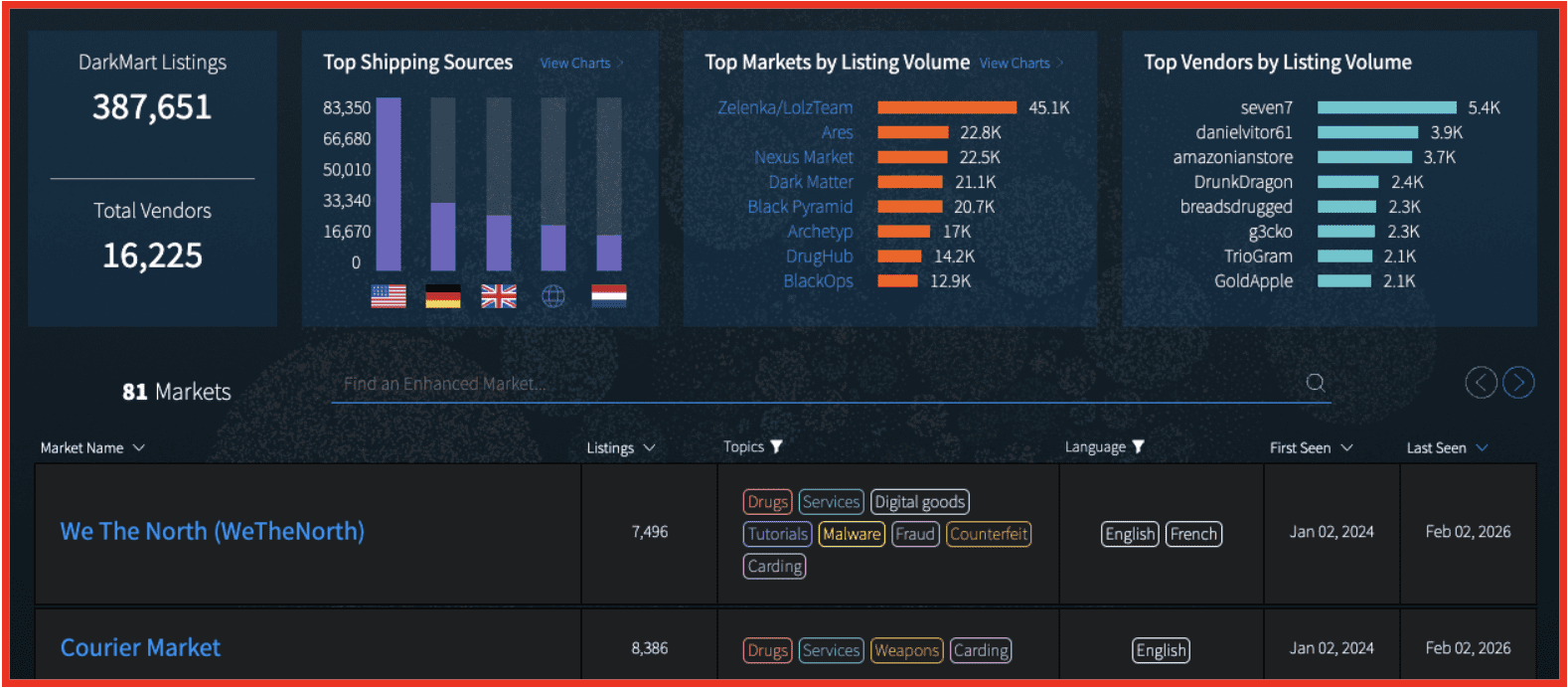
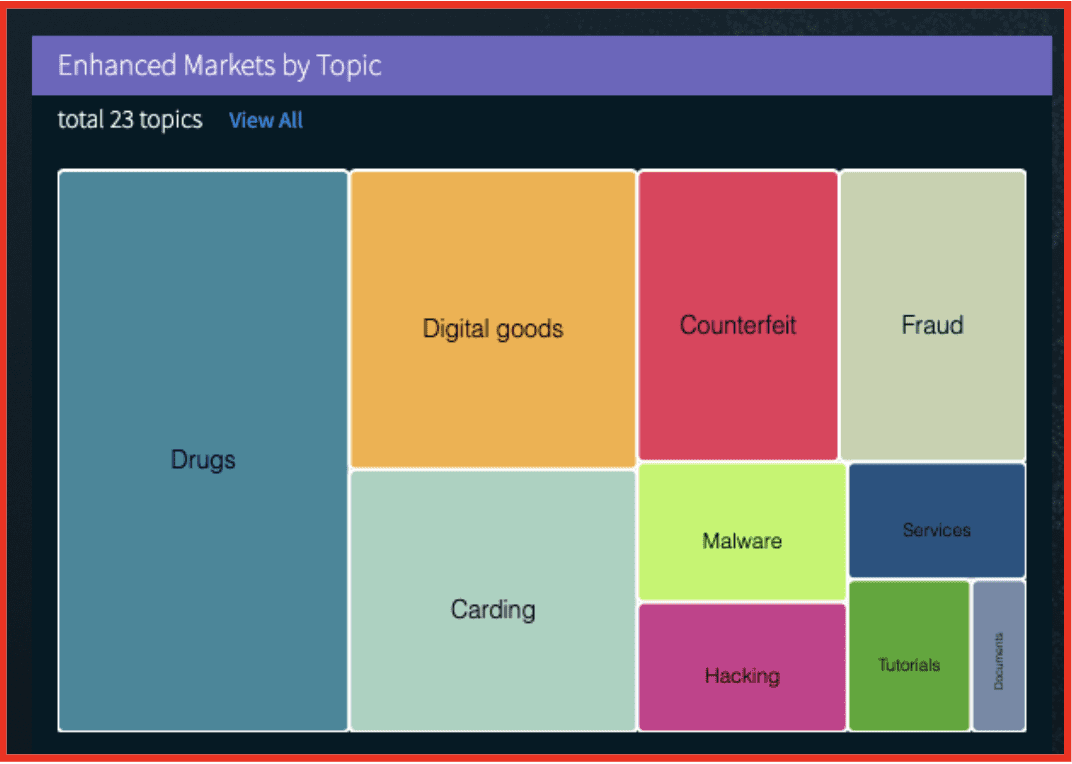
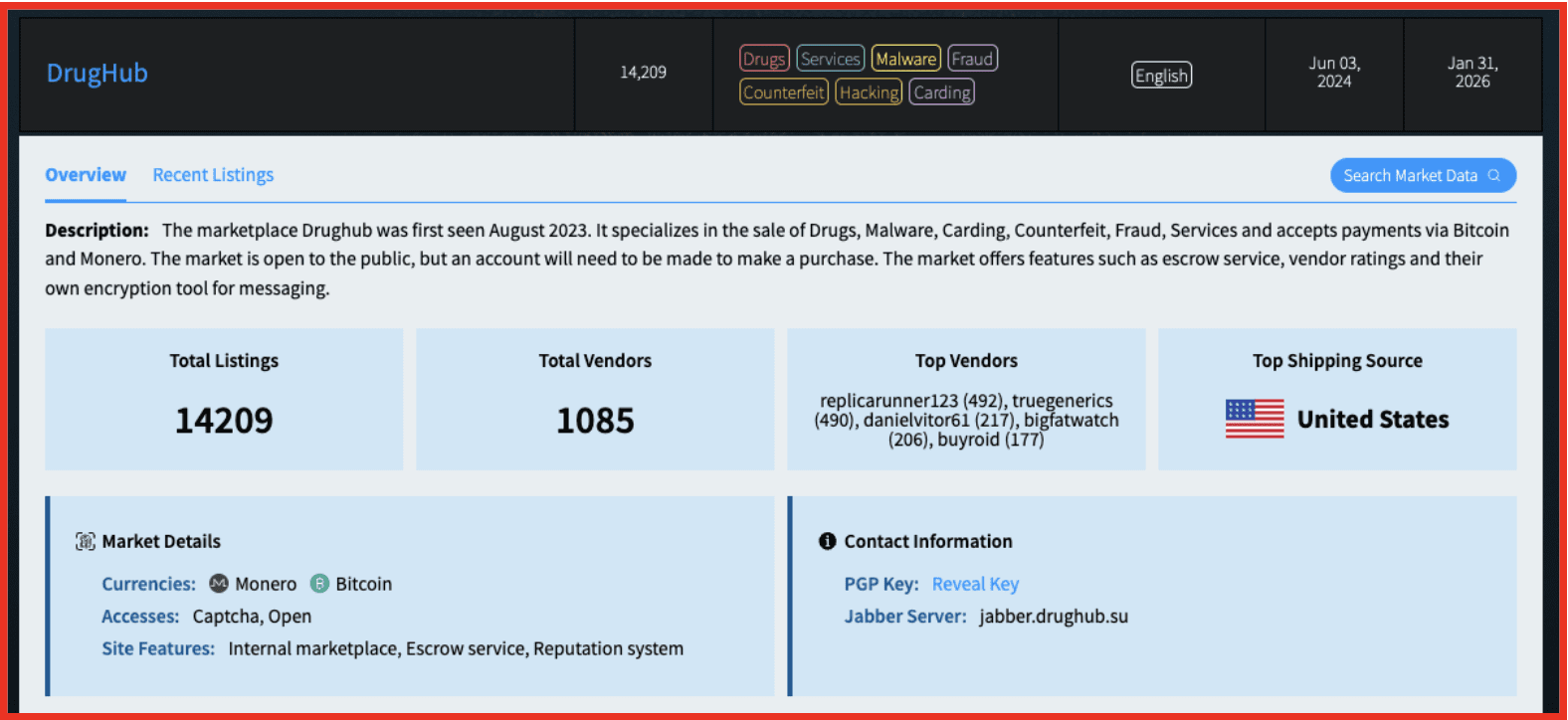
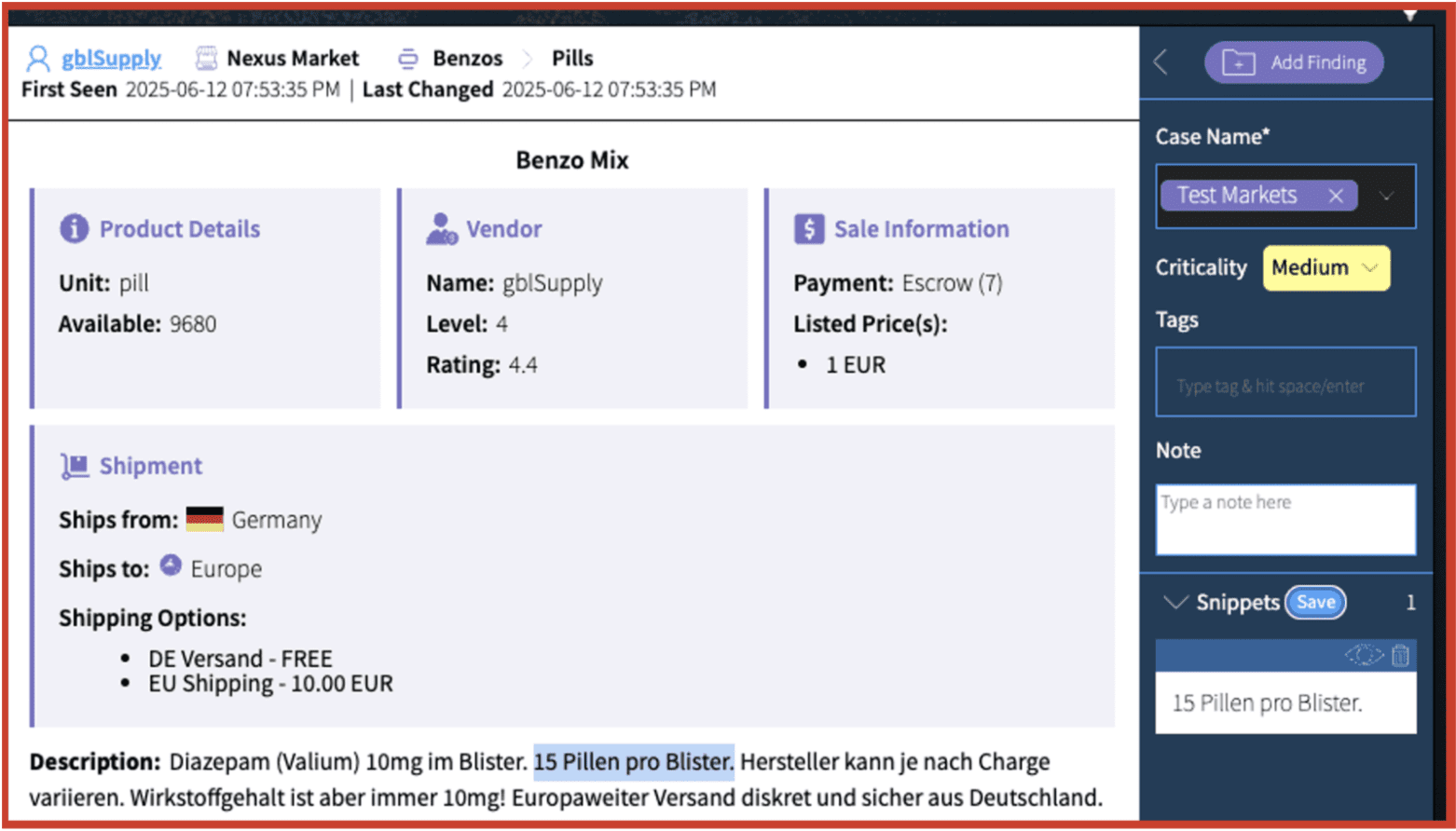
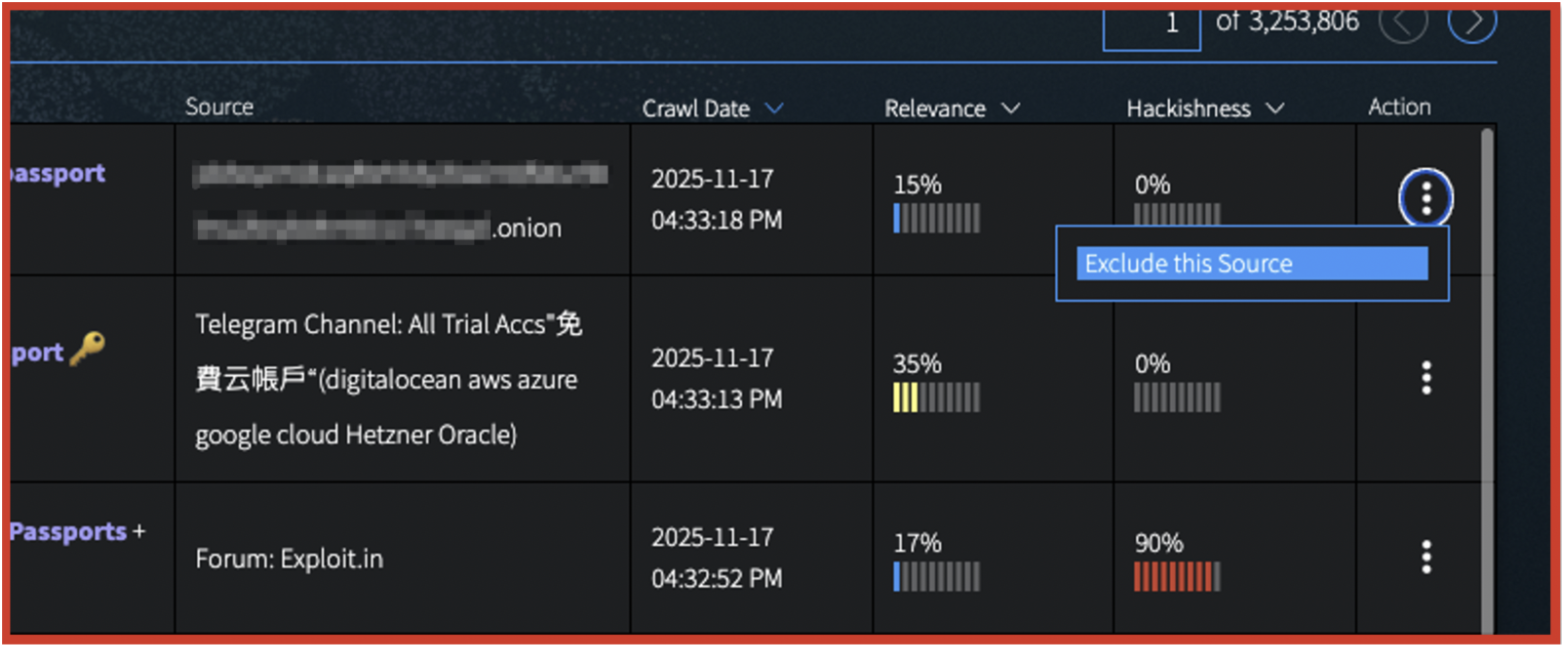
These dynamics are not limited to militant media channels. Similar patterns can be observed among pro-Iranian hacktivist groups, which use Telegram to promote alleged data breaches and advertise them on darknet marketplaces. For example, “APT Iran” has claimed to possess stolen data from Lockheed Martin, promoting it through Telegram and advertising it on a Russian-language darknet marketplace known as “Threat Market.”
The listing advertises an estimated value of approximately $374 million, with an exclusive buyout price nearing $600 million, alongside tiered pricing for partial data access. While these figures remain unverified, their scale reflects a broader pattern of inflated valuation and narrative amplification, where the perceived significance of a breach is emphasized as much as the underlying data itself.
Figures 18 & 19: APT Iran Telegram post referencing Lockheed; Lockheed leak posted on Threat Market
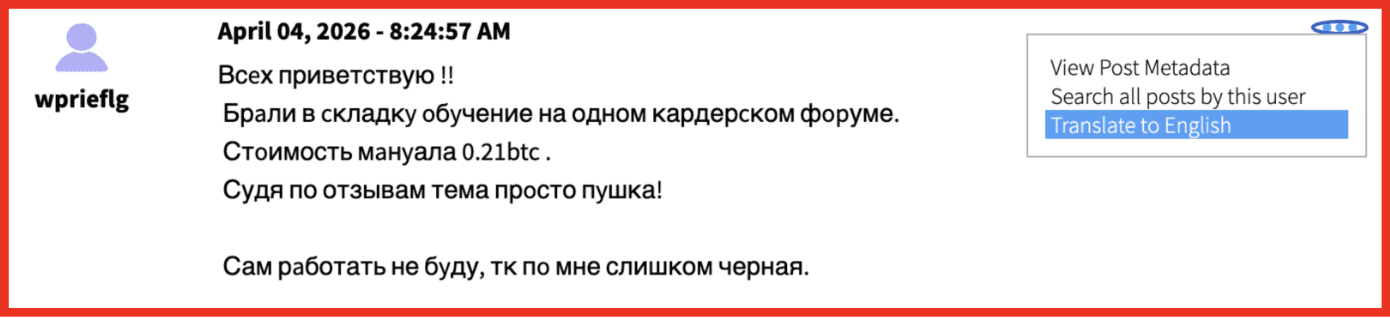
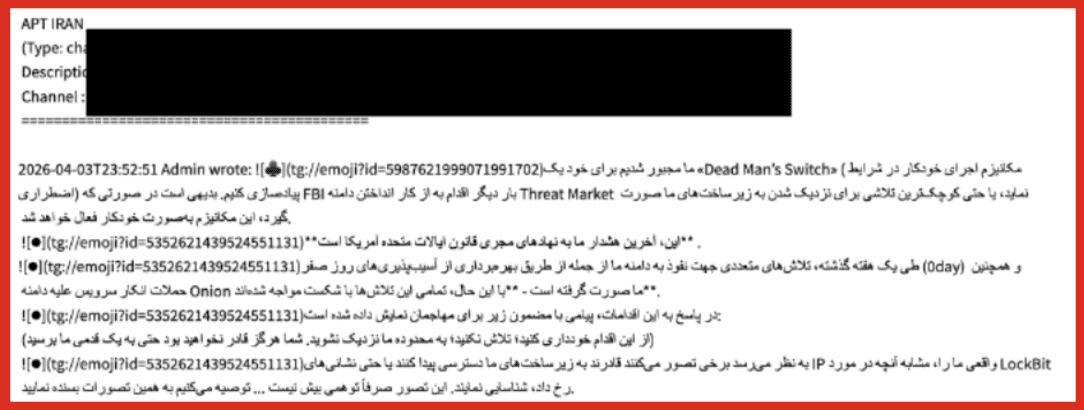
More recent activity suggests increasing instability and responsiveness to external pressure. Following attention surrounding the alleged Lockheed Martin leak, the actor associated with “APT Iran” appears to have changed its Telegram identity to “Brona
Blanco had begun posting images of purported source code tied to the breach. Concurrent messaging in Farsi references potential law enforcement scrutiny, including warnings about FBI targeting of infrastructure linked to Threat Market and the implementation of contingency measures such as a “dead man’s switch.”
Figure 20: APT Iran Telegram post referencing the FBI targeting Threat Market
Figure 21: APT Iran/Brona Blanco Telegram post referencing Lockheed Martin Source Code
While these claims remain unverified, this shift in tone and behavior reinforces a consistent pattern observed across these actors: rapid escalation in claims, reactive messaging driven by perceived pressure, and an emphasis on perceived impact over independently verifiable outcomes.
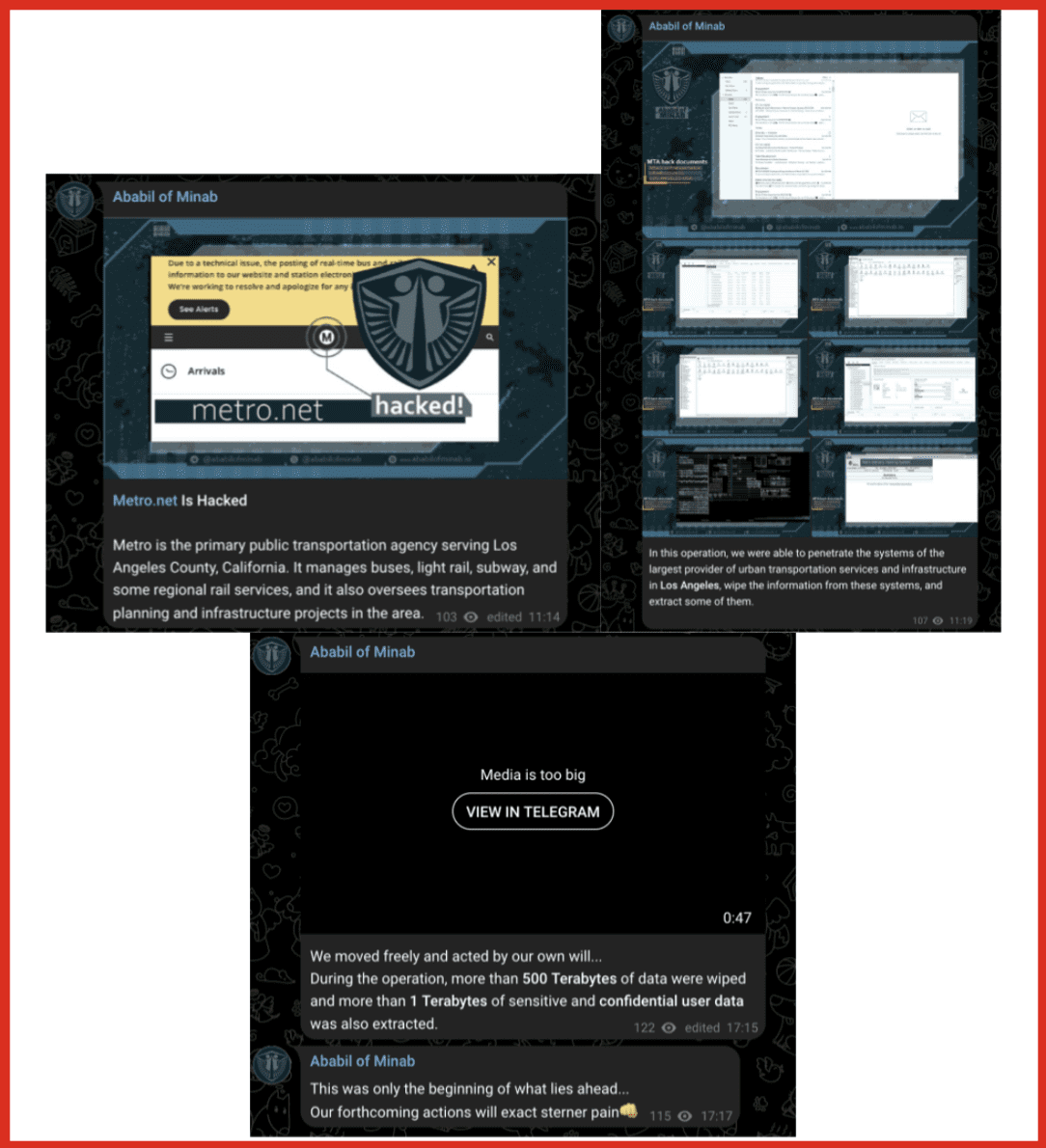
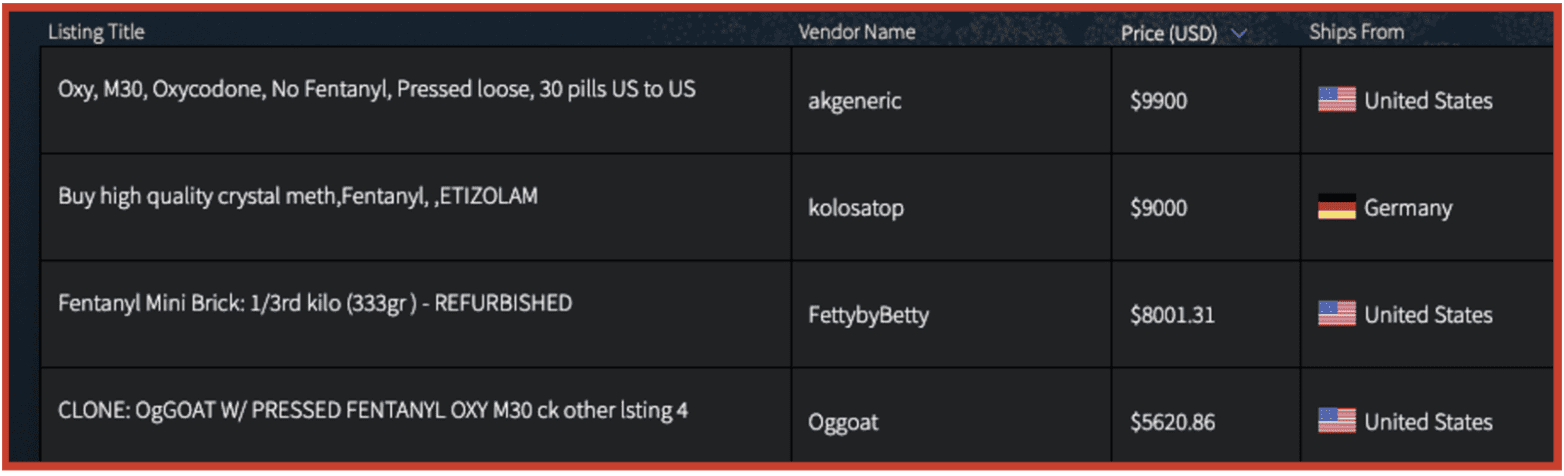
This same dynamic is evident in recent claims by a group calling itself “Ababil of Minab,” which has claimed responsibility for a cyber incident targeting Los Angeles Metro infrastructure. As reported by Dark Web Informer, the group used Telegram to publicize the claim, asserting large-scale data exfiltration and system disruption while providing limited verifiable evidence. While attribution remains unclear, the group’s messaging style and distribution patterns reflect characteristics observed across other Iranian-aligned or Iran-affiliated cyber personas.
Figure 22: “Ababil of Minab” Telegram posts claiming responsibility for a cyber intrusion targeting LA Metro
As with other actors in this ecosystem, the framing of the operation emphasizes scale and impact, including claims of hundreds of terabytes of data being wiped and additional sensitive data extracted. This reflects a recurring dynamic in which perceived significance is amplified through messaging rather than confirmed technical outcomes. This interpretation is consistent with emerging reporting on Iran-linked hybrid activity, where analysts have noted coordination across pro-Iranian online ecosystems and raised questions about the authenticity of some groups operating within them.
Conclusion
Harakat Ashab al-Yamin al-Islamia has emerged rapidly, but its fragmented Telegram presence, recycled media, and overlap with Iranian-aligned channels complicate its assessment as a standalone organization.
Instead, it is best understood as part of a broader ecosystem in which content is circulated, repurposed, and reinforced across multiple actors. In this environment, attribution becomes less about identifying a single origin point and more about understanding how narratives move across channels.
This model allows new entities to project visibility and claim relevance without demonstrating sustained operational capability, blurring the line between coordinated activity and opportunistic amplification.
As this ecosystem evolves, tracking how new entities emerge, gain visibility, and integrate into existing networks will remain critical to assessing how influence and perceived operational reach are constructed within these networks.