2024 Security Threats in Review
January 09, 2025
As we look back at 2024, the cybersecurity landscape has become ever more complicated and perilous. Last year brought a continual onslaught of cyberattacks from increasingly sophisticated adversaries and a keep-up-if-you-can rush to deal with newly emerging vulnerabilities. It’s clear that no sector is immune from cyber threats.
From AI-driven scams to the breaches of critical infrastructure, the past year has once more shown that we are all part of the same cyber history. In some of these big incidents, there are dark lessons to learn for 2025.
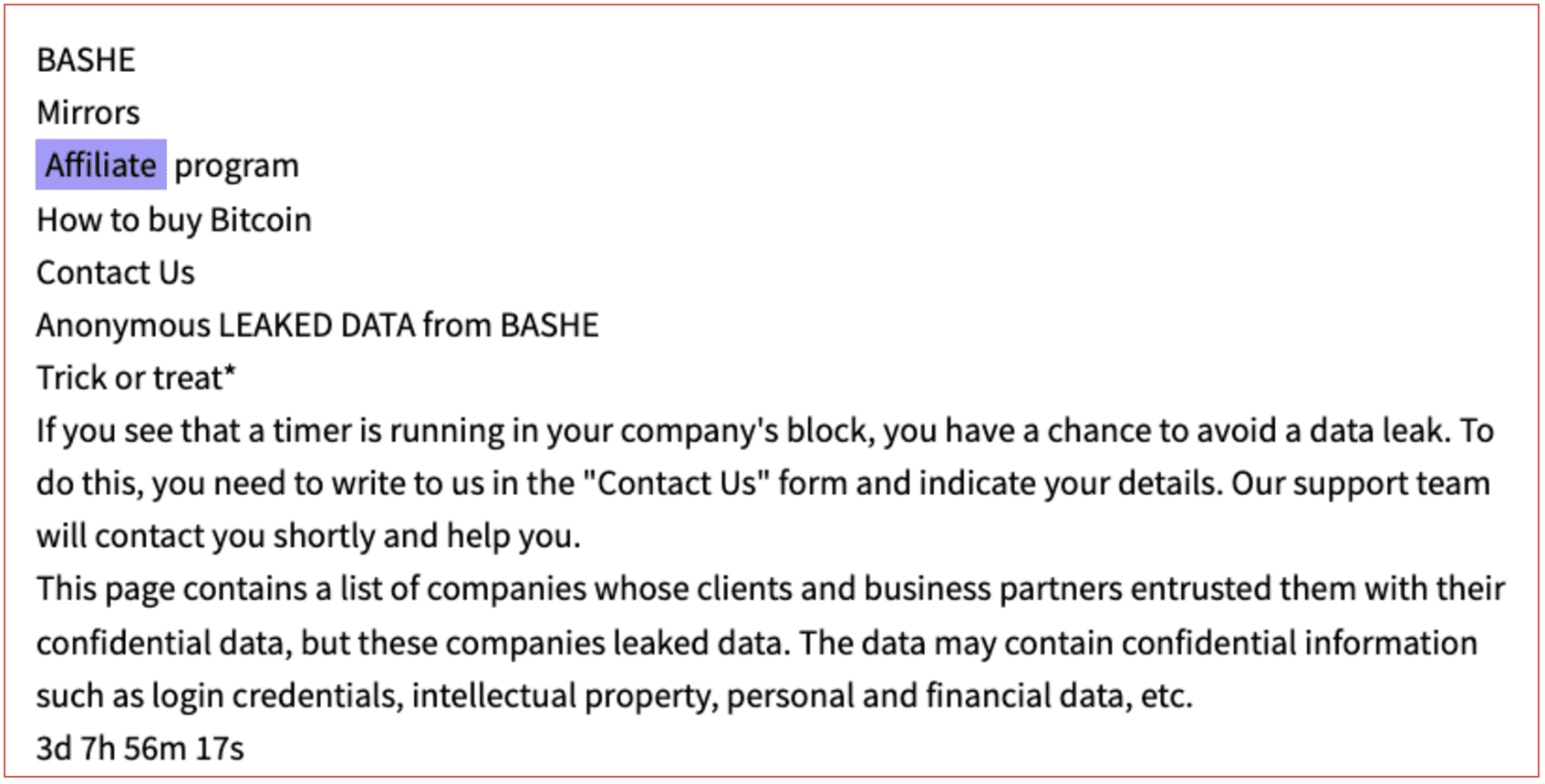
Ransomware: Still the Dominant Threat
Ransomware was still one of the most widespread and harmful cyber threats in 2024, with cybercriminals going after organizations in all sectors regardless of size. They used ransomware to extort money, take selected operations hostage, and sometimes demand ridiculously high payments. However, the most significant incident of the year was not one of these smaller hits but rather a direct assault on Change Healthcare, a major provider of healthcare IT solutions. When they finished with the ransomware part of the job (which is what criminals often do), the cyber attackers stole lots of sensitive medical data.
Just recently in December, Krispy Kreme experienced a major ransomware attack. It brought online ordering to an abrupt stop in several U.S. regions. Just as a new segment of society was embracing cozy conditions for in-store holiday shopping and ordering sweet treats from the drive-thru, the company hit the brakes on certain critical online ordering operations until it could bring them back up safely.
Ransomware has been the predominant cybercrime story for the past few years. But it is increasingly overshadowed by another tale: AI-driven cyberattacks
AI-Driven Cyber Attacks: A Double-Edged Sword
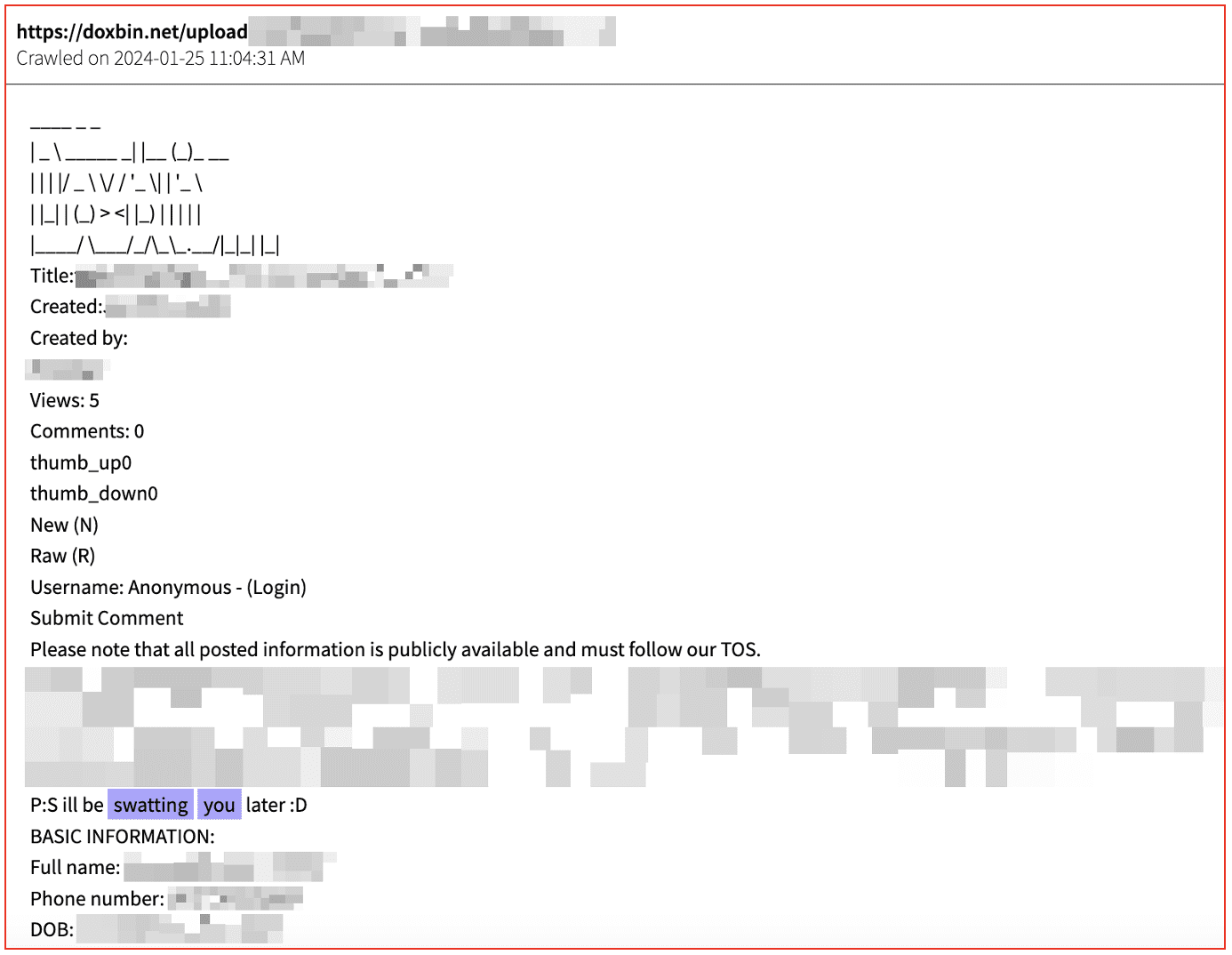
AI-driven cyberattacks are quickly emerging as the next big frontier in “what hackers are up to.” For instance, deepfake technology advanced to such a level that it began to cause unease. Videos and audio with the voices of top executives created by AI convincingly tricked organizations into making unauthorized transactions, and the resultant data breaches were some of the biggest in recent history. Meanwhile, malware powered by similarly advanced AI posed a new challenge, as threat actors now had a polymorphic, or constantly changing, set of programs to use against us. These incidents have brought organizations to the point where implementing AI-based defensive tools and training among employees is inevitable in identifying these advanced scams and phishing attempts. This year has shown that to counter AI-enabled threats, the defenders will also have to tap into the power of AI themselves.
Critical Infrastructure Breaches: A Stark Warning
New trends in targeting key infrastructure were front and center to demonstrate what many consider worrisome developments for 2024: the exploitation of security holes by nation-state actors and cybercriminals—half a world away and right here in the U.S.—with potentially disastrous consequences for national security and public safety. In September, the Chinese-linked “Salt Typhoon” went after top U.S. telecom companies, like AT&T and Verizon, to compromise systems used in judicial wiretapping; a thoroughly alarming breach of national security. The health sector has suffered greatly, with ransomware assaults on hospitals disrupting patient care and cybercriminals targeting what has been described as “fragile medical systems.” These breaches have raised the alarm about the urgent need for a public-private partnership in “hardening” critical infrastructure. These breaches underlined the need for a public-private partnership in securing critical infrastructure. Regular penetration testing, detailed incident response planning, and coordination between governments and private organizations are needed to meet any other future risks.
Cloud Security Challenges: Missteps and Vulnerabilities
Meanwhile, as organizations continue to move more into the Cloud, two trouble spots have emerged: misconfiguration and defective APIs. The significant breaches brought attention to the dangers of adopting the Cloud, especially in places with little oversight.
Snowflake was among the most popular cloud providers in one of the year’s largest incidents. The hackers accessed customer accounts using the stolen credentials, compromising companies like Advance Auto Parts and LendingTree. This breach exposed weaknesses in credential management and underlined the need for stricter security controls. The increased adoption of multi-cloud strategies further complicated the security landscape. Organizations needed help maintaining visibility across platforms, creating gaps that attackers exploited to access sensitive data. These challenges highlighted the need for robust monitoring tools, encrypted storage, and access controls to safeguard cloud environments.
Supply Chain Attacks: Finding the Weakest Link
Supply chain vulnerabilities continued to be one of the major problems for organizations in 2024 because attackers had been leveraging relationships with third-party suppliers and vendors to gain access. The consequences of such an attack trickled across industries, underlining how modern cybersecurity risks are interconnected.
Early in the year, a ransomware attack knocked services offline and spilled sensitive medical data on millions of patients at Change Healthcare. Attackers also targeted open-source software, embedding malicious code in popular libraries and spreading their reach to innumerable organizations. These incidents have brought out the dire need for stringent vendor assessment, constant monitoring of third-party systems, and an incident response mechanism implemented quickly. Supply chains have become high priorities to protect as attackers increasingly make them a key entry point.
The Talent Crisis: An Overlooked Threat
The number and complexity of cyberattacks are rising, but the cybersecurity workforce is not growing fast enough to keep pace. With a talent shortage further stretched by high-stress levels and even burnout among cybersecurity professionals, organizations of all sizes are more exposed than ever to the myriad threats that come at them daily. And the most defenseless ones are often the same smaller and medium-sized businesses that have the fewest resources to help compete for the top people in the cybersecurity field.
Numerous firms have embraced automation and shifted to managed security services to counter the shortage of cybersecurity professionals. Although the software issues created by Crowdstrike highlight the risks that having such a dependence can have. However, alleviating the talent crisis will require more than those stopgap measures. What would certainly work against that talent crisis has to do with a variety of things: multiple investments in education, training programs, and workforce development; equally, it requires attention and action regarding mental health and the promotion of better quality of work-life balance in cybersecurity professions.
Taking Lessons from Cybersecurity in 2024
The past year has been a harsh reminder of how far we still must go in the fight against cyber threats. Ransomware once again proved to be a relentless force, hitting businesses across every industry. High-profile incidents at Change Healthcare and Krispy Kreme exposed the weaknesses of outdated systems and the devastating impact of operational disruptions.
Artificial intelligence brought a new dimension to cybersecurity as a weapon and a shield. Attackers used AI to create deepfake scams and more advanced malware, while defenders scrambled to adapt, integrating AI tools and training employees to recognize new types of attacks. The race to stay ahead of AI-driven threats will define the battles of 2025.
Critical infrastructure breaches were among the year’s most alarming developments. Nation-state actors targeted telecommunications and healthcare systems, exposing vulnerabilities and jeopardizing public safety and national security. These events reinforced the need for stronger partnerships between governments and private companies to protect essential systems.
Cloud security remained a persistent weak point. Misconfigurations and credential mishandling led to breaches like the Snowflake incident, affecting companies like LendingTree. As organizations expand into multi-cloud environments, they must focus on better oversight, stronger controls, and improved employee training.
Supply chain attacks highlighted another growing danger. Attackers exploited third-party relationships to breach countless organizations. These incidents served as a warning: companies need stricter vendor assessments and constant monitoring of external systems to protect their own.
Amid these challenges, the cybersecurity workforce faced a worsening talent crisis. Many teams were overburdened, understaffed, and unable to keep pace with the volume and complexity of threats. Addressing this gap will require investments in education, workforce training, and improving the quality of life for cybersecurity professionals.
2024 made one clear: our cyber threats are evolving faster than ever. Ransomware continues to dominate. AI has become both a powerful ally and a dangerous adversary. Our critical infrastructure, cloud environments, and supply chains remain vulnerable. And the workforce tasked with defending against these threats is stretched thin.