2025 – A Year of Constant Upheaval on the Dark Web
XSS, BreachForums, and the Age of Exit Scams
January 15, 2026
If you watched the dark web ecosystem in 2025, like DarkOwl does, you may have noticed that it seemed very unstable. While the dark web is notorious for being unstable with onion sites often going up and down, this year felt different – with more permanent changes to mature and established sites and a seemingly revolving door of admins.
Long-running drug markets vanished overnight in coordinated international operations. Fraud and hacking forums were seized and marked with law enforcement seals. Others simply went dark in classic exit scams, taking millions in crypto with them.
The most notable sites to be impacted this year were XSS – a long-standing Russian-language hub for exploits, access, and ransomware affiliates and BreachForums – the English-language epicenter of data breach leaks and credential trading, which has been subject to changes over many years but always seems to come back.
But they were only part of a much larger story that included major markets like Archetyp and Abacus, plus “shadow markets” on platforms like Telegram.
As 2026 begins, we wanted to delve into what happened in 2025: XSS, the ongoing BreachForums saga as well as review some of the major marketplace hits and exit scams, how exit scams and takedowns reshape trust in the underground and what all of this means for defenders and analysts.
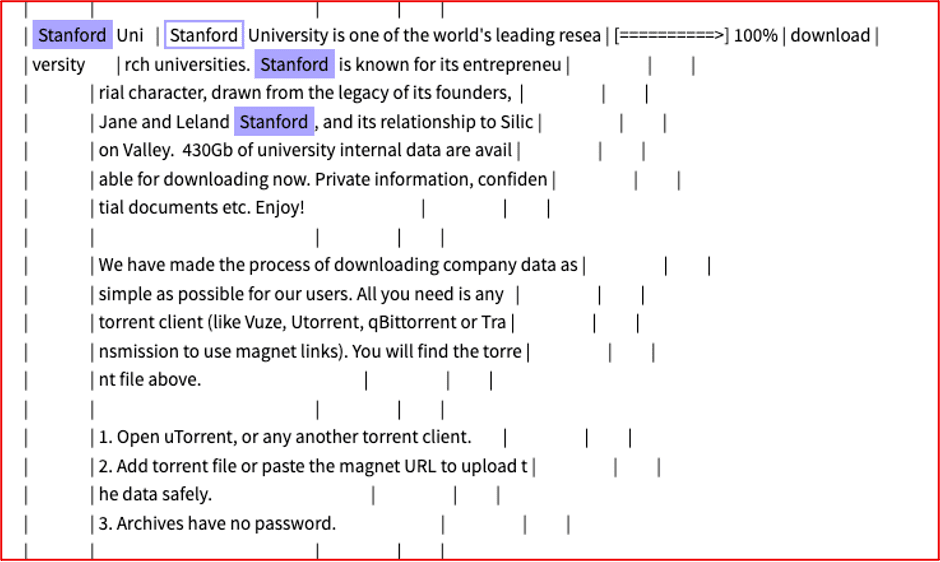
XSS
For years, XSS (formerly DaMaGeLaB) was one of the most influential Russian-language cybercrime forums. It served as a marketplace for exploits, stolen access, and malware as well as a recruiting ground for ransomware crews. A well-established site, it fostered a high-trust environment among its users, who were able to trade tools and services. The site had been operating since 2013 and was estimated to have over 50,000 registered users.
However, in mid-2025, the XSS era effectively ended. Law enforcement agencies in France and Ukraine, supported by Europol, targeted XSS after a multi-year investigation which began in 2021. This led to the arrest of a 38-year-old suspect alleged to be the main XSS administrator in Kyiv. Shortly after, the XSS domain displayed a classic law enforcement seizure banner, signaling that authorities had taken control of infrastructure and likely obtained access to backend data and communications. This marked a change for law enforcement who have typically targeted English-speaking sites on the dark web with Russian sites usually being more difficult to infiltrate.

Figure 1: XSS Seizure Notice
For a forum that catered to serious actors, including affiliates of major ransomware groups, this was a significant blow. The value of the takedown wasn’t just the shutdown, but the potential intelligence gathered, thought to include database content, private messages, transaction details, and operational. It also initially appeared to leave a void of where these actors could interact and advertise.
However, as usual, the community did not vanish with the domain, which did reappear. Some members migrated to other Russian-language forums such as Exploit or RAMP. Exploit another well-established forum appeared to be the primary forum of choice. Others attempted to relaunch XSS under slightly different branding, trying to keep the reputation and user base intact. However, the registration for new users proved challenging, and many commentators online felt that XSS was now a honeypot run by law enforcement. It appeared that many in the community were reticent to continue using the updated site.
The net effect, XSS as a brand is fractured, but the underlying actors remain active and mobile on other forums. For cyber security analysts, the center of gravity moved, but the threat did not disappear. The game of wack-a-mole continues.
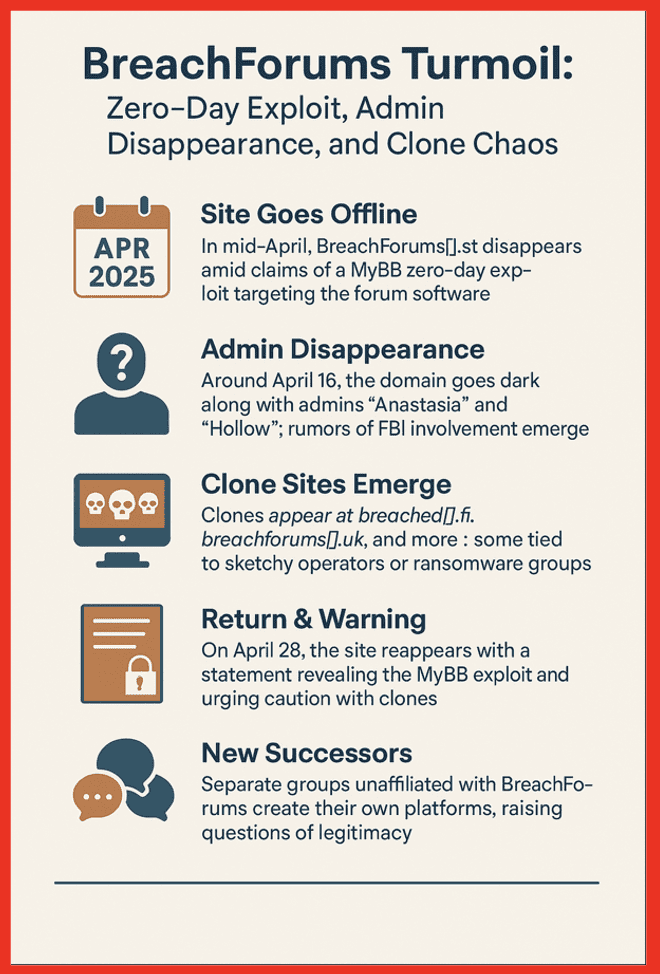
BreachForums
On the English-speaking side, BreachForums has been the high-profile home for many years, having launched around 2022 in the aftermath of the RaidForums seizure. The site was known primarily for selling and sharing data breach leaks, trades and giveaways of credential dumps as well as the discussion of hacks, access sales, and “clout” postings.
Since then, BreachForums has been stuck in a loop.

BreachForums v1 (breached / breached.vc, etc.) – launched after RaidForums was seized, was itself later taken offline after the arrest of its founder “Pompompurin” (Conor Fitzpatrick). Fitzpatrick was subsequently charged, and rumors swirled that the site was operating as a honeypot.
In September 2025, founder Conor Fitzpatrick was re-sentenced to a longer prison term after an appeals court deemed the original sentence too lenient. That move signaled that U.S. courts view BreachForums as a serious, high-impact cybercrime platform, not just a “kids swapping databases” site.
Subsequent versions of BreachForums followed the same pattern. New domains and infrastructure spun up (e.g., breachforums[.]st) quickly, claiming to be the successor and controlled by affiliates of previous versions. The community reconvened, often with familiar staff and leak actors (including groups like ShinyHunters). However, law enforcement seized infrastructure again, posting FBI banners on front-end domains and, in some cases, gaining access to backend data and user logs.
However, in 2025, a few milestones stood out as different to the pattern, and the activity appeared to occur much more rapidly than it had with previous iterations.
One BreachForums instance announced it was closing after operators claimed law enforcement had exploited a 0-day in MyBB (their forum software) to gain access. Whether this was accurate or an excuse, the result was the same: another dead forum, more scattered users. Yet another BreachForums-branded domain displayed an FBI seizure notice, underscoring that law enforcement was tracking the brand as much as the infrastructure.
Honeypot or Home?
Every new BreachForums revival faces the same dilemma, If it’s real, it’s a prime target. If it’s not real, it might be a honeypot or undercover operation. This creates a deep trust problem inside the community.
So, while BreachForums keeps coming back in some form, each iteration is more paranoid, more fragmented, and less trusted than the last. Because of that, similar to XSS we have seen the community seek other sites as refuge from the law enforcement action and fear of honeypots. In 2025, a clear front runner has been Dark Forums. However, this site has also already experienced changes in management as well as technical issues leading to downtime as well as changes in domains.
Seizures vs. Slow-Motion Exit Scams
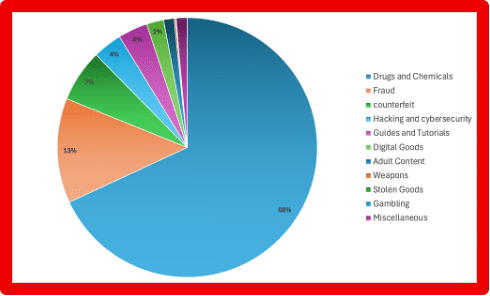
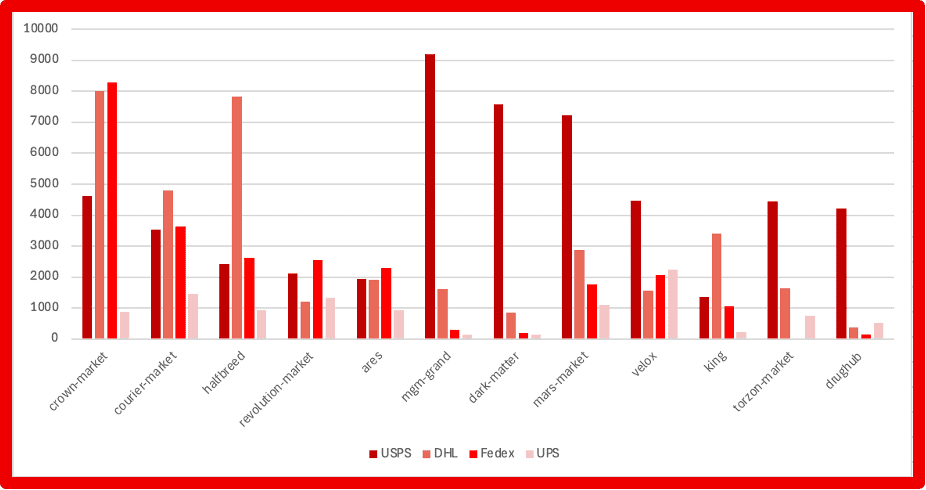
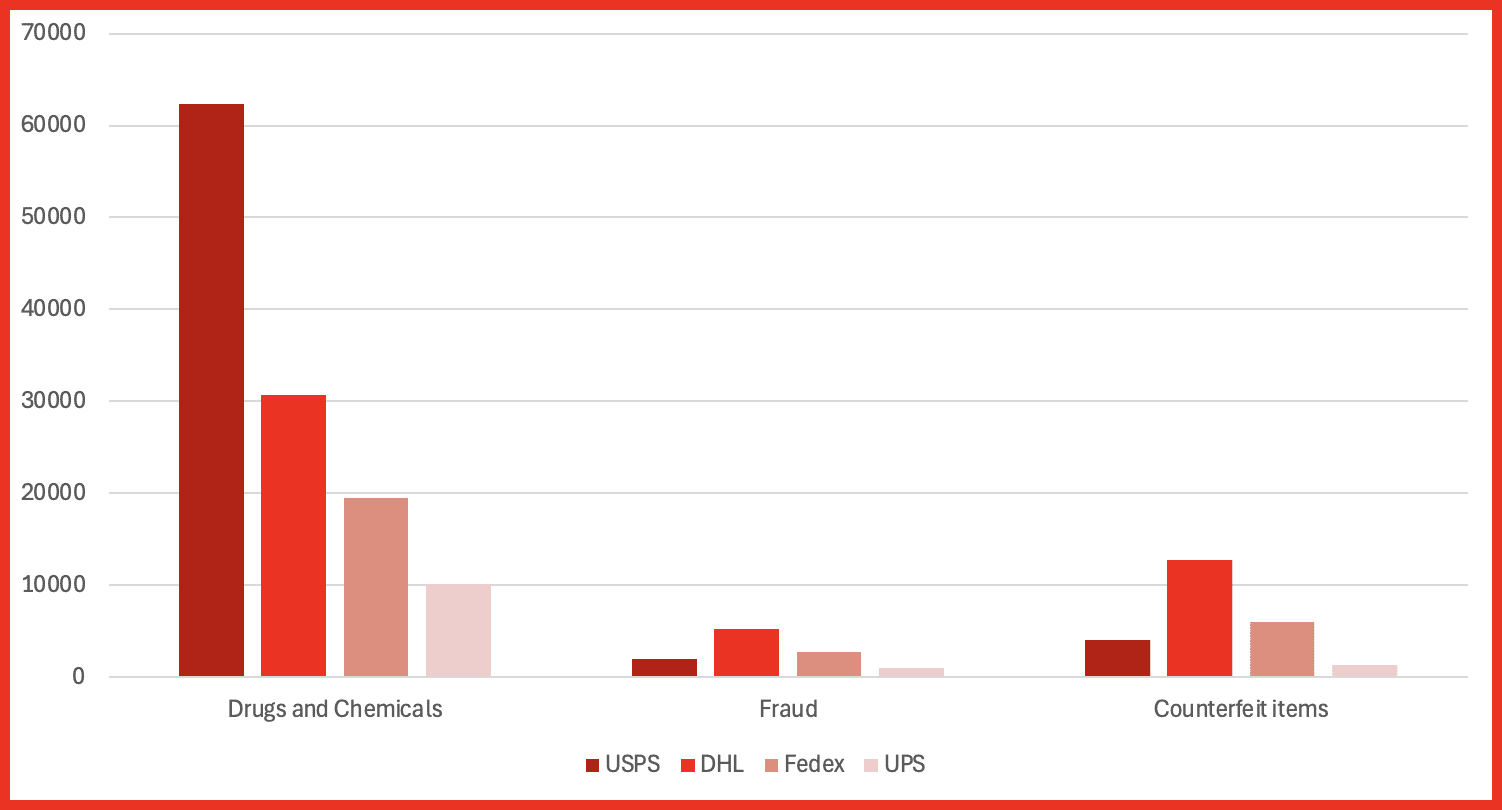
Beyond forums, darknet marketplaces remain a central pillar of the underground economy, especially for drugs, fraud services, and stolen data. In 2025, they were hammered from both sides.
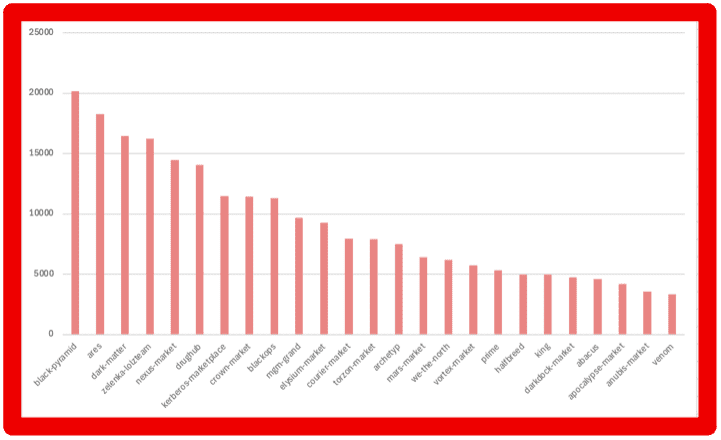
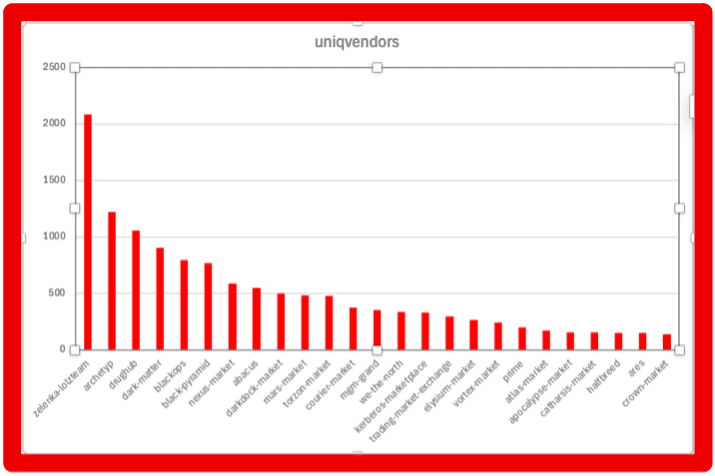
Archetyp Market
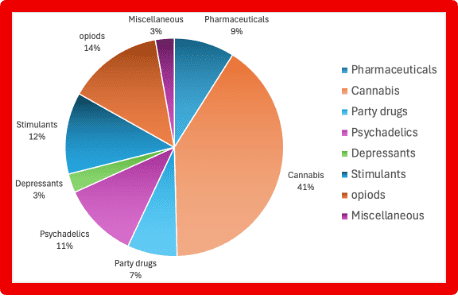
Archetyp Market was first seen in May 2020 and quickly became one of the largest drug markets operating. It specialized in the sale of drugs, including high risk substances such as fentanyl. The site required registration and accepted funds via the “privacy” cryptocurrency Monero. With over 600,000 users and 3,200 vendors, the market facilitated transactions involving cocaine, meth, MDMA, and other narcotics. By its final days, it had moved an estimated $250–290 million in illicit goods, making it a titan among darknet marketplaces.
From June 11–13, 2025, Operation Deep Sentinel, led by Germany’s BKA and supported by Europol, Eurojust, Homeland Security Investigation (HSI) and law enforcement from five other countries, executed a coordinated takedown. Servers were seized in the Netherlands, digital assets frozen, and the suspected site administrator, a 30-year-old German, was arrested in Barcelona. In addition, authorities confiscated millions in cryptocurrency, luxury vehicles, phones, and drugs in sweeping raids.
This followed a familiar pattern from earlier eras: Silk Road, AlphaBay, Hansa, Hydra. Each time, a flagship market becomes large and visible enough international law enforcement teams invest the time and resources to take it down.
Abacus Market
In contrast to Archetyp’s law enforcement takedown, Abacus Market appears to have chosen the exit-scam route. An exit scam occurs when the administrators of a site close it down and, in the process, steal funds that they are holding in escrow from their customers and vendors.
Abacus had, by many accounts, become one of the highest-earning Western darknet markets in 2025. Then the warning signs started; users began reporting withdrawal delays and stuck balances. At the time admins blamed technical problems, DDoS attacks (distributed denial of service attack), and onboarding chaos from refugees fleeing other shut-down markets.
However, over time, more evidence pointed to a classic rug pull: no seizure banner, no official statement—just vanished infrastructure and a lot of missing crypto.
By mid-2025, most analysts agreed Abacus had exit-scammed, likely taking a substantial share of user balances and escrowed payments with it.
Takedowns vs. Exit Scams
From the average user’s perspective, the result of both scenarios looks the same; one day the site works, the next day it doesn’t—and your coins are gone. However, the implications are very different.
In a Law enforcement takedown scenario. Agencies aim to identify operators, seize servers, and collect evidence. This means that you will often see official seizure banners on the site, indicating that it has been taken down and by who. Law enforcement wants the users of the site to know that they have acted and view it as a warning to others. Increasingly, law enforcement has accessed the registered users of these sites to warn them that they are participating in criminal activity to try and dissuade users from continuing this activity.
For participants, that means risk doesn’t end when the site goes down; it may only be starting. Data recovered in 2025 can fuel cases and investigations for many years.
In an exit scam, the admins’ primary objective is to take as much money as possible and disappear. Early warning signs can include:
- “Temporary” withdrawal freezes
- Sudden policy changes around escrow and wallet management
- Increasingly vague or aggressive communication from staff
Unlike with law enforcement action, there is no public banner and usually no immediate arrests—just silence.
Legally, the admin’s exposure doesn’t change much: they were already running an illegal market. But for users, the fallout is more about financial loss and fractured trust, rather than immediate deanonymization through seized databases.
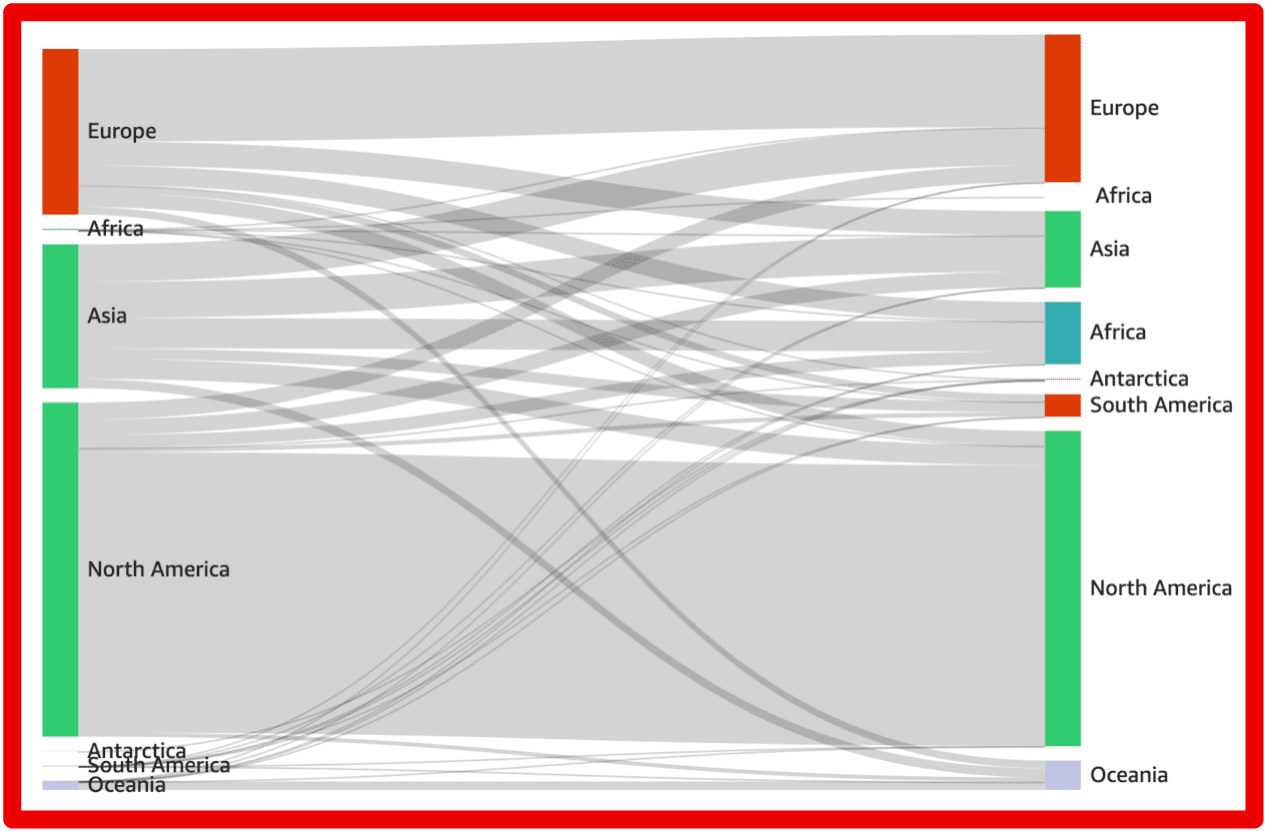
In both cases though, the users of the sites will have to find a new home to conduct their illegal trades and communities.
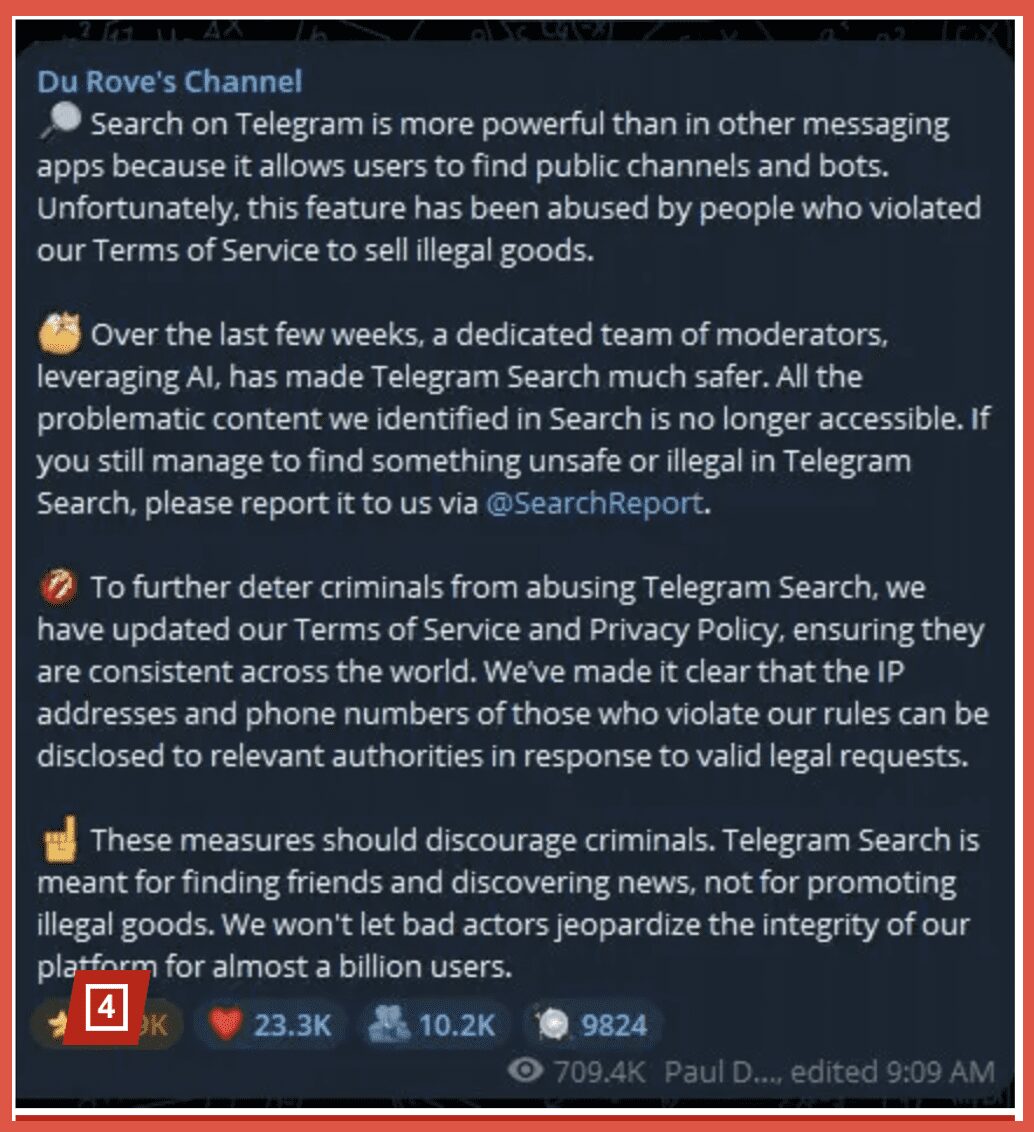
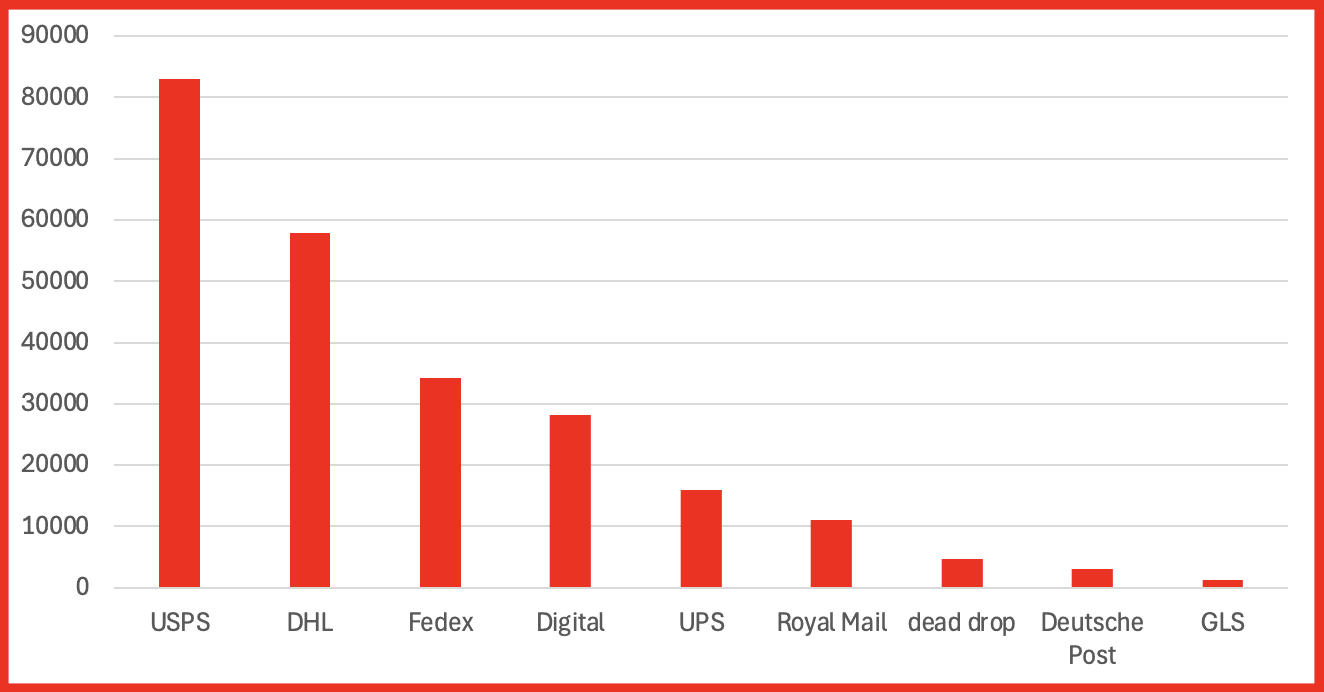
Beyond Tor: Platform Crackdowns and Shadow Markets
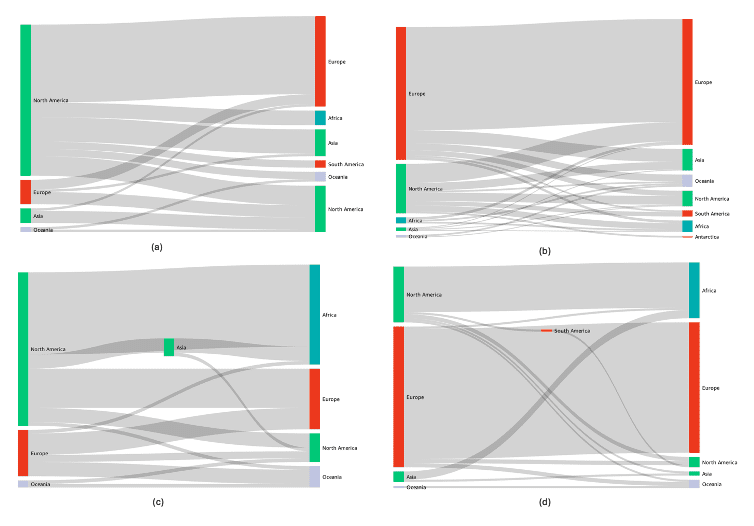
While Tor-based marketplaces and forums grab headlines, 2025 also highlighted another front, shadow markets built on mainstream platforms. DarkOwl will often refer to these sites as dark web adjacent, as they are used by the same actors for illegal activity but don’t actually exist on the dark web technology.
A notable example was the crackdown of channels associated with the underground ecosystem on Telegram. After the arrest of Telegram’s CEO in late 2024, the platform began to increase its moderation of the app, actively banning and suspending channels which it alleged were breaking their terms and conditions. This was not solely focused on markets on Telegram but was wide ranging.
These bans have had an impact on the market side of telegram particularly fraud services, laundering, and illicit financial services which were run via channels and bots.
Telegram’s enforcement actions—including mass bans and account purges—disrupted what analysts described as a multi-billion-dollar illicit economy.
This illustrates a broader trend – crime is platform-agnostic. When Tor markets are unstable, actors move to, encrypted messaging apps (Telegram, Signal, Threema), private Discord servers and niche forums and invite-only groups or even surface web sites. As TOR becomes more unstable and more likely to be disrupted by law enforcement action many actors favor a simpler way of setting up their businesses.
For cyber security analysts, focusing solely on .onion sites risks missing a big slice of activity that’s happening on “regular” platforms. This is why DarkOwl monitors not just the dark web but also dark web adjacent sites.
Is the Dark Web Still Important?
Given all the takedowns and scams, is the dark web actually shrinking?
The short answer is no, not really. There is still a huge amount of criminal activity taking place on the dark web and it is important to track and monitor this activity to protect yourself and your organization and to combat crime. However, it is also important to acknowledge that the dark web is becoming more fragmented, less stable, and much harder to trust and therefore harder to track.
Some key trends DarkOwl noted in 2025:
Shorter Lifespans
Long-lived giants like XSS and Archetyp are being removed or compromised. New markets and forums:
- Launch quickly
- Hit critical mass
- Either get seized or exit-scam once the risk feels too high
That constant churn makes it harder to operate large-scale, long-term criminal infrastructure.
Exit Scams Are “Priced In”
Vendors and buyers increasingly assume every market will die. Meaning that they
- They keep smaller balances in market wallets.
- They distribute activity across multiple platforms.
- They rely more heavily on out-of-band communication (e.g., direct contact over Telegram) and reputation that travels across sites.
Exit scams hurt, but they are no longer surprising.
Forums Are Critical—and Dangerous
Forums like XSS and BreachForums played a key role in:
- Announcing new markets
- Arbitrating disputes
- Establishing trust and reputations
But this made them and sites like them prime targets for:
- Seizure and infiltration
- Undercover operations
- Intelligence collection on active and prospective offenders
By 2025, many actors treat high-profile forums as necessary but risky.
Investigators Are Playing the Long Game
The XSS takedown and BreachForums sentencing are reminders that investigations often span multiple years before going public. Sentencing can be revisited and made harsher as courts and prosecutors recalibrate how serious digital crimes are. And that Law-enforcement agencies are increasingly comfortable with crypto tracing, infiltration, and complex international joint operations.
The underground can adapt quickly, but investigators are learning and iterating too.
Takeaways for Investigators, Researchers, and Policy Makers
If you follow this space for security, research, or policy, 2025 offers some clear lessons:
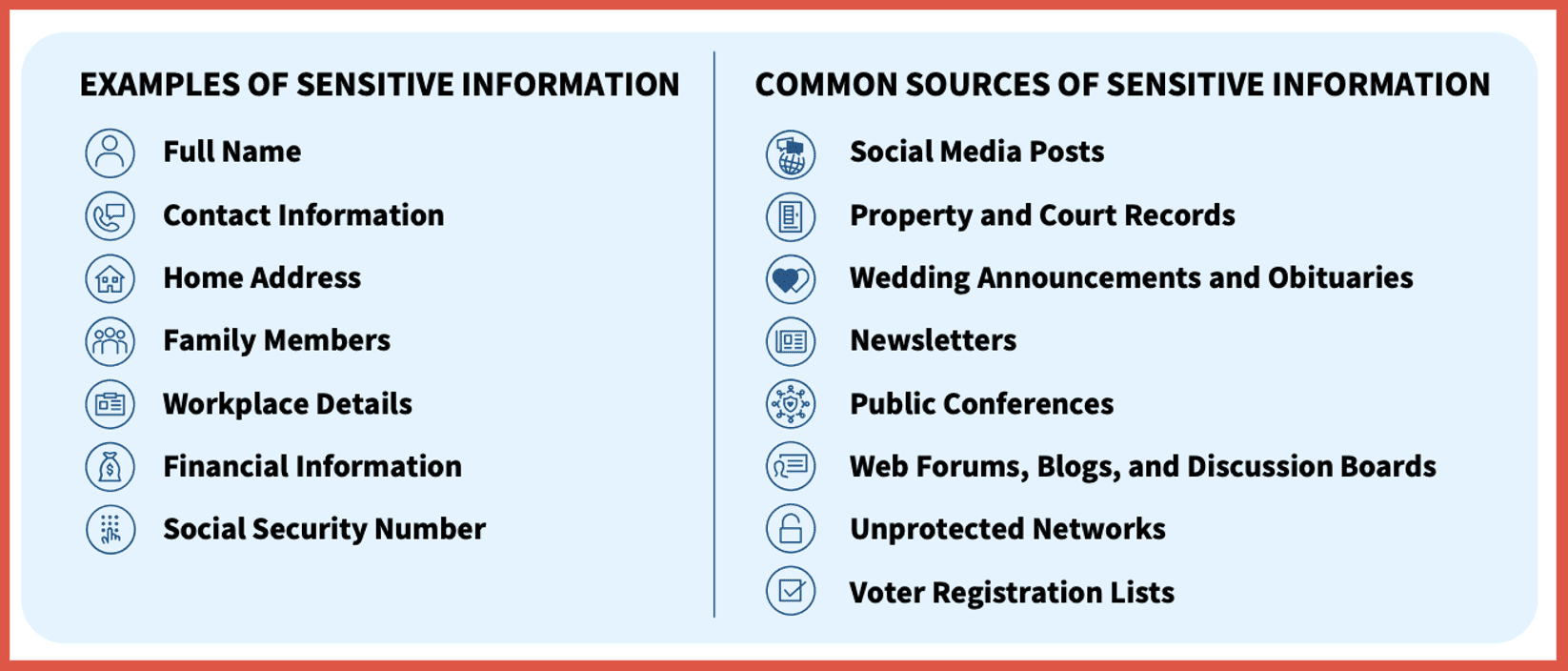
1. Follow Actors, Infrastructure and Money, Not Just Sites
Names like “XSS,” “BreachForums,” or “Abacus” come and go. But what does persist is the actors that are active on these sites, they are often working on multiple sites, and it is important to track how and if they continue to operate and what networks the operate within. One way of doing this is following the money and monitoring any wallet addresses shared and how these transactions operate across the blockchain. It is also possible to identify new an upcoming site by monitoring other sites and adjacent sites for chatter from actors, as well as identifying infrastructure patters such as hosting choices and tools used.
2. Treat Every Major Seizure as an Intelligence Event
Takedowns come with positives and negatives for investigators; on the one hand a source of intelligence has been removed. Sometimes we lose access to sites for which we have good access and are able to obtain a large amount of information that can assist with our investigations. Furthermore, the users of these sites tend to scatter, and it is a race to find the next site and where the actors we are most interested in have moved to.
On the other hand, it is great that illegal activity has been thwarted, usually leading to arrests and the seizure of infrastructure which decreases the activity. While we sometimes have to scramble to maintain oversite, the actors also have to scramble to find a new home which can really slow them down, plus they have the fear that they are now on the radar of law enforcement which may deter them fully from the activity. Furthermore, newly unsealed indictments can reveal OPSEC failures and tradecraft which can assist in future investigations, seizure notices and infrastructure details can feed your detections, and you can update risk assessments for actors tied to seized forums and markets.
3. Understand How Exit-Scam Risk Shapes Behavior
As exit scams become more common offenders tend to gravitate toward smaller, more “community-focused” markets. More trading moves into semi-closed spaces like invite-only Telegram channels and some actors may experiment with more robust escrow, multisig, and reputation mechanisms—but trust remains fragile. This means it can be more difficult to infiltrate and track the activity that is occurring. That has implications for everything from undercover operations to intelligence collection.
4. Look Beyond Tor
Serious illicit trade often uses a mix of different platforms, and it is important to have oversight of all of them which can include:
- Tor markets and forums
- Clearnet infrastructure (CDNs, bulletproof hosts, compromised servers)
- Encrypted messaging platforms
A defensive strategy that stops at Tor is going to miss much of the real activity.
Conclusion
2025 didn’t “end” the dark web. But it did accelerate a shift that’s been visible for years:
- Big, stable, centralized markets and forums are increasingly unsustainable.
- Law enforcement is better at seizing infrastructure and tracing crypto.
- Admins are quicker to pull the plug and disappear with user funds.
- Users are more paranoid, more fragmented, and more willing to move between platforms.
For analysts, this is both good and challenging news. The chaos slows down some criminal operations—but it also pushes activity into smaller, harder-to-observe corners of the ecosystem. DarkOwl can assist in making sure you are able to monitor all areas where illicit activity is occurring and help you track actors as they react to takedowns and exit-scams. The dark web will continue but it will evolve and to mitigate risk it is important to closely track these changes.